ATS Integration : An In-Depth Guide With Key Concepts And Best Practices
Read more


Read more

All the hot and popular Knit API resources
.webp)
Sage 200 is a comprehensive business management solution designed for medium-sized enterprises, offering strong accounting, CRM, supply chain management, and business intelligence capabilities. Its API ecosystem enables developers to automate critical business operations, synchronize data across systems, and build custom applications that extend Sage 200's functionality.
The Sage 200 API provides a structured, secure framework for integrating with external applications, supporting everything from basic data synchronization to complex workflow automation.
In this blog, you'll learn how to integrate with the Sage 200 API, from initial setup, authentication, to practical implementation strategies and best practices.
Sage 200 serves as the operational backbone for growing businesses, providing end-to-end visibility and control over business processes.
Sage 200 has become essential for medium-sized enterprises seeking integrated business management by providing a unified platform that connects all operational areas, enabling data-driven decision-making and streamlined processes.
Sage 200 breaks down departmental silos by connecting finance, sales, inventory, and operations into a single system. This integration eliminates duplicate data entry, reduces errors, and provides a 360-degree view of business performance.
Designed for growing businesses, Sage 200 scales with organizational needs, supporting multiple companies, currencies, and locations. Its modular structure allows businesses to start with core financials and add capabilities as they expand.
With built-in analytics and customizable dashboards, Sage 200 provides immediate insights into key performance indicators, cash flow, inventory levels, and customer behavior, empowering timely business decisions.
Sage 200 includes features for tax compliance, audit trails, and financial reporting standards, helping businesses meet regulatory requirements across different jurisdictions and industries.
Through its API and development tools, Sage 200 can be tailored to specific industry needs and integrated with specialized applications, providing flexibility without compromising core functionality.
Before integrating with the Sage 200 API, it's important to understand key concepts that define how data access and communication work within the Sage ecosystem.
The Sage 200 API enables businesses to connect their ERP system with e-commerce platforms, CRM systems, payment gateways, and custom applications. These integrations automate workflows, improve data accuracy, and create seamless operational experiences.
Below are some of the most impactful Sage 200 integration scenarios and how they can transform your business processes.
Online retailers using platforms like Shopify, Magento, or WooCommerce need to synchronize orders, inventory, and customer data with their ERP system. By integrating your e-commerce platform with Sage 200 API, orders can flow automatically into Sage for processing, fulfillment, and accounting.
How It Works:
Sales teams using CRM systems like Salesforce or Microsoft Dynamics need access to customer financial data, order history, and credit limits. Integrating CRM with Sage 200 ensures sales representatives have complete customer visibility.
How It Works:
Manufacturing and distribution companies need to coordinate with suppliers through procurement portals or vendor management systems. Sage 200 API integration automates purchase order creation, goods receipt, and supplier payment processes.
How It Works:
Organizations with multiple subsidiaries or complex group structures need consolidated financial reporting. Sage 200 API enables automated data extraction for consolidation tools and business intelligence platforms.
How It Works:
Field sales and service teams need mobile access to customer data, inventory availability, and order processing capabilities. Sage 200 API powers mobile applications for on-the-go business operations.
How It Works:
Financial teams spend significant time matching bank transactions with accounting entries. Integrating banking platforms with Sage 200 automates this process, improving accuracy and efficiency.
How It Works:
Sage 200 API uses token-based authentication to secure access to business data:
Implementation examples and detailed configuration are available in the Sage 200 Authentication Guide.
Before making API requests, you need to obtain authentication credentials. Sage 200 supports multiple authentication methods depending on your deployment (cloud or on-premise) and integration requirements.
Step 1: Register your application in the Sage Developer Portal. Create a new application and note your Client ID and Client Secret.
Step 2: Configure OAuth 2.0 redirect URIs and requested scopes based on the data your application needs to access.
Step 3: Implement the OAuth 2.0 authorization code flow:
Step 4: Refresh tokens automatically before expiry to maintain seamless access.
Step 1: Enable web services in the Sage 200 system administration and configure appropriate security settings.
Step 2: Use basic authentication or Windows authentication, depending on your security configuration:
Authorization: Basic {base64_encoded_credentials}
Step 3: For SOAP services, configure WS-Security headers as required by your deployment.
Step 4: Test connectivity using Sage 200's built-in web service test pages before proceeding with custom development.
Detailed authentication guides are available in the Sage 200 Authentication Documentation.
IIntegrating with the Sage 200 API may seem complex at first, but breaking the process into clear steps makes it much easier. This guide walks you through everything from registering your application to deploying it in production. It focuses mainly on Sage 200 Standard (cloud), which uses OAuth 2.0 and has the API enabled by default, with notes included for Sage 200 Professional (on-premise or hosted) where applicable.
Before making any API calls, you need to register your application with Sage to get a Client ID (and Client Secret for web/server applications).
Step 1: Submit the official Sage 200 Client ID and Client Secret Request Form.
Step 2: Sage will process your request (typically within 72 hours) and email you the Client ID and Client Secret (for confidential clients).
Step 3: Store these credentials securely, never expose the Client Secret in client-side code.
✅ At this stage, you have the credentials needed for authentication.
Sage 200 uses OAuth 2.0 Authorization Code Flow with Sage ID for secure, token-based access.
Steps to Implement the Flow:
1. Redirect User to Authorization Endpoint (Ask for Permission):
GET https://id.sage.com/authorize?
audience=s200ukipd/sage200&
client_id={YOUR_CLIENT_ID}&
response_type=code&
redirect_uri={YOUR_REDIRECT_URI}&
scope=openid%20profile%20email%20offline_access&
state={RANDOM_STATE_STRING}2. User logs in with their Sage ID and consents to access.
3. Sage redirects back to your redirect_uri with a code:
{YOUR_REDIRECT_URI}?code={AUTHORIZATION_CODE}&state={YOUR_STATE}4. Exchange Code for Tokens:
POST https://id.sage.com/oauth/token
Content-Type: application/x-www-form-urlencoded
client_id={YOUR_CLIENT_ID}
&client_secret={YOUR_CLIENT_SECRET} // Only for confidential clients
&redirect_uri={YOUR_REDIRECT_URI}
&code={AUTHORIZATION_CODE}
&grant_type=authorization_code5. Refresh Token When Needed:
POST https://id.sage.com/oauth/token
Content-Type: application/x-www-form-urlencoded
client_id={YOUR_CLIENT_ID}
&client_secret={YOUR_CLIENT_SECRET}
&refresh_token={YOUR_REFRESH_TOKEN}
&grant_type=refresh_tokenSage 200 organizes data by sites and companies. You need their IDs for most requests.
Steps:
1. Call the sites endpoint (no X-Site/X-Company headers needed here):
Headers:
Authorization: Bearer {ACCESS_TOKEN}
Content-Type: application/json2. Response lists available sites with site_id, site_name, company_id, etc. Note the ones you need.
Sage 200 API is fully RESTful with OData v4 support for querying.
Key Features:
No SOAP Support in Current API - It's all modern REST/JSON.
All requests require:
Authorization: Bearer {ACCESS_TOKEN}
X-Site: {SITE_ID}
X-Company: {COMPANY_ID}
Content-Type: application/jsonUse Case 1: Fetching Customers (GET)
GET https://api.columbus.sage.com/uk/sage200/accounts/v1/customers?$top=10Response Example (Partial):
[
{
"id": 27828,
"reference": "ABS001",
"name": "ABS Garages Ltd",
"balance": 2464.16,
...
}
]Use Case 2: Creating a Customer (POST)
POST https://api.columbus.sage.com/uk/sage200/accounts/v1/customers
Body:
{
"reference": "NEW001",
"name": "New Customer Ltd",
"short_name": "NEW001",
"credit_limit": 5000.00,
...
}Success: Returns 201 Created with the new customer object.
1. Use Development Credentials from your registration.
2. Test with a demo or non-production site (request via your Sage partner if needed).
3. Tools:
4. Test scenarios: Create/read/update/delete key entities (customers, orders), error handling, token refresh.
5. Monitor responses for errors (e.g., 401 for invalid token).
Building reliable Sage 200 integrations requires understanding platform capabilities and limitations. Following these best practices ensures optimal performance and maintainability.
Sage 200 APIs have practical limits on data volume per request. For large data transfers:
Implement robust error handling:
Ensure data consistency between systems:
Protect sensitive business data:
Choose the right approach for each integration scenario:
Integrating directly with Sage 200 API requires handling complex authentication, data mapping, error handling, and ongoing maintenance. Knit simplifies this by providing a unified integration platform that connects your application to Sage 200 and dozens of other business systems through a single, standardized API.
Instead of writing separate integration code for each ERP system (Sage 200, SAP Business One, Microsoft Dynamics, NetSuite), Knit provides a single Unified ERP API. Your application connects once to Knit and can instantly work with multiple ERP systems without additional development.
Knit automatically handles the differences between systems—different authentication methods, data models, API conventions, and business rules—so you don't have to.
Sage 200 authentication varies by deployment (cloud vs. on-premise) and requires ongoing token management. Knit's pre-built Sage 200 connector handles all authentication complexities:
Your application interacts with a simple, consistent authentication API regardless of the underlying Sage 200 configuration.
Every ERP system has different data models. Sage 200's customer structure differs from SAP's, which differs from NetSuite's. Knit solves this with a Unified Data Model that normalizes data across all supported systems.
When you fetch customers from Sage 200 through Knit, they're automatically transformed into a consistent schema. When you create an order, Knit transforms it from the unified model into Sage 200's specific format. This eliminates the need for custom mapping logic for each integration.
Polling Sage 200 for changes is inefficient and can impact system performance. Knit provides real-time webhooks that notify your application immediately when data changes in Sage 200:
This event-driven approach ensures your application always has the latest data without constant polling.
Building and maintaining a direct Sage 200 integration typically takes months of development and ongoing maintenance. With Knit, you can build a complete integration in days:
Your team can focus on core product functionality instead of integration maintenance.
A. Sage 200 provides API support for both cloud and on-premise versions. The cloud API is generally more feature-rich and follows standard REST/OData patterns. On-premise versions may have limitations based on the specific release.
A. Yes, Sage 200 supports webhooks for certain events, particularly in cloud deployments. You can subscribe to notifications for created, updated, or deleted records. Configuration is done through the Sage 200 administration interface or API. Not all object types support webhooks, so check the specific documentation for your requirements.
A. Sage 200 Cloud enforces API rate limits to ensure system stability:
On-premise deployments may have different limits based on server capacity and configuration. Implement retry logic with exponential backoff to handle rate limit responses gracefully.
A. Yes, Sage provides several options for testing:
A. Sage 200 APIs provide detailed error responses, including:
Enable detailed logging in your integration code and monitor both application logs and Sage 200's audit trails for comprehensive troubleshooting.
A. You can use any programming language that supports HTTP requests and JSON parsing. Sage provides SDKs and examples for:
Community-contributed libraries may be available for other languages. The REST/OData API ensures broad language compatibility.
A. For large data operations:
A. Multiple support channels are available:
.webp)
Jira is one of those tools that quietly powers the backbone of how teams work—whether you're NASA tracking space-bound bugs or a startup shipping sprints on Mondays. Over 300,000 companies use it to keep projects on track, and it’s not hard to see why.
This guide is meant to help you get started with Jira’s API—especially if you’re looking to automate tasks, sync systems, or just make your project workflows smoother. Whether you're exploring an integration for the first time or looking to go deeper with use cases, we’ve tried to keep things simple, practical, and relevant.
At its core, Jira is a powerful tool for tracking issues and managing projects. The Jira API takes that one step further—it opens up everything under the hood so your systems can talk to Jira automatically.
Think of it as giving your app the ability to create tickets, update statuses, pull reports, and tweak workflows—without anyone needing to click around. Whether you're building an integration from scratch or syncing data across tools, the API is how you do it.
It’s well-documented, RESTful, and gives you access to all the key stuff: issues, projects, boards, users, workflows—you name it.
Chances are, your customers are already using Jira to manage bugs, tasks, or product sprints. By integrating with it, you let them:
It’s a win-win. Your users save time by avoiding duplicate work, and your app becomes a more valuable part of their workflow. Plus, once you set up the integration, you open the door to a ton of automation—like auto-updating statuses, triggering alerts, or even creating tasks based on events from your product.
Before you dive into the API calls, it's helpful to understand how Jira is structured. Here are some basics:
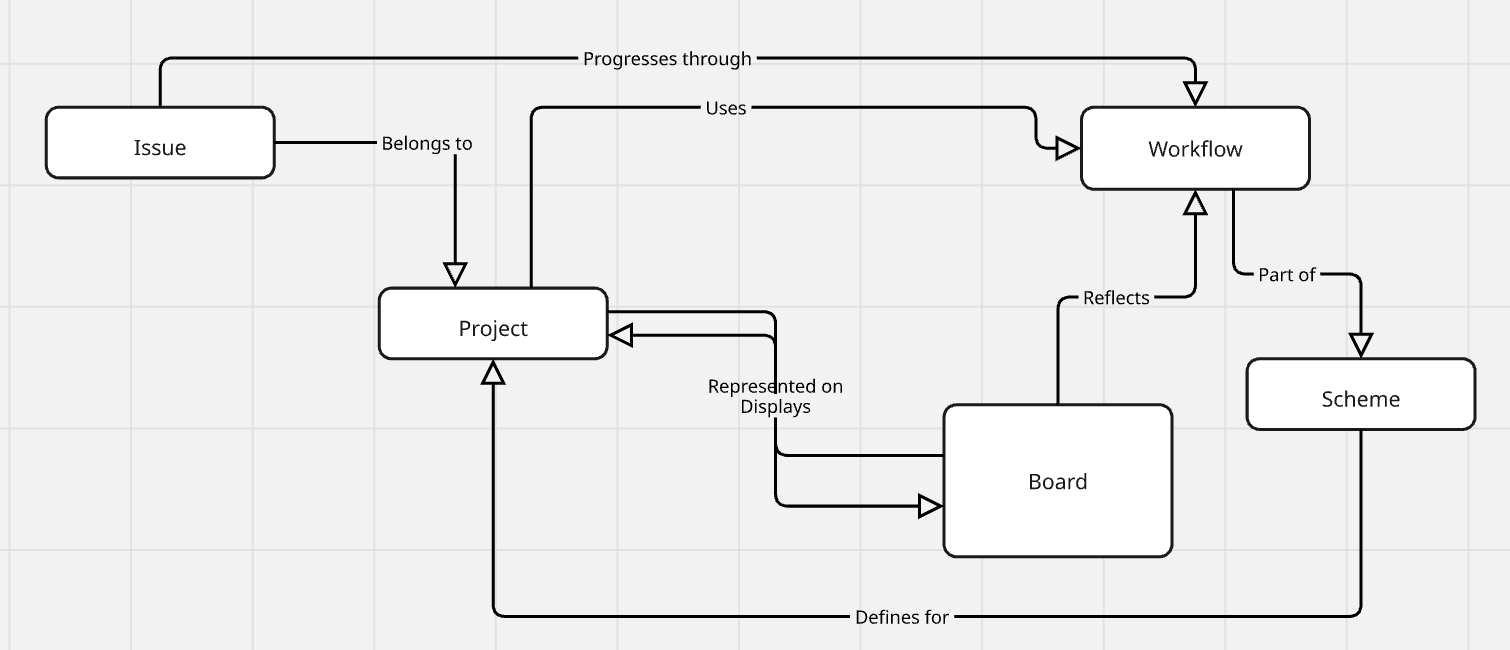
Each of these maps to specific API endpoints. Knowing how they relate helps you design cleaner, more effective integrations.
To start building with the Jira API, here’s what you’ll want to have set up:
If you're using Jira Cloud, you're working with the latest API. If you're on Jira Server/Data Center, there might be a few quirks and legacy differences to account for.
Before you point anything at production, set up a test instance of Jira Cloud. It’s free to try and gives you a safe place to break things while you build.
You can:
Testing in a sandbox means fewer headaches down the line—especially when things go wrong (and they sometimes will).
The official Jira API documentation is your best friend when starting an integration. It's hosted by Atlassian and offers granular details on endpoints, request/response bodies, and error messages. Use the interactive API explorer and bookmark sections such as Authentication, Issues, and Projects to make your development process efficient.
Jira supports several different ways to authenticate API requests. Let’s break them down quickly so you can choose what fits your setup.
Basic authentication is now deprecated but may still be used for legacy systems. It consists of passing a username and password with every request. While easy, it does not have strong security features, hence the phasing out.
OAuth 1.0a has been replaced by more secure protocols. It was previously used for authorization but is now phased out due to security concerns.
For most modern Jira Cloud integrations, API tokens are your best bet. Here’s how you use them:
It’s simple, secure, and works well for most use cases.
If your app needs to access Jira on behalf of users (with their permission), you’ll want to go with 3-legged OAuth. You’ll:
It’s a bit more work upfront, but it gives you scoped, permissioned access.
If you're building apps *inside* the Atlassian ecosystem, you'll either use:
Both offer deeper integrations and more control, but require additional setup.
Whichever method you use, make sure:
A lot of issues during integration come down to misconfigured auth—so double-check before you start debugging the code.
Once you're authenticated, one of the first things you’ll want to do is start interacting with Jira issues. Here’s how to handle the basics: create, read, update, delete (aka CRUD).
To create a new issue, you’ll need to call the `POST /rest/api/3/issue` endpoint with a few required fields:
{
"fields": {
"project": { "key": "PROJ" },
"issuetype": { "name": "Bug" },
"summary": "Something’s broken!",
"description": "Details about the bug go here."
}
}At a minimum, you need the project key, issue type, and summary. The rest—like description, labels, and custom fields—are optional but useful.
Make sure to log the responses so you can debug if anything fails. And yes, retry logic helps if you hit rate limits or flaky network issues.
To fetch an issue, use a GET request:
GET /rest/api/3/issue/{issueIdOrKey}
You’ll get back a JSON object with all the juicy details: summary, description, status, assignee, comments, history, etc.
It’s pretty handy if you’re syncing with another system or building a custom dashboard.
Need to update an issue’s status, add a comment, or change the priority? Use PUT for full updates or PATCH for partial ones.
A common use case is adding a comment:
{
"body": "Following up on this issue—any updates?"
}
Make sure to avoid overwriting fields unintentionally. Always double-check what you're sending in the payload.
Deleting issues is irreversible. Only do it if you're absolutely sure—and always ensure your API token has the right permissions.
It’s best practice to:
Confirm the issue should be deleted (maybe with a soft-delete flag first)
Keep an audit trail somewhere. Handle deletion errors gracefully
Jira comes with a powerful query language called JQL (Jira Query Language) that lets you search for precise issues.
Want all open bugs assigned to a specific user? Or tasks due this week? JQL can help with that.
Example: project = PROJ AND status = "In Progress" AND assignee = currentUser()
When using the search API, don’t forget to paginate: GET /rest/api/3/search?jql=yourQuery&startAt=0&maxResults=50
This helps when you're dealing with hundreds (or thousands) of issues.
The API also allows you to create and manage Jira projects. This is especially useful for automating new customer onboarding.
Use the `POST /rest/api/3/project` endpoint to create a new project, and pass in details like the project key, name, lead, and template.
You can also update project settings and connect them to workflows, issue type schemes, and permission schemes.
If your customers use Jira for agile, you’ll want to work with boards and sprints.
Here’s what you can do with the API:
- Fetch boards (`GET /board`)
- Retrieve or create sprints
- Move issues between sprints
It helps sync sprint timelines or mirror status in an external dashboard.
Jira Workflows define how an issue moves through statuses. You can:
- Get available transitions (`GET /issue/{key}/transitions`)
- Perform a transition (`POST /issue/{key}/transitions`)
This lets you automate common flows like moving an issue to "In Review" after a pull request is merged.
Jira’s API has some nice extras that help you build smarter, more responsive integrations.
You can link related issues (like blockers or duplicates) via the API. Handy for tracking dependencies or duplicate reports across teams.
Example:
{
"type": { "name": "Blocks" },
"inwardIssue": { "key": "PROJ-101" },
"outwardIssue": { "key": "PROJ-102" }
}Always validate the link type you're using and make sure it fits your project config.
Need to upload logs, screenshots, or files? Use the attachments endpoint with a multipart/form-data request.
Just remember:
Want your app to react instantly when something changes in Jira? Webhooks are the way to go.
You can subscribe to events like issue creation, status changes, or comments. When triggered, Jira sends a JSON payload to your endpoint.
Make sure to:
Understanding the differences between Jira Cloud and Jira Server is critical:
Keep updated with the latest changes by monitoring Atlassian’s release notes and documentation.
Even with the best setup, things can (and will) go wrong. Here’s how to prepare for it.
Jira’s API gives back standard HTTP response codes. Some you’ll run into often:
Always log error responses with enough context (request, response body, endpoint) to debug quickly.
Jira Cloud has built-in rate limiting to prevent abuse. It’s not always published in detail, but here’s how to handle it safely:
If you’re building a high-throughput integration, test with realistic volumes and plan for throttling.
To make your integration fast and reliable:
These small tweaks go a long way in keeping your integration snappy and stable.
Getting visibility into your integration is just as important as writing the code. Here's how to keep things observable and testable.
Solid logging = easier debugging. Here's what to keep in mind:
If something breaks, good logs can save hours of head-scratching.
When you’re trying to figure out what’s going wrong:
Also, if your app has logs tied to user sessions or sync jobs, make those searchable by ID.
Testing your Jira integration shouldn’t be an afterthought. It keeps things reliable and easy to update.
The goal is to have confidence in every deploy—not to ship and pray.
Let’s look at a few examples of what’s possible when you put it all together:
Trigger issue creation when a bug or support request is reported:
curl --request POST \
--url 'https://your-domain.atlassian.net/rest/api/3/issue' \
--user 'email@example.com:<api_token>' \
--header 'Accept: application/json' \
--header 'Content-Type: application/json' \
--data '{
"fields": {
"project": { "key": "PROJ" },
"issuetype": { "name": "Bug" },
"summary": "Bug in production",
"description": "A detailed bug report goes here."
}
}'Read issue data from Jira and sync it to another tool:
bash
curl -u email@example.com:API_TOKEN -X GET \ https://your-domain.atlassian.net/rest/api/3/issue/PROJ-123
Map fields like title, status, and priority, and push updates as needed.
Use a scheduled script to move overdue tasks to a "Stuck" column:
```python
import requests
import json
jira_domain = "https://your-domain.atlassian.net"
api_token = "API_TOKEN"
email = "email@example.com"
headers = {"Content-Type": "application/json"}
# Find overdue issues
jql = "project = PROJ AND due < now() AND status != 'Done'"
response = requests.get(f"{jira_domain}/rest/api/3/search",
headers=headers,
auth=(email, api_token),
params={"jql": jql})
for issue in response.json().get("issues", []):
issue_key = issue["key"]
payload = {"transition": {"id": "31"}} # Replace with correct transition ID
requests.post(f"{jira_domain}/rest/api/3/issue/{issue_key}/transitions",
headers=headers,
auth=(email, api_token),
data=json.dumps(payload))
```Automations like this can help keep boards clean and accurate.
Security's key, so let's keep it simple:
Think of API keys like passwords.
Secure secrets = less risk.
If you touch user data:
Quick tips to level up:
Libraries (Java, Python, etc.) can help with the basics.
Your call is based on your needs.
Automate testing and deployment.
Reliable integration = happy you.
If you’ve made it this far—nice work! You’ve got everything you need to build a powerful, reliable Jira integration. Whether you're syncing data, triggering workflows, or pulling reports, the Jira API opens up a ton of possibilities.
Here’s a quick checklist to recap:
Jira is constantly evolving, and so are the use cases around it. If you want to go further:
- Follow [Atlassian’s Developer Changelog]
- Explore the [Jira API Docs]
- Join the [Atlassian Developer Community]
And if you're building on top of Knit, we’re always here to help.
Drop us an email at hello@getknit.dev if you run into a use case that isn’t covered.
Happy building! 🙌
.webp)
Sage Intacct API integration allows businesses to connect financial systems with other applications, enabling real-time data synchronization and reducing errors and missed opportunities. Manual data transfers and outdated processes can lead to errors and missed opportunities. This guide explains how Sage Intacct API integration removes those pain points. We cover the technical setup, common issues, and how using Knit can cut down development time while ensuring a secure connection between your systems and Sage Intacct.
Sage Intacct API integration integrates your financial and ERP systems with third-party applications. It connects your financial information and tools used for reporting, budgeting, and analytics.
The Sage Intacct API documentation provides all the necessary information to integrate your systems with Sage Intacct’s financial services. It covers two main API protocols: REST and SOAP, each designed for different integration needs. REST is commonly used for web-based applications, offering a simple and flexible approach, while SOAP is preferred for more complex and secure transactions.
By following the guidelines, you can ensure a secure and efficient connection between your systems and Sage Intacct.
Integrating Sage Intacct with your existing systems offers a host of advantages.
Before you start the integration process, you should properly set up your environment. Proper setup creates a solid foundation and prevents most pitfalls.
A clear understanding of Sage Intacct’s account types and ecosystem is vital.
A secure environment protects your data and credentials.
Setting up authentication is crucial to secure the data flow.
An understanding of the different APIs and protocols is necessary to choose the best method for your integration needs.
Sage Intacct offers a flexible API ecosystem to fit diverse business needs.
The Sage Intacct REST API offers a clean, modern approach to integrating with Sage Intacct.
Note (2025): Sage Intacct has designated the XML API as legacy. All new objects and features are now released via the REST API only. The XML API remains supported for existing integrations, but new builds should use the REST API. See developer.intacct.com for the current migration guidance.
Curl request:
curl -i -X GET \ 'https://api.intacct.com/ia/api/v1/objects/cash-management/bank-acount {key}' \-H 'Authorization: Bearer <YOUR_TOKEN_HERE>'Here’s a detailed reference to all the Sage Intacct REST API Endpoints.
For environments that need robust enterprise-level integration, the Sage Intacct SOAP API is a strong option.
Each operation is a simple HTTP request. For example, a GET request to retrieve account details:
Parameters for request body:
<read>
<object>GLACCOUNT</object>
<keys>1</keys>
<fields>*</fields>
</read>Data format for the response body:
Here’s a detailed reference to all the Sage Intacct SOAP API Endpoints.
Comparing SOAP versus REST for various scenarios:
Beyond the primary REST and SOAP APIs, Sage Intacct provides other modules to enhance integration.
Now that your environment is ready and you understand the API options, you can start building your integration.
A basic API call is the foundation of your integration.
Step-by-step guide for a basic API call using REST and SOAP:
REST Example:
Example:
Curl Request:
curl -i -X GET \
https://api.intacct.com/ia/api/v1/objects/accounts-receivable/customer \
-H 'Authorization: Bearer <YOUR_TOKEN_HERE>'
Response 200 (Success):
{
"ia::result": [
{
"key": "68",
"id": "CUST-100",
"href": "/objects/accounts-receivable/customer/68"
},
{
"key": "69",
"id": "CUST-200",
"href": "/objects/accounts-receivable/customer/69"
},
{
"key": "73",
"id": "CUST-300",
"href": "/objects/accounts-receivable/customer/73"
}
],
"ia::meta": {
"totalCount": 3,
"start": 1,
"pageSize": 100
}
}
Response 400 (Failure):
{
"ia::result": {
"ia::error": {
"code": "invalidRequest",
"message": "A POST request requires a payload",
"errorId": "REST-1028",
"additionalInfo": {
"messageId": "IA.REQUEST_REQUIRES_A_PAYLOAD",
"placeholders": {
"OPERATION": "POST"
},
"propertySet": {}
},
"supportId": "Kxi78%7EZuyXBDEGVHD2UmO1phYXDQAAAAo"
}
},
"ia::meta": {
"totalCount": 1,
"totalSuccess": 0,
"totalError": 1
}
}
SOAP(Legacy) Example:
Example snippet of creating a reporting period:
<create>
<REPORTINGPERIOD>
<NAME>Month Ended January 2017</NAME>
<HEADER1>Month Ended</HEADER1>
<HEADER2>January 2017</HEADER2>
<START_DATE>01/01/2017</START_DATE>
<END_DATE>01/31/2017</END_DATE>
<BUDGETING>true</BUDGETING>
<STATUS>active</STATUS>
</REPORTINGPERIOD>
</create>Using Postman for Testing and Debugging API Calls
Postman is a good tool for sending and confirming API requests before implementation to make the testing of your Sage Intacct API integration more efficient.
You can import the Sage Intacct Postman collection into your Postman tool, which has pre-configured endpoints for simple testing. You can use it to simply test your API calls, see results in real time, and debug any issues.
This helps in debugging by visualizing responses and simplifying the identification of errors.
Mapping your business processes to API workflows makes integration smoother.
To test your Sage Intacct API integration, using Postman is recommended. You can import the Sage Intacct Postman collection and quickly make sample API requests to verify functionality. This allows for efficient testing before you begin full implementation.
Understanding real-world applications helps in visualizing the benefits of a well-implemented integration.
This section outlines examples from various sectors that have seen success with Sage Intacct integrations.
Industry
Joining a sage intacct partnership program can offer additional resources and support for your integration efforts.
The partnership program enhances your integration by offering technical and marketing support.
Different partnership tiers cater to varied business needs.
Following best practices ensures that your integration runs smoothly over time.
Manage API calls effectively to handle growth.
query, readByQuery, create, update, or delete call — query results are capped at 2,000 per call, so large datasets require multiple queries, each counting separately. Monitor your usage at Company → Admin → Usage Insights → API Usage. Higher tiers are available for additional fees — contact your Sage Intacct Customer Success Manager. Knit manages transaction volume automatically, batching requests and staying within tier limits to avoid unexpected overage charges.Security must remain a top priority.
Effective monitoring helps catch issues early.
No integration is without its challenges. This section covers common problems and how to fix them.
Prepare for and resolve typical issues quickly.
Effective troubleshooting minimizes downtime.
Long-term management of your integration is key to ongoing success.
Stay informed about changes to avoid surprises.
Ensure your integration remains robust as your business grows.
Knit offers a streamlined approach to integrating Sage Intacct. This section details how Knit simplifies the process.
Knit reduces the heavy lifting in integration tasks by offering pre-built accounting connectors in its Unified Accounting API.
This section provides a walk-through for integrating using Knit.
A sample table for mapping objects and fields can be included:
Knit eliminates many of the hassles associated with manual integration.
In this guide, we have walked you through the steps and best practices for integrating Sage Intacct via API. You have learned how to set up a secure environment, choose the right API option, map business processes, and overcome common challenges.
If you're ready to link Sage Intacct with your systems without the need for manual integration, it's time to discover how Knit can assist. Knit delivers customized, secure connectors and a simple interface that shortens development time and keeps maintenance low. Book a demo with Knit today to see firsthand how our solution addresses your integration challenges so you can focus on growing your business rather than worrying about technical roadblocks
Yes. Sage Intacct provides two API interfaces: the REST API (recommended for all new integrations, available at api.intacct.com) and the XML API (legacy, still supported but receiving no new features). The REST API uses standard HTTP verbs and OAuth 2.0 Bearer token authentication. It covers the full financial data model — customers, vendors, invoices, bills, GL accounts, and reporting objects. Knit's Unified Accounting API normalises Sage Intacct alongside QuickBooks, NetSuite, and Xero into a consistent schema, so teams build one integration rather than one per platform.
Sage Intacct enforces API transaction limits under a Performance Tier model (enforced April 2025). The default Tier 1 allows 100,000 transactions per month. Each query, readByQuery, create, update, or delete call counts as one transaction — query results are capped at 2,000 per call, so large datasets require multiple queries. Overages are charged at $0.15 per pack of 10 transactions. Monitor usage at Company → Admin → Usage Insights → API Usage. Knit manages transaction volume automatically to avoid unexpected overage charges.
The Sage Intacct REST API uses OAuth 2.0 Bearer token authentication. Register an application in the Sage Developer Portal to obtain a Client ID and Client Secret, then use the Authorization Code flow for user-delegated access. The legacy XML API uses Web Services credentials — a Sender ID, User ID, and Company ID passed in the XML request body. For new integrations, use OAuth 2.0 via the REST API. Knit handles the full OAuth flow for Sage Intacct; users authorise once and Knit manages token refresh automatically.
The REST API is Sage Intacct's current recommended interface — it uses standard HTTP verbs, JSON payloads, and OAuth 2.0 authentication. All new objects and features are released via REST only. The XML API (also called the SOAP or Web Services API) is the legacy interface — it uses XML request/response structures and Web Services credentials (Sender ID + User ID). It remains supported for existing integrations but receives no new features. New integrations should always use the REST API.
Yes — Sage Intacct provides an openly documented API available to any developer. The REST API documentation is published at developer.sage.com and the legacy XML API reference is at developer.intacct.com. Both are accessible without special partnership status, though production access requires a Sage Intacct subscription or a developer sandbox account. Some advanced modules (multi-entity consolidation, project accounting) require the corresponding Sage Intacct subscription to access via API.
Sage Intacct includes Sage Copilot, an AI assistant embedded natively in the product that proactively analyses financial data, surfaces insights, and responds to natural language queries within the application. For AI agent integrations (external tools calling Sage Intacct programmatically), the REST API provides the data layer — an external MCP server or AI agent can call Sage Intacct endpoints to retrieve invoices, GL balances, or vendor data as part of a multi-step workflow. Knit provides a unified accounting API that enables AI agents to query Sage Intacct alongside other accounting platforms through a consistent interface.
Sage Intacct provides a sandbox environment that mirrors your production account for safe testing. You can request a sandbox via the Sage Intacct Developer Portal at developer.intacct.com. If you don't have an existing Sage Intacct subscription, Sage offers a demo account at sage.com/intacct for proof-of-concept work. The sandbox uses the same API endpoints as production — note that the base URL differs slightly from production and must be configured separately in your integration. Knit might also be able provide access to a Sage Intacct sandbox for testing integrations built on the Knit platform -speak to your account manager to request for it.
.png)
In today's AI-driven world, AI agents have become transformative tools, capable of executing tasks with unparalleled speed, precision, and adaptability. From automating mundane processes to providing hyper-personalized customer experiences, these agents are reshaping the way businesses function and how users engage with technology. However, their true potential lies beyond standalone functionalities—they thrive when integrated seamlessly with diverse systems, data sources, and applications.
This integration is not merely about connectivity; it’s about enabling AI agents to access, process, and act on real-time information across complex environments. Whether pulling data from enterprise CRMs, analyzing unstructured documents, or triggering workflows in third-party platforms, integration equips AI agents to become more context-aware, action-oriented, and capable of delivering measurable value.
This article explores how seamless integrations unlock the full potential of AI agents, the best practices to ensure success, and the challenges that organizations must overcome to achieve seamless and impactful integration.
The rise of Artificial Intelligence (AI) agents marks a transformative shift in how we interact with technology. AI agents are intelligent software entities capable of performing tasks autonomously, mimicking human behavior, and adapting to new scenarios without explicit human intervention. From chatbots resolving customer queries to sophisticated virtual assistants managing complex workflows, these agents are becoming integral across industries.
This rise of use of AI agents has been attributed to factors like:
AI agents are more than just software programs; they are intelligent systems capable of executing tasks autonomously by mimicking human-like reasoning, learning, and adaptability. Their functionality is built on two foundational pillars:
For optimal performance, AI agents require deep contextual understanding. This extends beyond familiarity with a product or service to include insights into customer pain points, historical interactions, and updates in knowledge. However, to equip AI agents with this contextual knowledge, it is important to provide them access to a centralized knowledge base or data lake, often scattered across multiple systems, applications, and formats. This ensures they are working with the most relevant and up-to-date information. Furthermore, they need access to all new information, such as product updates, evolving customer requirements, or changes in business processes, ensuring that their outputs remain relevant and accurate.
For instance, an AI agent assisting a sales team must have access to CRM data, historical conversations, pricing details, and product catalogs to provide actionable insights during a customer interaction.
AI agents’ value lies not only in their ability to comprehend but also to act. For instance, AI agents can perform activities such as updating CRM records after a sales call, generating invoices, or creating tasks in project management tools based on user input or triggers. Similarly, AI agents can initiate complex workflows, such as escalating support tickets, scheduling appointments, or launching marketing campaigns. However, this requires seamless connectivity across different applications to facilitate action.
For example, an AI agent managing customer support could resolve queries by pulling answers from a knowledge base and, if necessary, escalating unresolved issues to a human representative with full context.
The capabilities of AI agents are undeniably remarkable. However, their true potential can only be realized when they seamlessly access contextual knowledge and take informed actions across a wide array of applications. This is where integrations play a pivotal role, serving as the key to bridging gaps and unlocking the full power of AI agents.
The effectiveness of an AI agent is directly tied to its ability to access and utilize data stored across diverse platforms. This is where integrations shine, acting as conduits that connect the AI agent to the wealth of information scattered across different systems. These data sources fall into several broad categories, each contributing uniquely to the agent's capabilities:
Platforms like databases, Customer Relationship Management (CRM) systems (e.g., Salesforce, HubSpot), and Enterprise Resource Planning (ERP) tools house structured data—clean, organized, and easily queryable. For example, CRM integrations allow AI agents to retrieve customer contact details, sales pipelines, and interaction histories, which they can use to personalize customer interactions or automate follow-ups.
The majority of organizational knowledge exists in unstructured formats, such as PDFs, Word documents, emails, and collaborative platforms like Notion or Confluence. Cloud storage systems like Google Drive and Dropbox add another layer of complexity, storing files without predefined schemas. Integrating with these systems allows AI agents to extract key insights from meeting notes, onboarding manuals, or research reports. For instance, an AI assistant integrated with Google Drive could retrieve and summarize a company’s annual performance review stored in a PDF document.
Real-time data streams from IoT devices, analytics tools, or social media platforms offer actionable insights that are constantly updated. AI agents integrated with streaming data sources can monitor metrics, such as energy usage from IoT sensors or engagement rates from Twitter analytics, and make recommendations or trigger actions based on live updates.
APIs from third-party services like payment gateways (Stripe, PayPal), logistics platforms (DHL, FedEx), and HR systems (BambooHR, Workday) expand the agent's ability to act across verticals. For example, an AI agent integrated with a payment gateway could automatically reconcile invoices, track payments, and even issue alerts for overdue accounts.
To process this vast array of data, AI agents rely on data ingestion—the process of collecting, aggregating, and transforming raw data into a usable format. Data ingestion pipelines ensure that the agent has access to a broad and rich understanding of the information landscape, enhancing its ability to make accurate decisions.
However, this capability requires robust integrations with a wide variety of third-party applications. Whether it's CRM systems, analytics tools, or knowledge repositories, each integration provides an additional layer of context that the agent can leverage.
Without these integrations, AI agents would be confined to static or siloed information, limiting their ability to adapt to dynamic environments. For example, an AI-powered customer service bot lacking integration with an order management system might struggle to provide real-time updates on a customer’s order status, resulting in a frustrating user experience.
In many applications, the true value of AI agents lies in their ability to respond with real-time or near-real-time accuracy. Integrations with webhooks and streaming APIs enable the agent to access live data updates, ensuring that its responses remain relevant and timely.
Consider a scenario where an AI-powered invoicing assistant is tasked with generating invoices based on software usage. If the agent relies on a delayed data sync, it might fail to account for a client’s excess usage in the final moments before the invoice is generated. This oversight could result in inaccurate billing, financial discrepancies, and strained customer relationships.
Integrations are not merely a way to access data for AI agents; they are critical to enabling these agents to take meaningful actions on behalf of other applications. This capability is what transforms AI agents from passive data collectors into active participants in business processes.
Integrations play a crucial role in this process by connecting AI agents with different applications, enabling them to interact seamlessly and perform tasks on behalf of the user to trigger responses, updates, or actions in real time.
For instance, A customer service AI agent integrated with CRM platforms can automatically update customer records, initiate follow-up emails, and even generate reports based on the latest customer interactions. SImilarly, if a popular product is running low, the AI agent for e-commerce platform can automatically reorder from the supplier, update the website’s product page with new availability dates, and notify customers about upcoming restocks. Furthermore, A marketing AI agent integrated with CRM and marketing automation platforms (e.g., Mailchimp, ActiveCampaign) can automate email campaigns based on customer behaviors—such as opening specific emails, clicking on links, or making purchases.
Integrations allow AI agents to automate processes that span across different systems. For example, an AI agent integrated with a project management tool and a communication platform can automate task assignments based on project milestones, notify team members of updates, and adjust timelines based on real-time data from work management systems.
For developers driving these integrations, it’s essential to build robust APIs and use standardized protocols like OAuth for secure data access across each of the applications in use. They should also focus on real-time synchronization to ensure the AI agent acts on the most current data available. Proper error handling, logging, and monitoring mechanisms are critical to maintaining reliability and performance across integrations. Furthermore, as AI agents often interact with multiple platforms, developers should design integration solutions that can scale. This involves using scalable data storage solutions, optimizing data flow, and regularly testing integration performance under load.
Retrieval-Augmented Generation (RAG) is a transformative approach that enhances the capabilities of AI agents by addressing a fundamental limitation of generative AI models: reliance on static, pre-trained knowledge. RAG fills this gap by providing a way for AI agents to efficiently access, interpret, and utilize information from a variety of data sources. Here’s how iintegrations help in building RAG pipelines for AI agents:
Traditional APIs are optimized for structured data (like databases, CRMs, and spreadsheets). However, many of the most valuable insights for AI agents come from unstructured data—documents (PDFs), emails, chats, meeting notes, Notion, and more. Unstructured data often contains detailed, nuanced information that is not easily captured in structured formats.
RAG enables AI agents to access and leverage this wealth of unstructured data by integrating it into their decision-making processes. By integrating with these unstructured data sources, AI agents:
RAG involves not only the retrieval of relevant data from these sources but also the generation of responses based on this data. It allows AI agents to pull in information from different platforms, consolidate it, and generate responses that are contextually relevant.
For instance, an HR AI agent might need to pull data from employee records, performance reviews, and onboarding documents to answer a question about benefits. RAG enables this agent to access the necessary context and background information from multiple sources, ensuring the response is accurate and comprehensive through a single retrieval mechanism.
RAG empowers AI agents by providing real-time access to updated information from across various platforms with the help of Webhooks. This is critical for applications like customer service, where responses must be based on the latest data.
For example, if a customer asks about their recent order status, the AI agent can access real-time shipping data from a logistics platform, order history from an e-commerce system, and promotional notes from a marketing database—enabling it to provide a response with the latest information. Without RAG, the agent might only be able to provide a generic answer based on static data, leading to inaccuracies and customer frustration.
While RAG presents immense opportunities to enhance AI capabilities, its implementation comes with a set of challenges. Addressing these challenges is crucial to building efficient, scalable, and reliable AI systems.
Integration of an AI-powered customer service agent with CRM systems, ticketing platforms, and other tools can help enhance contextual knowledge and take proactive actions, delivering a superior customer experience.
For instance, when a customer reaches out with a query—such as a delayed order—the AI agent retrieves their profile from the CRM, including past interactions, order history, and loyalty status, to gain a comprehensive understanding of their background. Simultaneously, it queries the ticketing system to identify any related past or ongoing issues and checks the order management system for real-time updates on the order status. Combining this data, the AI develops a holistic view of the situation and crafts a personalized response. It may empathize with the customer’s frustration, offer an estimated delivery timeline, provide goodwill gestures like loyalty points or discounts, and prioritize the order for expedited delivery.
The AI agent also performs critical backend tasks to maintain consistency across systems. It logs the interaction details in the CRM, updating the customer’s profile with notes on the resolution and any loyalty rewards granted. The ticketing system is updated with a resolution summary, relevant tags, and any necessary escalation details. Simultaneously, the order management system reflects the updated delivery status, and insights from the resolution are fed into the knowledge base to improve responses to similar queries in the future. Furthermore, the AI captures performance metrics, such as resolution times and sentiment analysis, which are pushed into analytics tools for tracking and reporting.
In retail, AI agents can integrate with inventory management systems, customer loyalty platforms, and marketing automation tools for enhancing customer experience and operational efficiency. For instance, when a customer purchases a product online, the AI agent quickly retrieves data from the inventory management system to check stock levels. It can then update the order status in real time, ensuring that the customer is informed about the availability and expected delivery date of the product. If the product is out of stock, the AI agent can suggest alternatives that are similar in features, quality, or price, or provide an estimated restocking date to prevent customer frustration and offer a solution that meets their needs.
Similarly, if a customer frequently purchases similar items, the AI might note this and suggest additional products or promotions related to these interests in future communications. By integrating with marketing automation tools, the AI agent can personalize marketing campaigns, sending targeted emails, SMS messages, or notifications with relevant offers, discounts, or recommendations based on the customer’s previous interactions and buying behaviors. The AI agent also writes back data to customer profiles within the CRM system. It logs details such as purchase history, preferences, and behavioral insights, allowing retailers to gain a deeper understanding of their customers’ shopping patterns and preferences.
Integrating AI (Artificial Intelligence) and RAG (Recommendations, Actions, and Goals) frameworks into existing systems is crucial for leveraging their full potential, but it introduces significant technical challenges that organizations must navigate. These challenges span across data ingestion, system compatibility, and scalability, often requiring specialized technical solutions and ongoing management to ensure successful implementation.
Adding integrations to AI agents involves providing these agents with the ability to seamlessly connect with external systems, APIs, or services, allowing them to access, exchange, and act on data. Here are the top ways to achieve the same:
Custom development involves creating tailored integrations from scratch to connect the AI agent with various external systems. This method requires in-depth knowledge of APIs, data models, and custom logic. The process involves developing specific integrations to meet unique business requirements, ensuring complete control over data flows, transformations, and error handling. This approach is suitable for complex use cases where pre-built solutions may not suffice.
Embedded iPaaS (Integration Platform as a Service) solutions offer pre-built integration platforms that include no-code or low-code tools. These platforms allow organizations to quickly and easily set up integrations between the AI agent and various external systems without needing deep technical expertise. The integration process is simplified by using a graphical interface to configure workflows and data mappings, reducing development time and resource requirements.
Unified API solutions provide a single API endpoint that connects to multiple SaaS products and external systems, simplifying the integration process. This method abstracts the complexity of dealing with multiple APIs by consolidating them into a unified interface. It allows the AI agent to access a wide range of services, such as CRM systems, marketing platforms, and data analytics tools, through a seamless and standardized integration process.
Knit offers a game-changing solution for organizations looking to integrate their AI agents with a wide variety of SaaS applications quickly and efficiently. By providing a seamless, AI-driven integration process, Knit empowers businesses to unlock the full potential of their AI agents by connecting them with the necessary tools and data sources.
By integrating with Knit, organizations can power their AI agents to interact seamlessly with a wide array of applications. This capability not only enhances productivity and operational efficiency but also allows for the creation of innovative use cases that would be difficult to achieve with manual integration processes. Knit thus transforms how businesses utilize AI agents, making it easier to harness the full power of their data across multiple platforms.
Ready to see how Knit can transform your AI agents? Contact us today for a personalized demo!
What are integrations for AI agents?
Integrations for AI agents are the connections that give an AI agent access to external data sources, APIs, and tools it needs to complete tasks. An AI agent without integrations can only work with the information in its context window - it can't read a CRM record, trigger a payroll run, or pull a customer's support history. Integrations bridge the gap between the agent's reasoning capability and the real-world systems it needs to act on. Common integration types include REST APIs (for SaaS platforms like HubSpot, Salesforce, or Workday), file storage systems, databases, and event streams. For agents built on LLMs, integrations are typically exposed as tools the model can call - either through direct API connections, an embedded iPaaS, or a unified API platform like Knit.
Why do AI agents need integrations?
AI agents need integrations for two reasons: knowledge and action. For knowledge, integrations give agents access to up-to-date, customer-specific data they can't get from their training - CRM records, HR data, support tickets, financial history. For action, integrations let agents do things beyond generating text - update a record, trigger a workflow, send a message, or write to a database. Without integrations, an AI agent is a sophisticated chatbot. With integrations, it becomes a system that can perceive context across your tech stack and take meaningful actions on behalf of users.
What is MCP and how does it relate to AI agent integrations?
MCP (Model Context Protocol) is an open standard that defines how AI models connect to external tools and data sources. Rather than every agent framework implementing its own tool-calling conventions, MCP provides a standardised protocol so that any MCP-compatible agent can use any MCP server. For AI agent integrations, this means a well-built MCP server can expose your SaaS integrations (CRM, HRIS, ticketing) to any agent framework that supports MCP - without bespoke wiring for each one. Knit provides an MCP hub that you could use for MCP servers across 150+ apps that knit supports, so agents built on Claude, GPT-4o, or any MCP-compatible framework can call Knit's 100+ HRIS, payroll, and CRM integrations through a single MCP connection.
What is the best way to add integrations to an AI agent?
There are three main approaches. Custom development gives you the most control but requires building and maintaining each integration individually - practical for one or two integrations, but it doesn't scale. Embedded iPaaS platforms (like Zapier Embedded or Workato) provide pre-built connectors with a workflow layer, which speeds up deployment but adds cost and a middleware dependency. Unified API platforms (like Knit) provide a single API endpoint that normalises data from hundreds of SaaS tools into a consistent schema - the fastest path to multi-tool coverage for agents. For 2026, unified APIs combined with MCP server support is becoming the standard architecture for production AI agents that need to act across many systems.
What are examples of integrations for AI agents?
Common AI agent integration examples include: an HR agent that reads employee data from Workday or BambooHR to answer questions about org structure, leave balances, or comp data; a sales agent that pulls deal context from Salesforce or HubSpot before drafting outreach; a support agent that retrieves ticket history from Zendesk or Intercom to provide contextual responses; a finance agent that reads invoices from accounting software like QuickBooks or NetSuite; and an onboarding agent that writes new hire records to an HRIS and provisions access in an identity provider.
What is a unified API for AI agents and why does it matter?
A unified API normalises multiple third-party APIs into a single consistent interface. Instead of building separate connectors for Workday, BambooHR, and Rippling, an AI agent calls one endpoint like GET /hris/employees and receives normalised data regardless of the underlying platform. This matters for AI agents specifically because agents often need to act across multiple systems in a single workflow - pulling an employee record from Workday, updating a ticket in Jira, and logging the action in a CRM. Without a unified API, the agent needs custom connector logic for each system, which multiplies engineering cost and maintenance burden. Knit is built specifically as a unified API for enterprise HRIS, ATS, and ERP platforms.
What are the main challenges of building integrations for AI agents?
The main challenges are: data compatibility (different SaaS tools structure the same data differently, requiring normalisation); rate limits (agents can make far more API calls per session than traditional integrations, requiring careful throttling); authentication management across many customer accounts; maintaining integrations as upstream APIs evolve; and observability - understanding exactly which integration call caused a failure in a multi-step agent workflow. Unified API platforms like Knit address these by abstracting the integration layer: one endpoint, normalised schema, managed auth, and built-in rate limit handling across all connected platforms.
How do MCP servers help AI agents access enterprise data?
MCP servers wrap enterprise APIs in a standardised tool interface that any MCP-compatible AI agent can call. The agent calls a named tool like get_employee_list or get_open_roles and the MCP server handles the underlying API call, authentication, pagination, and data transformation - without any per-platform custom code in the agent itself. Knit's MCP servers expose tools covering employees, org structure, payroll, and job profiles across 100+ HRIS and ATS platforms, all accessible from Claude, GPT, or any MCP-compatible agent through a single server connection.
.png)
In today’s fast-paced digital landscape, organizations across all industries are leveraging Calendar APIs to streamline scheduling, automate workflows, and optimize resource management. While standalone calendar applications have always been essential, Calendar Integration significantly amplifies their value—making it possible to synchronize events, reminders, and tasks across multiple platforms seamlessly. Whether you’re a SaaS provider integrating a customer’s calendar or an enterprise automating internal processes, a robust API Calendar strategy can drastically enhance efficiency and user satisfaction.
Explore more Calendar API integrations
In this comprehensive guide, we’ll discuss the benefits of Calendar API integration, best practices for developers, real-world use cases, and tips for managing common challenges like time zone discrepancies and data normalization. By the end, you’ll have a clear roadmap on how to build and maintain effective Calendar APIs for your organization or product offering in 2026.
In 2026, calendars have evolved beyond simple day-planners to become strategic tools that connect individuals, teams, and entire organizations. The real power comes from Calendar Integration, or the ability to synchronize these planning tools with other critical systems—CRM software, HRIS platforms, applicant tracking systems (ATS), eSignature solutions, and more.
Essentially, Calendar API integration becomes indispensable for any software looking to reduce operational overhead, improve user satisfaction, and scale globally.
One of the most notable advantages of Calendar Integration is automated scheduling. Instead of manually entering data into multiple calendars, an API can do it for you. For instance, an event management platform integrating with Google Calendar or Microsoft Outlook can immediately update participants’ schedules once an event is booked. This eliminates the need for separate email confirmations and reduces human error.
When a user can book or reschedule an appointment without back-and-forth emails, you’ve substantially upgraded their experience. For example, healthcare providers that leverage Calendar APIs can let patients pick available slots and sync these appointments directly to both the patient’s and the doctor’s calendars. Changes on either side trigger instant notifications, drastically simplifying patient-doctor communication.
By aligning calendars with HR systems, CRM tools, and project management platforms, businesses can ensure every resource—personnel, rooms, or equipment—is allocated efficiently. Calendar-based resource mapping can reduce double-bookings and idle times, increasing productivity while minimizing conflicts.
Notifications are integral to preventing missed meetings and last-minute confusion. Whether you run a field service company, a professional consulting firm, or a sales organization, instant schedule updates via Calendar APIs keep everyone on the same page—literally.
API Calendar solutions enable triggers and actions across diverse systems. For instance, when a sales lead in your CRM hits “hot” status, the system can automatically schedule a follow-up call, add it to the rep’s calendar, and send a reminder 15 minutes before the meeting. Such automation fosters a frictionless user experience and supports consistent follow-ups.
<a name="calendar-api-data-models-explained"></a>
To integrate calendar functionalities successfully, a solid grasp of the underlying data structures is crucial. While each calendar provider may have specific fields, the broad data model often consists of the following objects:
Properly mapping these objects during Calendar Integration ensures consistent data handling across multiple systems. Handling each element correctly—particularly with recurring events—lays the foundation for a smooth user experience.
Below are several well-known Calendar APIs that dominate the market. Each has unique features, so choose based on your users’ needs:
Applicant Tracking Systems (ATS) like Lever or Greenhouse can integrate with Google Calendar or Outlook to automate interview scheduling. Once a candidate is selected for an interview, the ATS checks availability for both the interviewer and candidate, auto-generates an event, and sends reminders. This reduces manual coordination, preventing double-bookings and ensuring a smooth interview process.
Learn more on How Interview Scheduling Companies Can Scale ATS Integrations Faster
ERPs like SAP or Oracle NetSuite handle complex scheduling needs for workforce or equipment management. By integrating with each user’s calendar, the ERP can dynamically allocate resources based on real-time availability and location, significantly reducing conflicts and idle times.
Salesforce and HubSpot CRMs can automatically book demos and follow-up calls. Once a customer selects a time slot, the CRM updates the rep’s calendar, triggers reminders, and logs the meeting details—keeping the sales cycle organized and on track.
Systems like Workday and BambooHR use Calendar APIs to automate onboarding schedules—adding orientation, training sessions, and check-ins to a new hire’s calendar. Managers can see progress in real-time, ensuring a structured, transparent onboarding experience.
Assessment tools like HackerRank or Codility integrate with Calendar APIs to plan coding tests. Once a test is scheduled, both candidates and recruiters receive real-time updates. After completion, debrief meetings are auto-booked based on availability.
DocuSign or Adobe Sign can create calendar reminders for upcoming document deadlines. If multiple signatures are required, it schedules follow-up reminders, ensuring legal or financial processes move along without hiccups.
QuickBooks or Xero integrations place invoice due dates and tax deadlines directly onto the user’s calendar, complete with reminders. Users avoid late penalties and maintain financial compliance with minimal manual effort.
While Calendar Integration can transform workflows, it’s not without its hurdles. Here are the most prevalent obstacles:
Businesses can integrate Calendar APIs either by building direct connectors for each calendar platform or opting for a Unified Calendar API provider that consolidates all integrations behind a single endpoint. Here’s how they compare:
Learn more about what should you look for in a Unified API Platform
The calendar landscape is only getting more complex as businesses and end users embrace an ever-growing range of tools and platforms. Implementing an effective Calendar API strategy—whether through direct connectors or a unified platform—can yield substantial operational efficiencies, improved user satisfaction, and a significant competitive edge. From Calendar APIs that power real-time notifications to AI-driven features predicting best meeting times, the potential for innovation is limitless.
If you’re looking to add API Calendar capabilities to your product or optimize an existing integration, now is the time to take action. Start by assessing your users’ needs, identifying top calendar providers they rely on, and determining whether a unified or direct connector strategy makes the most sense. Incorporate the best practices highlighted in this guide—like leveraging webhooks, managing data normalization, and handling rate limits—and you’ll be well on your way to delivering a next-level calendar experience.
Ready to transform your Calendar Integration journey?
Book a Demo with Knit to See How AI-Driven Unified APIs Simplify Integrations
Calendar API integration is the process of connecting your software application to a calendar platform - such as Google Calendar, Microsoft Outlook, or Apple Calendar - using that platform's API to read, create, update, and delete events programmatically. Instead of requiring users to manually copy meeting details between systems, a calendar API integration lets your product sync scheduling data directly with the user's existing calendar. For B2B SaaS products, calendar integrations are commonly used for interview scheduling in ATS tools, client meeting sync in CRM platforms, and onboarding milestone tracking in HRIS systems. Knit provides a unified Calendar API that connects your product to all major calendar platforms through a single integration.
To integrate a calendar API:
(1) Register your application with the calendar provider (Google Cloud Console for Google Calendar, Azure AD for Microsoft Graph);
(2) implement OAuth 2.0 to authenticate users and obtain access tokens scoped to calendar permissions;
(3) call the API endpoints to list, create, or update calendar events using the provider's REST API;
(4) handle webhooks or push notifications to receive real-time event changes;
(5) implement time zone normalization, since calendar APIs return timestamps in various formats. Each calendar platform has a different authentication model, event schema, and rate limit.
For products integrating multiple calendar providers, a unified calendar API layer handles per-provider differences automatically.
With a calendar API you can: read a user's upcoming events and availability windows; create new events with attendees, location, conferencing links, and reminders; update or cancel existing events; access free/busy information to find open slots for scheduling; subscribe to calendar change notifications via webhooks; and manage recurring event series including exceptions and cancellations. Calendar APIs expose the core scheduling primitives - events, attendees, reminders, recurrence rules - that power features like automated interview scheduling, appointment booking, resource allocation, and cross-platform event sync in B2B SaaS products.
Yes. Google Calendar API is free to use - there is no per-request charge and exceeding quota limits does not incur extra billing. The default quota is 1,000,000 queries per day per project, with a per-user rate limit of 60 requests per minute. For production applications with high request volumes, you can apply for a quota increase via Google Cloud Console. The Microsoft Graph Calendar API (Outlook/Microsoft 365) is similarly free to use for reading and writing calendar data, provided the end user has a valid Microsoft 365 licence. You pay for the underlying platform licences (if applicable), not for API calls themselves.
Prioritise based on your users' calendar providers. For most B2B SaaS products, start with Google Calendar API (dominant among SMB and tech-forward companies) and Microsoft Graph Calendar API (dominant in enterprise and regulated industries). Together these two cover the vast majority of business users. Apple Calendar (CalDAV-based) is worth adding if your users skew to Mac-heavy or mobile-first workflows. Zoho Calendar and Exchange on-premises matter for specific verticals. Most products build Google first, then Microsoft, then expand based on customer demand. If you want to go live with all of them at once consider a unified API like Knit that lets you integrate with all calendar apps via a single integration
Key challenges include: time zone handling - calendar events use IANA timezone identifiers and RFC 5545 recurrence rules (RRULE) that must be normalised across providers; recurring events - modifying a single instance vs. the entire series requires careful handling of exception logic; permission scopes - requesting overly broad calendar access triggers user friction during OAuth consent; rate limits - Google Calendar enforces per-user limits requiring exponential backoff; data sync inconsistencies - webhook delivery can be delayed or missed, requiring periodic polling as a fallback; and multi-provider divergence, where the event object structure differs significantly between Google, Microsoft, and Apple calendar APIs.
Key best practices: use webhooks (Google Calendar push notifications, Microsoft Graph change notifications) for real-time event updates rather than polling; request the minimum OAuth scopes needed - for read-only use cases, avoid requesting write permissions; normalise time zones using the IANA timezone database before storing or displaying event times; handle recurring event exceptions carefully - modifying a single occurrence requires sending the recurrence ID; implement exponential backoff for rate limit errors (HTTP 429); store event ETags or sync tokens to detect changes efficiently; and test edge cases like all-day events, multi-day events, and events with no attendees, which vary in structure across providers.
Use a unified calendar API when your product needs to support more than one or two calendar providers and you want to avoid maintaining separate integration codebases for each. A unified layer normalises the event schema, handles per-provider OAuth flows, and abstracts webhook differences - so you build once and gain coverage across Google Calendar, Microsoft Outlook, Apple Calendar, and others. Direct integrations make sense when you need provider-specific features not exposed by a unified layer, or when you're building deeply for a single platform. Knit's unified Calendar API lets B2B SaaS products connect to all major calendar platforms through a single integration without managing per-provider authentication or event schema differences.
By following the strategies in this comprehensive guide, you’ll not only harness the power of Calendar APIs but also future-proof your software or enterprise operations for the decade ahead. Whether you’re automating interviews, scheduling field services, or synchronizing resources across continents, Calendar Integration is the key to eliminating complexity and turning time management into a strategic asset.
.webp)
This guide is part of our growing collection on HRIS integrations. We’re continuously exploring new apps and updating our HRIS Guides Directory with fresh insights.
Workday has become one of the most trusted platforms for enterprise HR, payroll, and financial management. It’s the system of record for employee data in thousands of organizations. But as powerful as Workday is, most businesses don’t run only on Workday. They also use performance management tools, applicant tracking systems, payroll software, CRMs, SaaS platforms, and more.
The challenge? Making all these systems talk to each other.
That’s where the Workday API comes in. By integrating with Workday’s APIs, companies can automate processes, reduce manual work, and ensure accurate, real-time data flows between systems.
In this blog, we’ll give you everything you need, whether you’re a beginner just learning about APIs or a developer looking to build an enterprise-grade integration.
We’ll cover terminology, use cases, step-by-step setup, code examples, and FAQs. By the end, you’ll know how Workday API integration works and how to do it the right way.
Looking to quickstart with the Workday API Integration? Check our Workday API Directory for common Workday API endpoints
Workday integrations can support both internal workflows for your HR and finance teams, as well as customer-facing use cases that make SaaS products more valuable. Let’s break down some of the most impactful examples.
Performance reviews are key to fair salary adjustments, promotions, and bonus payouts. Many organizations use tools like Lattice to manage reviews and feedback, but without accurate employee data, the process can become messy.
By integrating Lattice with Workday, job titles and salaries stay synced and up to date. HR teams can run performance cycles with confidence, and once reviews are done, compensation changes flow back into Workday automatically — keeping both systems aligned and reducing manual work.
Onboarding new employees is often a race against time , from getting payroll details set up to preparing IT access. With Workday, you can automate this process.
For example, by integrating an ATS like Greenhouse with Workday:
For SaaS companies, onboarding users efficiently is key to customer satisfaction. Workday integrations make this scalable.
Take BILL, a financial operations platform, as an example:
Offboarding is just as important as onboarding, especially for maintaining security. If a terminated employee retains access to systems, it creates serious risks.
Platforms like Ramp, a spend management solution, solve this through Workday integrations:
While this guide equips developers with the skills to build robust Workday integrations through clear explanations and practical examples, the benefits extend beyond the development team. You can also expand your HRIS integrations with the Workday API integration and automate tedious tasks like data entry, freeing up valuable time to focus on other important work. Business leaders gain access to real-time insights across their entire organization, empowering them to make data-driven decisions that drive growth and profitability. This guide empowers developers to build integrations that streamline HR workflows, unlock real-time data for leaders, and ultimately unlock Workday's full potential for your organization.
Understanding key terms is essential for effective integration with Workday. Let’s look upon few of them, that will be frequently used ahead -
1. API Types: Workday offers REST and SOAP APIs, which serve different purposes. REST APIs are commonly used for web-based integrations, while SOAP APIs are often utilized for complex transactions.
2. Endpoint Structure: You must familiarize yourself with the Workday API structure as each endpoint corresponds to a specific function. A common workday API example would be retrieving employee data or updating payroll information.
3. API Documentation: Workday API documentation provides a comprehensive overview of both REST and SOAP APIs.
Workday supports two primary ways to authenticate API calls. Which one you use depends on the API family you choose:
SOAP requests are authenticated with a special Workday user account (the ISU) using WS-Security headers. Access is controlled by the security group(s) and domain policies assigned to that ISU.
REST requests use OAuth 2.0. You register an API client in Workday, grant scopes (what the client is allowed to access), and obtain access tokens (and a refresh token) to call endpoints.
To ensure a secure and reliable connection with Workday's APIs, this section outlines the essential prerequisites. These steps will lay the groundwork for a successful integration, enabling seamless data exchange and unlocking the full potential of Workday within your existing technological infrastructure.
Now that you have a comprehensive overview of the steps required to build a Workday API Integration and an overview of the Workday API documentation, lets dive deep into each step so you can build your Workday integration confidently!
The Web Services Endpoint for the Workday tenant serves as the gateway for integrating external systems with Workday's APIs, enabling data exchange and communication between platforms. To access your specific Workday web services endpoint, follow these steps:
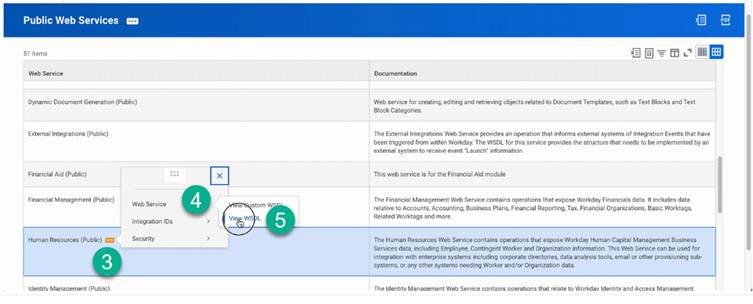
Next, you need to establish an Integration System User (ISU) in Workday, dedicated to managing API requests. This ensures enhanced security and enables better tracking of integration actions. Follow the below steps to set up an ISU in Workday:
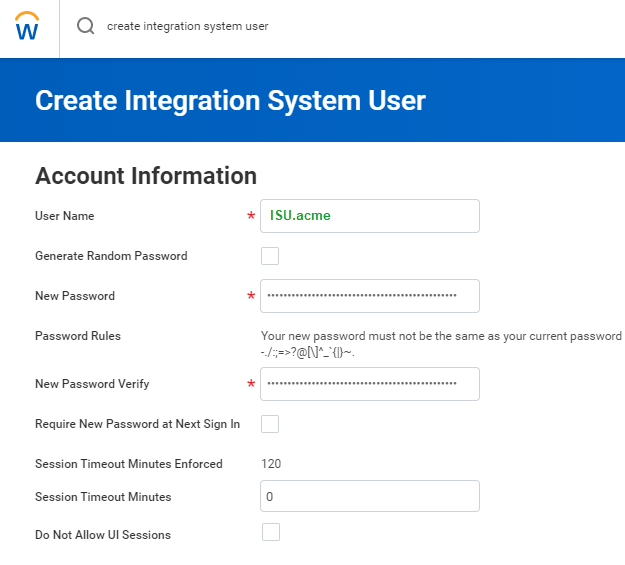
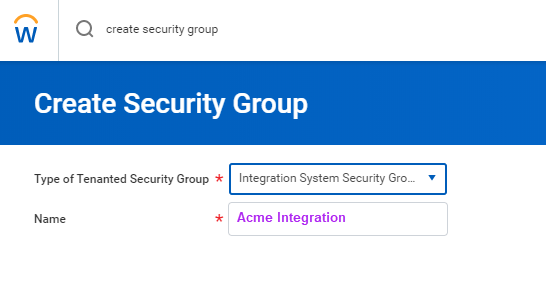
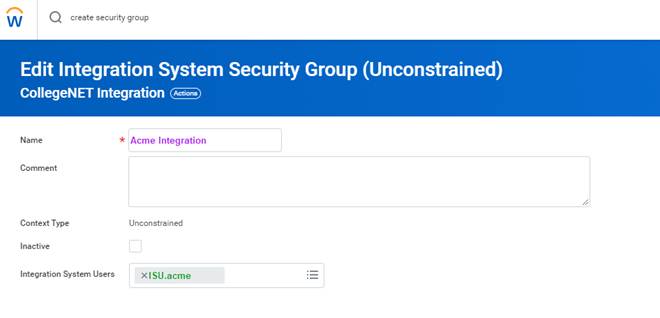
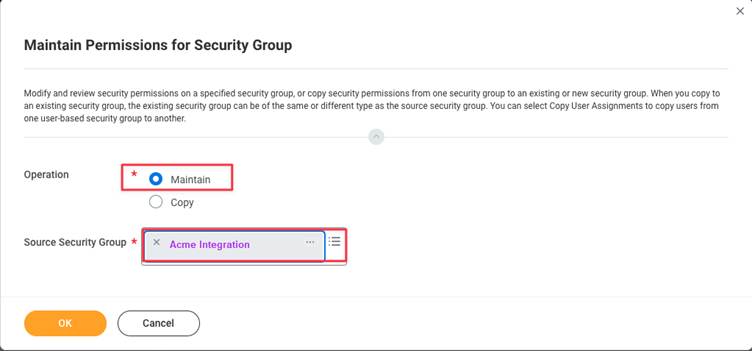

Note: The permissions listed below are necessary for the full HRIS API. These permissions may vary depending on the specific implementation
Parent Domains for HRIS
Parent Domains for HRIS
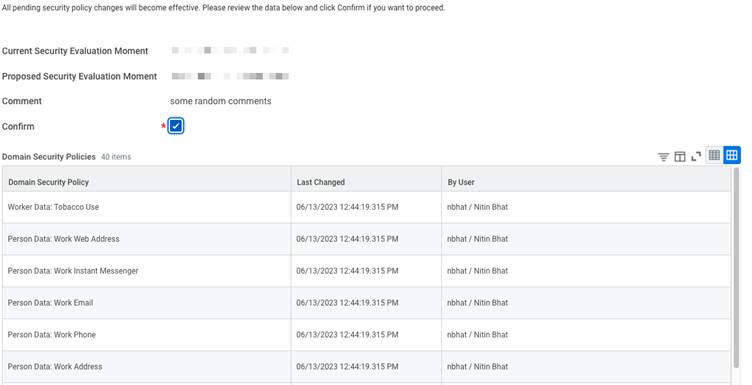
Workday offers different authentication methods. Here, we will focus on OAuth 2.0, a secure way for applications to gain access through an ISU (Integrated System User). An ISU acts like a dedicated user account for your integration, eliminating the need to share individual user credentials. Below steps highlight how to obtain OAuth 2.0 tokens in Workday:
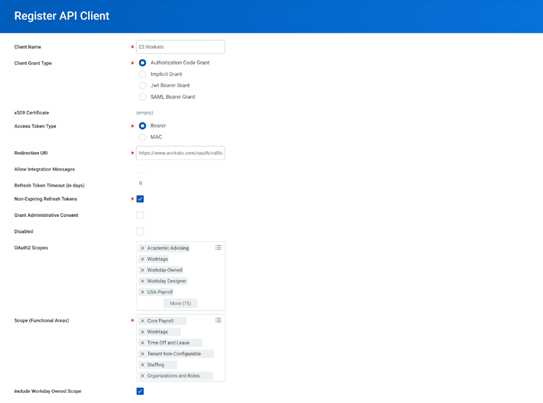
When building a Workday integration, one of the first decisions you’ll face is: Should I use SOAP or REST?
Both are supported by Workday, but they serve slightly different purposes. Let’s break it down.
SOAP (Simple Object Access Protocol) has been around for years and is still widely used in Workday, especially for sensitive data and complex transactions.
How to work with SOAP:
REST (Representational State Transfer) is the newer, lighter, and easier option for Workday integrations. It’s widely used in SaaS products and web apps.
Advantages of REST APIs
How to work with REST:
Now that you have picked between SOAP and REST, let's proceed to utilize Workday HCM APIs effectively. We'll walk through creating a new employee and fetching a list of all employees – essential building blocks for your integration. Remember, if you are using SOAP, you will authenticate your requests with an ISU user name and password, while if your are using REST, you will authenticate your requests with access tokens generated by using the OAuth refresh tokens we generated in the above steps.
In this guide, we will focus on using SOAP to construct our API requests.
First let's learn about constructing a SOAP Request Body
SOAP requests follow a specific format and use XML to structure the data. Here's an example of a SOAP request body to fetch employees using the Get Workers endpoint:
<soapenv:Envelope
xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"
xmlns:bsvc="urn:com.workday/bsvc">
<soapenv:Header>
<wsse:Security>
<wsse:UsernameToken>
<wsse:Username>{ISU USERNAME}</wsse:Username>
<wsse:Password>{ISU PASSWORD}</wsse:Password>
</wsse:UsernameToken>
</wsse:Security>
</soapenv:Header>
<soapenv:Body>
<bsvc:Get_Workers_Request xmlns:bsvc="urn:com.workday/bsvc" bsvc:version="v40.1">
</bsvc:Get_Workers_Request>
</soapenv:Body>
</soapenv:Envelope>👉 How it works:
Now that you know how to construct a SOAP request, let's look at a couple of real life Workday integration use cases:
Let's add a new team member. For this we will use the Hire Employee API! It lets you send employee details like name, job title, and salary to Workday. Here's a breakdown:
curl --location 'https://wd2-impl-services1.workday.com/ccx/service/{TENANT}/Staffing/v42.0' \
--header 'Content-Type: application/xml' \
--data-raw '<soapenv:Envelope xmlns:bsvc="urn:com.workday/bsvc" xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<wsse:Security>
<wsse:UsernameToken>
<wsse:Username>{ISU_USERNAME}</wsse:Username>
<wsse:Password>{ISU_PASSWORD}</wsse:Password>
</wsse:UsernameToken>
</wsse:Security>
<bsvc:Workday_Common_Header>
<bsvc:Include_Reference_Descriptors_In_Response>true</bsvc:Include_Reference_Descriptors_In_Response>
</bsvc:Workday_Common_Header>
</soapenv:Header>
<soapenv:Body>
<bsvc:Hire_Employee_Request bsvc:version="v42.0">
<bsvc:Business_Process_Parameters>
<bsvc:Auto_Complete>true</bsvc:Auto_Complete>
<bsvc:Run_Now>true</bsvc:Run_Now>
</bsvc:Business_Process_Parameters>
<bsvc:Hire_Employee_Data>
<bsvc:Applicant_Data>
<bsvc:Personal_Data>
<bsvc:Name_Data>
<bsvc:Legal_Name_Data>
<bsvc:Name_Detail_Data>
<bsvc:Country_Reference>
<bsvc:ID bsvc:type="ISO_3166-1_Alpha-3_Code">USA</bsvc:ID>
</bsvc:Country_Reference>
<bsvc:First_Name>Employee</bsvc:First_Name>
<bsvc:Last_Name>New</bsvc:Last_Name>
</bsvc:Name_Detail_Data>
</bsvc:Legal_Name_Data>
</bsvc:Name_Data>
<bsvc:Contact_Data>
<bsvc:Email_Address_Data bsvc:Delete="false" bsvc:Do_Not_Replace_All="true">
<bsvc:Email_Address>employee@work.com</bsvc:Email_Address>
<bsvc:Usage_Data bsvc:Public="true">
<bsvc:Type_Data bsvc:Primary="true">
<bsvc:Type_Reference>
<bsvc:ID bsvc:type="Communication_Usage_Type_ID">WORK</bsvc:ID>
</bsvc:Type_Reference>
</bsvc:Type_Data>
</bsvc:Usage_Data>
</bsvc:Email_Address_Data>
</bsvc:Contact_Data>
</bsvc:Personal_Data>
</bsvc:Applicant_Data>
<bsvc:Position_Reference>
<bsvc:ID bsvc:type="Position_ID">P-SDE</bsvc:ID>
</bsvc:Position_Reference>
<bsvc:Hire_Date>2024-04-27Z</bsvc:Hire_Date>
</bsvc:Hire_Employee_Data>
</bsvc:Hire_Employee_Request>
</soapenv:Body>
</soapenv:Envelope>'Elaboration:
Response:
<bsvc:Hire_Employee_Event_Response
xmlns:bsvc="urn:com.workday/bsvc" bsvc:version="string">
<bsvc:Employee_Reference bsvc:Descriptor="string">
<bsvc:ID bsvc:type="ID">EMP123</bsvc:ID>
</bsvc:Employee_Reference>
</bsvc:Hire_Employee_Event_Response>If everything goes well, you'll get a success message and the ID of the newly created employee!
Now, if you want to grab a list of all your existing employees. The Get Workers API is your friend!
Below is workday API get workers example:
curl --location 'https://wd2-impl-services1.workday.com/ccx/service/{TENANT}/Human_Resources/v40.1' \
--header 'Content-Type: application/xml' \
--data '<soapenv:Envelope
xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"
xmlns:bsvc="urn:com.workday/bsvc">
<soapenv:Header>
<wsse:Security>
<wsse:UsernameToken>
<wsse:Username>{ISU_USERNAME}</wsse:Username>
<wsse:Password>{ISU_USERNAME}</wsse:Password>
</wsse:UsernameToken>
</wsse:Security>
</soapenv:Header>
<soapenv:Body>
<bsvc:Get_Workers_Request xmlns:bsvc="urn:com.workday/bsvc" bsvc:version="v40.1">
<bsvc:Response_Filter>
<bsvc:Count>10</bsvc:Count>
<bsvc:Page>1</bsvc:Page>
</bsvc:Response_Filter>
<bsvc:Response_Group>
<bsvc:Include_Reference>true</bsvc:Include_Reference>
<bsvc:Include_Personal_Information>true</bsvc:Include_Personal_Information>
</bsvc:Response_Group>
</bsvc:Get_Workers_Request>
</soapenv:Body>
</soapenv:Envelope>'This is a simple GET request to the Get Workers endpoint.
Elaboration:
Response:
<?xml version='1.0' encoding='UTF-8'?>
<env:Envelope xmlns:env="http://schemas.xmlsoap.org/soap/envelope/">
<env:Body>
<wd:Get_Workers_Response xmlns:wd="urn:com.workday/bsvc" wd:version="v40.1">
<wd:Response_Filter>
<wd:Page>1</wd:Page>
<wd:Count>1</wd:Count>
</wd:Response_Filter>
<wd:Response_Data>
<wd:Worker>
<wd:Worker_Data>
<wd:Worker_ID>21001</wd:Worker_ID>
<wd:User_ID>lmcneil</wd:User_ID>
<wd:Personal_Data>
<wd:Name_Data>
<wd:Legal_Name_Data>
<wd:Name_Detail_Data wd:Formatted_Name="Logan McNeil" wd:Reporting_Name="McNeil, Logan">
<wd:Country_Reference>
<wd:ID wd:type="WID">bc33aa3152ec42d4995f4791a106ed09</wd:ID>
<wd:ID wd:type="ISO_3166-1_Alpha-2_Code">US</wd:ID>
<wd:ID wd:type="ISO_3166-1_Alpha-3_Code">USA</wd:ID>
<wd:ID wd:type="ISO_3166-1_Numeric-3_Code">840</wd:ID>
</wd:Country_Reference>
<wd:First_Name>Logan</wd:First_Name>
<wd:Last_Name>McNeil</wd:Last_Name>
</wd:Name_Detail_Data>
</wd:Legal_Name_Data>
</wd:Name_Data>
<wd:Contact_Data>
<wd:Address_Data wd:Effective_Date="2008-03-25" wd:Address_Format_Type="Basic" wd:Formatted_Address="42 Laurel Street&#xa;San Francisco, CA 94118&#xa;United States of America" wd:Defaulted_Business_Site_Address="0">
</wd:Address_Data>
<wd:Phone_Data wd:Area_Code="415" wd:Phone_Number_Without_Area_Code="441-7842" wd:E164_Formatted_Phone="+14154417842" wd:Workday_Traditional_Formatted_Phone="+1 (415) 441-7842" wd:National_Formatted_Phone="(415) 441-7842" wd:International_Formatted_Phone="+1 415-441-7842" wd:Tenant_Formatted_Phone="+1 (415) 441-7842">
</wd:Phone_Data>
</wd:Worker_Data>
</wd:Worker>
</wd:Response_Data>
</wd:Get_Workers_Response>
</env:Body>
</env:Envelope>This JSON array gives you details of all your employees including details like the name, email, phone number and more.
Use a tool like Postman or curl to POST this XML to your Workday endpoint.
If you used REST instead, the same “Get Workers” request would look much simpler:
curl --location 'https://{host}.workday.com/ccx/api/v1/{tenant}/workers' \
--header 'Authorization: Bearer {ACCESS_TOKEN}'Before moving your integration to production, it’s always safer to test everything in a sandbox environment. A sandbox is like a practice environment; it contains test data and behaves like production but without the risk of breaking live systems.
Here’s how to use a sandbox effectively:
Ask your Workday admin to provide you with a sandbox environment. Specify the type of sandbox you need (development, test, or preview). If you are a Knit customer on the Scale or Enterprise plan, Knit will provide you access to a Workday sandbox for integration testing.
Log in to your sandbox and configure it so it looks like your production environment. Add sample company data, roles, and permissions that match your real setup.
Just like in production, create a dedicated ISU account in the sandbox. Assign it the necessary permissions to access the required APIs.
Register your application inside the sandbox to get client credentials (Client ID & Secret). These credentials will be used for secure API calls in your test environment.
Use tools like Postman or cURL to send test requests to the sandbox. Test different scenarios (e.g., creating a worker, fetching employees, updating job info). Identify and fix errors before deploying to production.
Use Workday’s built-in logs to track API requests and responses. Look for failures, permission issues, or incorrect payloads. Fix issues in your code or configuration until everything runs smoothly.
Once your integration has been thoroughly tested in the sandbox and you’re confident that everything works smoothly, the next step is moving it to the production environment. To do this, you need to replace all sandbox details with production values. This means updating the URLs to point to your production Workday tenant and switching the ISU (Integration System User) credentials to the ones created for production use.
When your integration is live, it’s important to make sure you can track and troubleshoot it easily. Setting up detailed logging will help you capture every API request and response, making it much simpler to identify and fix issues when they occur. Alongside logging, monitoring plays a key role. By keeping track of performance metrics such as response times and error rates, you can ensure the integration continues to run smoothly and catch problems before they affect your workflows.
If you’re using Knit, you also get the advantage of built-in observability dashboards. These dashboards give you real-time visibility into your live integration, making debugging and ongoing maintenance far easier. With the right preparation and monitoring in place, moving from sandbox to production becomes a smooth and reliable process.
PECI (Payroll Effective Change Interface) lets you transmit employee data changes (like new hires, raises, or terminations) directly to your payroll provider, slashing manual work and errors. Below you will find a brief comparison of PECI and Web Services and also the steps required to setup PECI in Workday
Feature: PECI
Feature: Web Services
PECI set up steps :-
Workday does not natively support real-time webhooks. This means you can’t automatically get notified whenever an event happens in Workday (like a new employee being hired or someone’s role being updated). Instead, most integrations rely on polling, where your system repeatedly checks Workday for updates. While this works, it can be inefficient and slow compared to event-driven updates.
This is exactly where Knit Virtual Webhooks step in. Knit simulates webhook functionality for systems like Workday that don’t offer it out of the box.
Knit continuously monitors changes in Workday (such as employee updates, terminations, or payroll changes). When a change is detected, it instantly triggers a virtual webhook event to your application. This gives you real-time updates without having to build complex polling logic.
For example: If a new hire is added in Workday, Knit can send a webhook event to your product immediately, allowing you to provision access or update records in real time — just like native webhooks.
Getting stuck with errors can be frustrating and time-consuming. Although many times we face errors that someone else has already faced, and to avoid giving in hours to handle such errors, we have put some common errors below and solutions to how you can handle them.
Integrating with Workday can unlock huge value for your business, but it also comes with challenges. Here are some important best practices to keep in mind as you build and maintain your integration.
Workday supports two main authentication methods: ISU (Integration System User) and OAuth 2.0. The choice between them depends on your security needs and integration goals.
If your integration is customer-facing, don’t just focus on building it , think about how you’ll launch it. A Workday integration can be a major selling point, and many customers will expect it.
Before going live, align on:
This ensures your team is ready to deliver value from day one and can even help close deals faster.
Building and maintaining a Workday integration completely in-house can be very time-consuming. Your developers may spend months just scoping, coding, and testing the integration. And once it’s live, maintenance can become a headache.
For example, even a small change , like Workday returning a value in a different format (string instead of number) , could break your integration. Keeping up with these edge cases pulls your engineers away from core product work.
A third-party integration platform like Knit can solve this problem. These platforms handle the heavy lifting , scoping, development, testing, and maintenance , while also giving you features like observability dashboards, virtual webhooks, and broader HRIS coverage. This saves engineering time, speeds up your launch, and ensures your integration stays reliable over time.
We know you're here to conquer Workday integrations, and at Knit (rated #1 for ease of use as of 2025!), we're here to help! Knit offers a unified API platform which lets you connect your application to multiple HRIS, CRM, Accounting, Payroll, ATS, ERP, and more tools in one go.
Advantages of Knit for Workday Integrations
Getting Started with Knit
REST Unified API Approach with Knit
A Workday integration is a connection built between Workday and another system (like payroll, CRM, or ATS) that allows data to flow seamlessly between them. These integrations can be created using APIs, files (CSV/XML), databases, or scripts , depending on the use case and system design.
A Workday API integration is a type of integration where you use Workday’s APIs (SOAP or REST) to connect Workday with other applications. This lets you securely access, read, and update Workday data in real time.
It depends on your approach.
Workday offers:
Workday doesn’t publish all rate limits publicly. Most details are available only to customers or partners. However, some endpoints have documented limits , for example, the Strategic Sourcing Projects API allows up to 5 requests per second. Always design your integration with pagination, retry logic, and throttling to avoid issues. The safest approach is to implement exponential backoff on all retry logic, paginate all list operations regardless of expected result size, and avoid polling intervals shorter than 5 minutes for background sync jobs. If you're consuming Workday data through Knit, rate limit management is handled automatically — Knit spaces requests and retries within Workday's thresholds so your application never hits limits directly.
Workday provides sandbox environments to its customers for development and testing. If you’re a software vendor (not a Workday customer), you typically need a partnership agreement with Workday to get access. Some third-party platforms like Knit also provide sandbox access for integration testing.
Workday supports two main methods:
Yes. Workday provides both SOAP and REST APIs, covering a wide range of data domains, HR, recruiting, payroll, compensation, time tracking, and more. REST APIs are typically preferred because they are easier to implement, faster, and more developer-friendly.
Yes. If you are a Workday customer or have a formal partnership, you can build integrations with their APIs. Without access, you won’t be able to authenticate or use Workday’s endpoints.
No, Workday does not natively support outbound webhooks - there is no mechanism to push real-time change events to an external endpoint when an employee record is created, updated, or terminated. The standard alternative is polling: querying Workday's APIs on a schedule (typically every 15–60 minutes) to detect changes. Knit solves this with virtual webhooks — when you connect Workday through Knit, you receive real-time event notifications via webhook whenever data changes in Workday, without needing to build or maintain any polling infrastructure. This is particularly valuable for use cases that require fast response to Workday events, such as automated onboarding workflows triggered by new hires or access revocation triggered by terminations.
A custom Workday integration built directly against Workday Web Services typically takes 4–12 weeks for a single integration, factoring in ISU setup, OAuth configuration, SOAP/REST endpoint selection, data model mapping, error handling, and testing in sandbox before production. That timeline doesn't include ongoing maintenance as Workday releases new API versions. Using Knit's unified API, teams can go from zero to a production Workday integration in 1–3 days - Knit handles authentication, data normalization, rate limiting, and webhook delivery, so your engineering team only needs to integrate once against Knit's normalized API rather than Workday's raw endpoints directly. See https://developers.getknit.dev for implementation guides.
Workday API is a programmatic interface that allows external applications to read and write data in Workday - including employee records, payroll data, org structures, benefits, and time tracking. Workday offers two API types: SOAP-based Web Services (the older, more comprehensive set using XML) and REST APIs (modern, JSON-based, covering a growing set of domains). Both require formal authentication through an Integration System User (ISU) or OAuth 2.0 client. For SaaS products that need to access Workday data on behalf of their customers, Knit provides a unified API that normalizes Workday's data into a consistent schema alongside 100+ other HRIS platforms.
Workday's SOAP API (Web Services) is the older, more comprehensive set - it covers virtually every Workday domain including payroll, benefits, and complex HR transactions, uses XML, and requires constructing SOAP envelopes with WS-Security headers. Workday's REST API is newer, uses JSON, supports OAuth 2.0, and is simpler to implement - but it has narrower domain coverage than the full SOAP Web Services suite. For most new integrations, start with the REST API; fall back to SOAP for payroll, compliance-critical operations, or endpoints not yet exposed via REST. Knit abstracts both API types behind a single normalized endpoint, so you don't need to choose or maintain separate implementations.
Building a Workday integration directly has no per-call API cost from Workday itself - access to the API is included with Workday licenses. The real cost is engineering time: a custom integration typically takes 4–12 weeks of developer time to build and requires ongoing maintenance as Workday updates its API. Third-party tools vary: iPaaS platforms like Workato charge per task or connection; unified APIs like Knit charge per active connection per month, with pricing that covers authentication, data normalization, rate limiting, and webhook delivery. For SaaS teams building customer-facing Workday integrations at scale, unified API pricing is typically more predictable than task-based pricing as connection volume grows.
Resources to get you started on your integrations journey
Learn how to build your specific integrations use case with Knit
.webp)
Auto provisioning is the automated creation, update, and removal of user accounts when a source system - usually an HRIS, ATS, or identity provider - changes. For B2B SaaS teams, it turns employee lifecycle events into downstream account creation, role assignment, and deprovisioning workflows without manual imports or ticket queues. Knit's Unified API connects HRIS, ATS, and other upstream systems to your product so you can build this workflow without stitching together point-to-point connectors.
If your product depends on onboarding employees, assigning access, syncing identity data, or triggering downstream workflows, provisioning cannot stay manual for long.
That is why auto provisioning matters.
For B2B SaaS, auto provisioning is not just an IT admin feature. It is a core product workflow that affects activation speed, compliance posture, and the day-one experience your customers actually feel. At Knit, we see the same pattern repeatedly: a team starts by manually creating users or pushing CSVs, then quickly runs into delays, mismatched data, and access errors across systems.
In this guide, we cover:
Auto provisioning is the automated creation, update, and removal of user accounts and permissions based on predefined rules and source-of-truth data. The provisioning trigger fires when a trusted upstream system — an HRIS, ATS, identity provider, or admin workflow — records a change: a new hire, a role update, a department transfer, or a termination.
That includes:
This third step — account removal — is what separates a real provisioning system from a simple user-creation script. Provisioning without clean deprovisioning is how access debt accumulates and how security gaps appear after offboarding.
For B2B SaaS products, the provisioning flow typically sits between a source system that knows who the user is, a policy layer that decides what should happen, and one or more downstream apps that need the final user, role, or entitlement state.
Provisioning is not just an internal IT convenience.
For SaaS companies, the quality of the provisioning workflow directly affects onboarding speed, time to first value, enterprise deal readiness, access governance, support load, and offboarding compliance. If enterprise customers expect your product to work cleanly with their Workday, BambooHR, or ADP instance, provisioning becomes part of the product experience — not just an implementation detail.
The problem is bigger than "create a user account." It is really about:
When a new employee starts at a customer's company and cannot access your product on day one, that is a provisioning problem — and it lands in your support queue, not theirs.
Most automated provisioning workflows follow the same pattern regardless of which systems are involved.
The signal may come from an HRIS (a new hire created in Workday, BambooHR, or ADP), an ATS (a candidate hired in Greenhouse or Ashby), a department or role change, or an admin action that marks a user inactive. For B2B SaaS teams building provisioning into their product, the most common source is the HRIS — the system of record for employee status.
The trigger may come from a webhook, a scheduled sync, a polling job, or a workflow action taken by an admin. Most HRIS platforms do not push real-time webhooks natively - which is why Knit provides virtual webhooks that normalize polling into event-style delivery your application can subscribe to.
Before the action is pushed downstream, the workflow normalizes fields across systems. Common attributes include user ID, email, team, location, department, job title, employment status, manager, and role or entitlement group. This normalization step is where point-to-point integrations usually break — every HRIS represents these fields differently.
This is where the workflow decides whether to create, update, or remove a user; which role to assign; which downstream systems should receive the change; and whether the action should wait for an approval or additional validation. Keeping this logic outside individual connectors is what makes the system maintainable as rules evolve.
The provisioning layer creates or updates the user in downstream systems and applies app assignments, permission groups, role mappings, team mappings, and license entitlements as defined by the rules.
Good provisioning architecture does not stop at "request sent." You need visibility into success or failure state, retry status, partial completion, skipped records, and validation errors. Silent failures are the most common cause of provisioning-related support tickets.
When a user becomes inactive in the source system, the workflow should trigger account disablement, entitlement removal, access cleanup, and downstream reconciliation. Provisioning without clean deprovisioning creates a security problem and an audit problem later. This step is consistently underinvested in projects that focus only on new-user creation.
Provisioning typically spans more than two systems. Understanding which layer owns what is the starting point for any reliable architecture.
The most important data objects are usually: user profile, employment or account status, team or department, location, role, manager, entitlement group, and target app assignment.
When a SaaS product needs to pull employee data or receive lifecycle events from an HRIS, the typical challenge is that each HRIS exposes these objects through a different API schema. Knit's Unified HRIS API normalizes these objects across 60+ HRIS and payroll platforms so your provisioning logic only needs to be written once.
Manual provisioning breaks first in enterprise onboarding. The more users, apps, approvals, and role rules involved, the more expensive manual handling becomes. Enterprise buyers — especially those running Workday or SAP — will ask about automated provisioning during the sales process and block deals where it is missing.
SCIM (System for Cross-domain Identity Management) is a standard protocol used to provision and deprovision users across systems in a consistent way. When both the identity provider and the SaaS application support SCIM, it can automate user creation, attribute updates, group assignment, and deactivation without custom integration code.
But SCIM is not the whole provisioning strategy for most B2B SaaS products. Even when SCIM is available, teams still need to decide what the real source of truth is, how attributes are mapped between systems, how roles are assigned from business rules rather than directory groups, how failures are retried, and how downstream systems stay in sync when SCIM is not available.
The more useful question is not "do we support SCIM?" It is: do we have a reliable provisioning workflow across the HRIS, ATS, and identity systems our customers actually use? For teams building that workflow across many upstream platforms, Knit's Unified API reduces that to a single integration layer instead of per-platform connectors.
SAML and SCIM are often discussed together but solve different problems. SAML handles authentication — it lets users log into your application via their company's identity provider using SSO. SCIM handles provisioning — it keeps the user accounts in your application in sync with the identity provider over time. SAML auto provisioning (sometimes called JIT provisioning) creates a user account on first login; SCIM provisioning creates and manages accounts in advance, independently of whether the user has logged in.
For enterprise customers, SCIM is generally preferred because it handles pre-provisioning, attribute sync, group management, and deprovisioning. JIT provisioning via SAML creates accounts reactively and cannot handle deprovisioning reliably on its own.
Provisioning projects fail in familiar ways.
The wrong source of truth. If one system says a user is active and another says they are not, the workflow becomes inconsistent. HRIS is almost always the right source for employment status — not the identity provider, not the product itself.
Weak attribute mapping. Provisioning logic breaks when fields like department, manager, role, or location are inconsistent across systems. This is the most common cause of incorrect role assignment in enterprise accounts.
No visibility into failures. If a provisioning job fails silently, support only finds out when a user cannot log in or cannot access the right resources. Observability is not optional.
Deprovisioning treated as an afterthought. Teams often focus on new-user creation and underinvest in access removal — exactly where audit and security issues surface. Every provisioning build should treat deprovisioning as a first-class requirement.
Rules that do not scale. A provisioning script that works for one HRIS often becomes unmanageable when you add more target systems, role exceptions, conditional approvals, and customer-specific logic. Abstraction matters early.
When deciding how to build an automated provisioning workflow, SaaS teams typically evaluate three approaches:
Native point-to-point integrations mean building a separate connector for each HRIS or identity system. This offers maximum control but creates significant maintenance overhead as each upstream API changes its schema, authentication, or rate limits.
Embedded iPaaS platforms (like Workato or Tray.io embedded) let you compose workflows visually. These work well for internal automation but add a layer of operational complexity when the workflow needs to run reliably inside a customer-facing SaaS product.
Unified API providers like Knit normalize many upstream systems into a single API endpoint. You write the provisioning logic once and it works across all connected HRIS, ATS, and other platforms. This is particularly effective when provisioning depends on multiple upstream categories — HRIS for employee status, ATS for new hire events, identity providers for role mapping. See how Knit compares to other approaches in our Native Integrations vs. Unified APIs guide.
As SaaS products increasingly use AI agents to automate workflows, provisioning becomes a data access question as well as an account management question. An AI agent that needs to look up employee data, check role assignments, or trigger onboarding workflows needs reliable access to HRIS and ATS data in real time.
Knit's MCP Servers expose normalized HRIS, ATS, and payroll data to AI agents via the Model Context Protocol — giving agents access to employee records, org structures, and role data without custom tooling per platform. This extends the provisioning architecture into the AI layer: the same source-of-truth data that drives user account creation can power AI-assisted onboarding workflows, access reviews, and anomaly detection. Read more in Integrations for AI Agents.
Building in-house can make sense when the number of upstream systems is small (one or two HRIS platforms), the provisioning rules are deeply custom and central to your product differentiation, your team is comfortable owning long-term maintenance of each upstream API, and the workflow is narrow enough that a custom solution will not accumulate significant edge-case debt.
A unified API layer typically makes more sense when customers expect integrations across many HRIS, ATS, or identity platforms; the same provisioning pattern repeats across customer accounts with different upstream systems; your team wants faster time to market on provisioning without owning per-platform connector maintenance; and edge cases — authentication changes, schema updates, rate limits — are starting to spread work across product, engineering, and support.
This is especially true when provisioning depends on multiple upstream categories. If your provisioning workflow needs HRIS data for employment status, ATS data for new hire events, and potentially CRM or accounting data for account management, a Unified API reduces that to a single integration contract instead of three or more separate connectors.
Auto provisioning is not just about creating users automatically. It is about turning identity and account changes in upstream systems — HRIS, ATS, identity providers — into a reliable product workflow that runs correctly across every customer's tech stack.
For B2B SaaS, the quality of that workflow affects onboarding speed, support burden, access hygiene, and enterprise readiness. The real standard is not "can we create a user." It is: can we provision, update, and deprovision access reliably across the systems our customers already use — without building and maintaining a connector for every one of them?
What is auto provisioning?Auto provisioning is the automatic creation, update, and removal of user accounts and access rights when a trusted source system changes — typically an HRIS, ATS, or identity provider. In B2B SaaS, it turns employee lifecycle events into downstream account creation, role assignment, and deprovisioning workflows without manual imports or admin tickets.
What is the difference between SAML auto provisioning and SCIM?SAML handles authentication — it lets users log into an application via SSO. SCIM handles provisioning — it keeps user accounts in sync with the identity provider over time, including pre-provisioning and deprovisioning. SAML JIT provisioning creates accounts on first login; SCIM manages the full account lifecycle independently of login events. For enterprise use cases, SCIM is the stronger approach for reliability and offboarding coverage.
What is the main benefit of automated provisioning?The main benefit is reliability at scale. Automated provisioning eliminates manual import steps, reduces access errors from delayed updates, ensures deprovisioning happens when users leave, and makes the provisioning workflow auditable. For SaaS products selling to enterprise customers, it also removes a common procurement blocker.
How does HRIS-driven provisioning work?HRIS-driven provisioning uses employee data changes in an HRIS (such as Workday, BambooHR, or ADP) as the trigger for downstream account actions. When a new employee is created in the HRIS, the provisioning workflow fires to create accounts, assign roles, and onboard the user in downstream SaaS applications. When the employee leaves, the same workflow triggers deprovisioning. Knit's Unified HRIS API normalizes these events across 60+ HRIS and payroll platforms.
What is the difference between provisioning and deprovisioning?Provisioning creates and configures user access. Deprovisioning removes or disables it. Both should be handled by the same workflow — deprovisioning is not an edge case. Incomplete deprovisioning is the most common cause of access debt and audit failures in SaaS products.
Does auto provisioning require SCIM?No. SCIM is one mechanism for automating provisioning, but many HRIS platforms and upstream systems do not support SCIM natively. Automated provisioning can be built using direct API integrations, webhooks, or scheduled sync jobs. Knit provides virtual webhooks for HRIS platforms that do not support native real-time events, allowing provisioning workflows to be event-driven without requiring SCIM from every upstream source.
When should a SaaS team use a unified API for provisioning instead of building native connectors?A unified API layer makes more sense when the provisioning workflow needs to work across many HRIS or ATS platforms, the same logic should apply regardless of which system a customer uses, and maintaining per-platform connectors would spread significant engineering effort. Knit's Unified API lets SaaS teams write provisioning logic once and deploy it across all connected platforms, including Workday, BambooHR, ADP, Greenhouse, and others.
If your team is still handling onboarding through manual imports, ticket queues, or one-off scripts, it is usually a sign that the workflow needs a stronger integration layer.
Knit connects SaaS products to HRIS, ATS, payroll, and other upstream systems through a single Unified API — so provisioning and downstream workflows do not turn into connector sprawl as your customer base grows.
-p-1080.png)
In today's fast-evolving business landscape, companies are streamlining employee financial offerings, particularly in payroll-linked payments and leasing solutions. These include auto-leasing programs, payroll-based financing, and other benefits designed to enhance employee financial well-being.
By integrating directly with an organization’s Human Resources Information System (HRIS) and payroll systems, solution providers can offer a seamless experience that benefits both employers (B2B) and employees (B2C). This guide explores the importance of payroll integration, challenges businesses face, and best practices for implementing scalable solutions, with insights drawn from the B2B auto-leasing sector.
Payroll-linked leasing and financing offer key advantages for companies and employees:
Despite its advantages, integrating payroll-based solutions presents several challenges:
Integrating payroll systems into leasing platforms enables:
A structured payroll integration process typically follows these steps:
To ensure a smooth and efficient integration, follow these best practices:
A robust payroll integration system must address:
A high-level architecture for payroll integration includes:
┌────────────────┐ ┌─────────────────┐
│ HR System │ │ Payroll │
│(Cloud/On-Prem) │ → │(Deduction Logic)│
└───────────────┘ └─────────────────┘
│ (API/Connector)
▼
┌──────────────────────────────────────────┐
│ Unified API Layer │
│ (Manages employee data & payroll flow) │
└──────────────────────────────────────────┘
│ (Secure API Integration)
▼
┌───────────────────────────────────────────┐
│ Leasing/Finance Application Layer │
│ (Approvals, User Portal, Compliance) │
└───────────────────────────────────────────┘
A single API integration that connects various HR systems enables scalability and flexibility. Solutions like Knit offer pre-built integrations with 40+ HRMS and payroll systems, reducing complexity and development costs.
To implement payroll-integrated leasing successfully, follow these steps:
Payroll-integrated leasing solutions provide significant advantages for employers and employees but require well-planned, secure integrations. By leveraging a unified API layer, automating approval workflows, and payroll deductions data, businesses can streamline operations while enhancing employee financial wellness.
For companies looking to reduce overhead and accelerate implementation, adopting a pre-built API solution can simplify payroll integration while allowing them to focus on their core leasing offerings. Now is the time to map out your integration strategy, define your data requirements, and build a scalable solution that transforms the employee leasing experience.
Ready to implement a seamless payroll-integrated leasing solution? Take the next step today by exploring unified API platforms and optimizing your HR-tech stack for maximum efficiency. To talk to our solutions experts at Knit you can reach out to us here

Seamless CRM and ticketing system integrations are critical for modern customer support software. However, developing and maintaining these integrations in-house is time-consuming and resource-intensive.
In this article, we explore how Knit’s Unified API simplifies customer support integrations, enabling teams to connect with multiple platforms—HubSpot, Zendesk, Intercom, Freshdesk, and more—through a single API.
Customer support platforms depend on real-time data exchange with CRMs and ticketing systems. Without seamless integrations:
A unified API solution eliminates these issues, accelerating integration processes and reducing ongoing maintenance burdens.
Developing custom integrations comes with key challenges:
For example a company offering video-assisted customer support where users can record and send videos along with support tickets. Their integration requirements include:
With Knit’s Unified API, these steps become significantly simpler.
By leveraging Knit’s single API interface, companies can automate workflows and reduce development time. Here’s how:
Knit provides pre-built ticketing APIs to simplify integration with customer support systems:
For a successful integration, follow these best practices:
Streamline your customer support integrations with Knit and focus on delivering a world-class support experience!
📞 Need expert advice? Book a consultation with our team. Find time here
Developer resources on APIs and integrations
Building a ServiceNow integration is fundamentally different from every other API integration you've built — because there is no single ServiceNow. Every customer runs their own instance at a unique subdomain, with their own OAuth endpoints, their own permission model, and their own table customisations. Guides written for ServiceNow developers working inside an instance won't help you. This one is written for developers building a product that connects to their customers' ServiceNow instances.
Quick answer: Use the Table API (/api/now/table/{tableName}) for reading and writing incidents, users, groups, and requests. Authenticate via OAuth 2.0 — but collect the customer's instance URL first, since every OAuth endpoint is instance-specific. The five tables that cover 90% of ITSM product integration use cases areincident,sys_user,sys_user_group,sc_request, andchange_request.
This guide covers per-instance OAuth setup, Table API endpoints and query syntax, webhook configuration, rate limits, and three real-world integration patterns with working code — all from the perspective of an external developer connecting to a customer's ServiceNow instance.
If your product needs to support ServiceNow alongside other ITSM tools like Jira, Zendesk, or GitHub Issues, there's a unified approach worth knowing about — covered in the Building with Knit section.
ServiceNow exposes several API surfaces. The right one for your integration depends on what you're doing:
The Table API is the right choice for the vast majority of product integrations. It provides CRUD access to any ServiceNow table through a consistent URL pattern:
https://{instance}.service-now.com/api/now/table/{tableName}The Scripted REST API requires a ServiceNow developer to create custom endpoints inside the instance — you can't deploy these from outside. The Import Set API is for bulk historical data loads, not real-time integrations.
ServiceNow OAuth is standard OAuth 2.0 in mechanics, but the endpoints are not standard — they're instance-specific. This is the detail that trips most developers up when building a multi-tenant integration.
For a typical API (Slack, GitHub, HubSpot), you hardcode a single OAuth endpoint:
https://slack.com/api/oauth.v2.accessFor ServiceNow, every customer has their own:
https://{customer-instance}.service-now.com/oauth_token.do
https://{customer-instance}.service-now.com/oauth_auth.doThis means your integration must:
Here's what that looks like in practice:
Your onboarding UI needs to ask for the instance identifier — the [company] part of https://[company].service-now.com. This is what Knit's auth screen shows users when they connect ServiceNow.
def get_servicenow_endpoints(instance: str) -> dict:
"""
Build instance-specific OAuth endpoints from the instance identifier.
instance = "mycompany" (not the full URL)
"""
base = f"https://{instance}.service-now.com"
return {
"base_url": base,
"auth_url": f"{base}/oauth_auth.do",
"token_url": f"{base}/oauth_token.do",
"api_base": f"{base}/api/now/table"
}Before any OAuth flow can happen, the customer's ServiceNow admin must register your application as an OAuth provider in their instance: System OAuth > Application Registry > New > Create an OAuth API endpoint for external clients.
Required fields:
This is a one-time admin step per customer instance. Document it clearly in your onboarding instructions.
import requests
from urllib.parse import urlencode
def get_auth_url(instance: str, client_id: str, redirect_uri: str, state: str) -> str:
"""Redirect the customer's admin to this URL to initiate OAuth consent."""
endpoints = get_servicenow_endpoints(instance)
params = {
"response_type": "code",
"client_id": client_id,
"redirect_uri": redirect_uri,
"state": state # CSRF protection — always validate on callback
}
return f"{endpoints['auth_url']}?{urlencode(params)}"
def exchange_code_for_tokens(instance: str, client_id: str, client_secret: str,
code: str, redirect_uri: str) -> dict:
"""Exchange the authorization code for access + refresh tokens."""
endpoints = get_servicenow_endpoints(instance)
response = requests.post(
endpoints["token_url"],
data={
"grant_type": "authorization_code",
"code": code,
"redirect_uri": redirect_uri,
"client_id": client_id,
"client_secret": client_secret
}
)
response.raise_for_status()
tokens = response.json()
# Store tokens["access_token"], tokens["refresh_token"], and instance per customer
return tokensServiceNow access tokens expire after 30 minutes by default (configurable by the admin). Build refresh logic before you hit your first expiry:
def refresh_access_token(instance: str, client_id: str, client_secret: str,
refresh_token: str) -> dict:
endpoints = get_servicenow_endpoints(instance)
response = requests.post(
endpoints["token_url"],
data={
"grant_type": "refresh_token",
"client_secret": client_secret,
"client_id": client_id,
"refresh_token": refresh_token
}
)
response.raise_for_status()
return response.json() # New access_token and refresh_tokenIf you're building a product that integrates with ServiceNow alongside other ITSM tools — Jira, Zendesk, GitHub, Linear — building and maintaining per-instance OAuth for each one is significant infrastructure overhead. Knit handles ServiceNow's instance URL collection and OAuth flow per customer, so you get a single integration layer across all your supported tools. → getknit.dev/integration/servicenow
ServiceNow has hundreds of tables. For a B2B product integration, these five cover the vast majority of use cases:
All Table API requests follow the same pattern:
GET https://{instance}.service-now.com/api/now/table/{table}
Authorization: Bearer {access_token}
Accept: application/json
Content-Type: application/json
X-no-response-body: falseServiceNow's Table API uses sysparm_ prefixed query parameters for filtering, field selection, and pagination. Understanding these is essential — without them you'll either pull the entire table or struggle with pagination.
def get_incidents(instance: str, token: str,
state: str = None, assigned_to: str = None,
limit: int = 100, offset: int = 0) -> dict:
"""
Fetch incidents from a ServiceNow instance.
state codes: 1=New, 2=In Progress, 3=On Hold, 6=Resolved, 7=Closed
"""
query_parts = []
if state:
query_parts.append(f"state={state}")
if assigned_to:
query_parts.append(f"assigned_to.user_name={assigned_to}")
params = {
"sysparm_limit": limit,
"sysparm_offset": offset,
"sysparm_fields": "sys_id,number,short_description,description,state,"
"priority,assigned_to,assignment_group,opened_at,"
"resolved_at,sys_created_on,sys_updated_on",
"sysparm_exclude_reference_link": "true",
"sysparm_display_value": "false" # Raw values are easier to work with
}
if query_parts:
params["sysparm_query"] = "^".join(query_parts)
response = requests.get(
f"https://{instance}.service-now.com/api/now/table/incident",
headers={
"Authorization": f"Bearer {token}",
"Accept": "application/json"
},
params=params
)
response.raise_for_status()
# Pagination: check X-Total-Count header for total record count
total = int(response.headers.get("X-Total-Count", 0))
return {
"records": response.json()["result"],
"total": total,
"has_more": (offset + limit) < total
}def create_incident(instance: str, token: str,
short_description: str, description: str,
caller_id: str = None, priority: int = 3,
assignment_group: str = None) -> dict:
"""
Creates an incident. Priority: 1=Critical, 2=High, 3=Moderate, 4=Low.
caller_id and assignment_group are sys_id values from sys_user/sys_user_group.
"""
payload = {
"short_description": short_description,
"description": description,
"priority": str(priority),
"impact": str(priority), # Often mirrors priority
"urgency": str(priority)
}
if caller_id:
payload["caller_id"] = caller_id
if assignment_group:
payload["assignment_group"] = assignment_group
response = requests.post(
f"https://{instance}.service-now.com/api/now/table/incident",
headers={
"Authorization": f"Bearer {token}",
"Accept": "application/json",
"Content-Type": "application/json"
},
json=payload
)
response.raise_for_status()
result = response.json()["result"]
return {
"sys_id": result["sys_id"], # Use this for future updates
"number": result["number"], # Human-readable e.g. INC0012345
"state": result["state"],
"url": f"https://{instance}.service-now.com/nav_to.do?uri=incident.do?sys_id={result['sys_id']}"
}def update_incident(instance: str, token: str,
sys_id: str, **fields) -> dict:
"""
Update any incident fields by sys_id.
Common fields: state, assigned_to, assignment_group, work_notes, close_notes
"""
response = requests.patch(
f"https://{instance}.service-now.com/api/now/table/incident/{sys_id}",
headers={
"Authorization": f"Bearer {token}",
"Accept": "application/json",
"Content-Type": "application/json"
},
json=fields
)
response.raise_for_status()
return response.json()["result"]# Get a user by their email address (common lookup pattern)
def get_user_by_email(instance: str, token: str, email: str) -> dict | None:
response = requests.get(
f"https://{instance}.service-now.com/api/now/table/sys_user",
headers={"Authorization": f"Bearer {token}", "Accept": "application/json"},
params={
"sysparm_query": f"email={email}^active=true",
"sysparm_fields": "sys_id,name,email,user_name",
"sysparm_limit": 1,
"sysparm_exclude_reference_link": "true"
}
)
response.raise_for_status()
results = response.json()["result"]
return results[0] if results else None
# List all active groups
def list_groups(instance: str, token: str) -> list:
response = requests.get(
f"https://{instance}.service-now.com/api/now/table/sys_user_group",
headers={"Authorization": f"Bearer {token}", "Accept": "application/json"},
params={
"sysparm_query": "active=true",
"sysparm_fields": "sys_id,name,description,manager",
"sysparm_limit": 1000,
"sysparm_exclude_reference_link": "true"
}
)
response.raise_for_status()
return response.json()["result"]ServiceNow does not have native outbound webhooks that you configure from outside the instance. Real-time event notifications require a ServiceNow admin on the customer side to set up two things: a Business Rule (which triggers on record events) and an Outbound REST Message (which sends the payload to your server).
This is a key difference from APIs like GitHub or Slack where you register a webhook URL programmatically. For ServiceNow, you need to provide your customers' IT teams with setup instructions.
What the customer's admin configures:
Business Rule (System Definition > Business Rules):
incidentafter insert/update// ServiceNow Business Rule script
var message = new sn_ws.RESTMessageV2('Your Integration', 'POST incident');
message.setStringParameterNoEscape('sys_id', current.sys_id);
message.setStringParameterNoEscape('number', current.number);
message.setStringParameterNoEscape('state', current.state);
message.setStringParameterNoEscape('updated_at', current.sys_updated_on);
var response = message.execute();Outbound REST Message (System Web Services > Outbound > REST Message):
On your server, receive and process the payload:
from flask import Flask, request, abort
import hmac, hashlib
app = Flask(__name__)
@app.route("/webhook/servicenow", methods=["POST"])
def handle_servicenow_event():
# ServiceNow doesn't send a standard signature header —
# secure your endpoint via IP allowlisting or a shared secret
# passed as a query param or custom header agreed with the admin
payload = request.json
sys_id = payload.get("sys_id")
state = payload.get("state")
# State codes: 1=New, 2=In Progress, 3=On Hold, 6=Resolved, 7=Closed
if state in ("6", "7"):
close_linked_item_in_your_product(sys_id)
return "", 200Because webhook setup requires admin access on the customer's instance, build your integration to work without webhooks first (polling) and offer webhook setup as an enhancement for customers whose admins can configure it.
ServiceNow rate limits are instance-configured, not globally fixed — your customer's IT admin controls them. This creates a situation you won't face with other APIs: two customers on the same plan can have different rate limits.
Unlike GitHub or Slack, ServiceNow does not return rate limit headers (X-RateLimit-Remaining etc.) on every response. You'll receive a 429 Too Many Requests when you hit the limit — build retry logic with exponential backoff:
import time
def servicenow_request(url: str, token: str, max_retries: int = 3, **kwargs) -> requests.Response:
for attempt in range(max_retries):
response = requests.get(url, headers={
"Authorization": f"Bearer {token}",
"Accept": "application/json"
}, **kwargs)
if response.status_code == 429:
wait = 2 ** attempt * 10 # 10s, 20s, 40s
time.sleep(wait)
continue
if response.status_code == 401:
# Token likely expired — trigger refresh and retry once
raise TokenExpiredError("Access token expired")
response.raise_for_status()
return response
raise Exception(f"Max retries exceeded for {url}")For sustained high-volume integrations, use a dedicated integration user account in ServiceNow rather than a human user's account — this ensures your rate limit isn't shared with the user's other API activity.
Pull all open incidents and keep them in sync with periodic polling:
def full_incident_sync(instance: str, token: str) -> list:
"""
Full sync of all open and in-progress incidents.
Run on initial connection; switch to delta sync (updatedAfter) for ongoing.
"""
all_incidents = []
offset = 0
limit = 100
while True:
page = get_incidents(
instance=instance,
token=token,
limit=limit,
offset=offset
)
all_incidents.extend(page["records"])
if not page["has_more"]:
break
offset += limit
# Normalise ServiceNow state codes to your product's status model
status_map = {
"1": "open", "2": "in_progress", "3": "on_hold",
"6": "resolved", "7": "closed"
}
return [
{
"external_id": i["sys_id"],
"reference": i["number"],
"title": i["short_description"],
"status": status_map.get(str(i["state"]), "unknown"),
"priority": i["priority"],
"assignee_id": i.get("assigned_to"),
"created_at": i["sys_created_on"],
"updated_at": i["sys_updated_on"]
}
for i in all_incidents
]The common "escalate to IT" pattern — a user triggers an action in your product and it creates a ServiceNow incident:
Raw ServiceNow approach — you need to resolve the user's sys_id first, look up the right assignment group sys_id, then create the incident:
# Step 1: resolve caller sys_id from user's email
caller = get_user_by_email(instance, token, user_email)
caller_sys_id = caller["sys_id"] if caller else None
# Step 2: look up assignment group sys_id
groups = list_groups(instance, token)
group = next((g for g in groups if g["name"] == "IT Help Desk"), None)
group_sys_id = group["sys_id"] if group else None
# Step 3: create the incident
incident = create_incident(
instance=instance,
token=token,
short_description=f"Alert from {your_product}: {alert_title}",
description=alert_details,
caller_id=caller_sys_id,
assignment_group=group_sys_id,
priority=2 # High
)
# Store incident["sys_id"] in your DB for future status syncWith Knit — skip the sys_id resolution steps. Knit's normalised endpoints return consistent IDs you can use directly:
# Get incidents already filtered and paginated
incidents = requests.get(
"https://api.getknit.dev/v1.0/ticketing/tickets.list",
headers={
"Authorization": f"Bearer {knit_token}",
"X-Knit-Integration-Id": integration_id
},
params={"status": "OPEN", "assignedToId": user_id}
)
# Update an incident's status
requests.post(
"https://api.getknit.dev/v1.0/ticketing/ticket.update",
headers={
"Authorization": f"Bearer {knit_token}",
"X-Knit-Integration-Id": integration_id
},
json={"ticketId": ticket_id, "status": "IN_PROGRESS", "assignedToId": agent_id}
)Many products need to know which ServiceNow users and groups a customer has, to map them to your product's access model:
def sync_users_and_groups(instance: str, token: str) -> dict:
"""
Sync all active users and groups from ServiceNow.
Used to populate assignee pickers and map access levels.
"""
# Fetch users — paginate if the instance has many
users_response = requests.get(
f"https://{instance}.service-now.com/api/now/table/sys_user",
headers={"Authorization": f"Bearer {token}", "Accept": "application/json"},
params={
"sysparm_query": "active=true",
"sysparm_fields": "sys_id,name,email,user_name,department",
"sysparm_limit": 1000,
"sysparm_exclude_reference_link": "true"
}
)
users = users_response.json()["result"]
# Fetch groups
groups = list_groups(instance, token)
return {
"users": [
{"id": u["sys_id"], "name": u["name"],
"email": u["email"], "username": u["user_name"]}
for u in users
],
"groups": [
{"id": g["sys_id"], "name": g["name"]}
for g in groups
]
}The two hardest parts of a ServiceNow product integration are both auth-related: collecting the instance URL from each customer, constructing per-instance OAuth endpoints, and managing token refresh independently per customer installation. These are real engineering problems that have nothing to do with the value you're delivering to users.
Knit handles ServiceNow authentication — including instance URL collection and per-customer OAuth — so your integration starts from a normalised API call rather than an auth infrastructure build. The same Knit headers work across all your ticketing integrations:
Authorization: Bearer {your-knit-token}
X-Knit-Integration-Id: {customer-integration-id}This is especially valuable if your product also supports Jira, Zendesk, GitHub Issues, Linear, or Asana — Knit's same API surface covers all of them, so you write the integration logic once.
The Knit APIs available for ServiceNow:
Example: list open high-priority incidents via Knit
/
import requests
def get_open_high_priority_incidents(knit_token: str, integration_id: str) -> list:
"""
No instance URL handling. No token refresh. No sysparm syntax.
Works the same way for ServiceNow, Jira, Zendesk, and every other Knit-supported tool.
"""
all_tickets = []
cursor = None
while True:
params = {"status": "OPEN"}
if cursor:
params["cursor"] = cursor
response = requests.get(
"https://api.getknit.dev/v1.0/ticketing/tickets.list",
headers={
"Authorization": f"Bearer {knit_token}",
"X-Knit-Integration-Id": integration_id
},
params=params
)
response.raise_for_status()
data = response.json()["data"]
all_tickets.extend(data["tickets"])
cursor = data["pagination"].get("next")
if not cursor:
break
return all_tickets
→ See the full ServiceNow integration on Knit: getknit.dev/integration/servicenow
→ Knit's ticketing API docs: developers.getknit.dev
mycompany, not https://mycompany.service-now.com).sysparm_fields from the start to avoid pulling data you don't need.sys_user and sys_user_group on integration setup and cache the results. These change infrequently and are needed to populate assignee pickers and resolve group names.incident with sysparm_query=sys_updated_on>javascript:gs.dateGenerate('YYYY-MM-DD','HH:mm:ss') to fetch only records changed since your last sync rather than re-pulling everything.
What is the ServiceNow Table API?
The ServiceNow Table API is the primary REST interface for reading and writing records across any ServiceNow table. It exposes endpoints at https://{instance}.service-now.com/api/now/table/{tableName} and supports GET, POST, PUT, PATCH, and DELETE operations. For product integrations, the most relevant tables are incident, sys_user, sys_user_group, sc_request, and change_request. The Table API supports powerful query filtering via the sysparm_query parameter.
How do I authenticate with the ServiceNow REST API?
ServiceNow supports OAuth 2.0 (recommended for production) and Basic Auth. For OAuth, the token endpoint is https://{instance}.service-now.com/oauth_token.do and the authorization endpoint is https://{instance}.service-now.com/oauth_auth.do — both are instance-specific, so you must collect the customer's instance URL before initiating the OAuth flow. Tokens expire after 30 minutes by default; use the refresh token to obtain new ones without user interaction.
What is sysparm_query in ServiceNow?
sysparm_query is the ServiceNow Table API's parameter for filtering records. It uses ServiceNow's encoded query syntax: field operators joined with ^ (AND) or ^OR (OR). Common operators include =, !=, IN, STARTSWITH, CONTAINS. Example: state=1^assigned_toISNOTEMPTY^opened_at>=javascript:gs.beginningOfLast30Days(). Build queries in the ServiceNow Filter Builder UI first, then copy the encoded query string to use in your API calls.
What are the ServiceNow API rate limits?
ServiceNow API rate limits are configured per instance by the customer's admin, not fixed globally. The default is typically 5,000 API requests per hour per user account, but enterprise instances can have this set differently. ServiceNow does not return standard rate limit headers on every response — watch for 429 Too Many Requests and implement exponential backoff. The API defaults to a maximum of 10,000 records per single Table API query (controlled by the glide.db.max_view_records system property — most instances leave this at the default).
How do ServiceNow webhooks work?
ServiceNow does not have native outbound webhooks that you register from outside the instance. Real-time event notifications are built using Business Rules (server-side scripts that fire on table record events) combined with Outbound REST Messages. This requires a ServiceNow admin on the customer's side to configure. For integrations where webhook setup isn't feasible, use delta polling: query the incident table with a sys_updated_on> filter on a schedule.
What is the difference between the ServiceNow Table API and Import Set API?
The Table API directly reads and writes records with immediate effect — the right choice for most product integrations. The Import Set API stages data in a temporary table first, then a transform map processes it into the target table. Use Import Sets only for bulk historical data migration. For real-time integrations involving incidents, users, and groups, always use the Table API.
Which ServiceNow tables should I use for an ITSM integration?
Focus on five tables: incident for IT incidents, sys_user for user records, sys_user_group for team assignments, sc_request for service catalog requests, and change_request for change management. The incident table's state field uses numeric codes — 1=New, 2=In Progress, 3=On Hold, 6=Resolved, 7=Closed — always map these explicitly in your code rather than relying on display values.
Is there a simpler way to integrate with ServiceNow without building per-instance OAuth for each customer?
Yes. Knit provides a unified ticketing API that handles ServiceNow authentication — including collecting the instance URL and managing the per-instance OAuth flow per customer. Instead of building dynamic OAuth endpoint logic, token refresh, and per-customer credential storage, your customers connect their ServiceNow instance once through Knit's auth layer. You then call Knit's normalised endpoints for incidents, accounts, contacts, users, and groups — the same interface that works across Jira, GitHub, Zendesk, and more. → getknit.dev/integration/servicenow
The GitHub REST API gives you programmatic access to repositories, issues, pull requests, users, and webhooks — but before you write a single API call, you need to make the right authentication decision. Choose the wrong one and you'll either hit per-user rate limits at scale or spend weeks rebuilding your auth layer.
Quick answer: For production product integrations, use GitHub Apps — they authenticate at the installation level (not per-user), receive 15,000 API requests/hour per installation, and support fine-grained permissions. Use OAuth Apps when you need to act as the user. Use Personal Access Tokens for scripts and one-off automation only.
This guide covers everything you need to build a complete GitHub API integration: authentication setup for all three methods, REST API endpoints for issues, repos, users, and labels, webhook configuration with signature verification, rate limits, and three real-world integration patterns with working Python code.
If your product needs to support GitHub alongside other issue trackers like Jira, Linear, or Asana, there's a unified approach worth knowing about — covered in the Building with Knit section.
GitHub exposes three API surfaces. Understanding which to use before you start building saves significant refactoring later.
REST API is the right choice for the vast majority of product integrations. The GraphQL API is useful when you need to fetch nested relationships (issues with their labels, assignees, and comments) in a single query and want to avoid over-fetching. Webhooks are event-driven and complement REST — they notify your server when something happens, then you call REST to get full details.
The GitHub REST API base URL is https://api.github.com. All endpoints accept and return JSON. The API version is specified via the X-GitHub-Api-Version header — always pin this to avoid breaking changes:
GET /repos/{owner}/{repo}/issues
Authorization: Bearer {token}
Accept: application/vnd.github+json
X-GitHub-Api-Version: 2022-11-28
This is the most consequential decision in any GitHub integration. Here's what each approach actually means for a production system:
GitHub Apps is the most powerful option and the right default for any B2B product integration. A GitHub App is installed on an organization or repository, not tied to a user account, and generates short-lived installation tokens.
Step 1: Register a GitHub App
Go to Settings → Developer settings → GitHub Apps → New GitHub App. Key fields:
GitHub generates a private key (.pem file) and an App ID. Store both securely.
Step 2: Generate a JWT
import jwt
import time
from pathlib import Path
def generate_github_jwt(app_id: str, private_key_path: str) -> str:
private_key = Path(private_key_path).read_text()
payload = {
"iat": int(time.time()) - 60, # Issued at (60s buffer for clock skew)
"exp": int(time.time()) + (10 * 60), # Expires in 10 minutes (max)
"iss": app_id
}
return jwt.encode(payload, private_key, algorithm="RS256")Step 3: Exchange the JWT for an Installation Token
import requests
def get_installation_token(jwt_token: str, installation_id: str) -> str:
"""
Installation tokens expire after 1 hour.
Cache and refresh them before expiry in production.
"""
response = requests.post(
f"https://api.github.com/app/installations/{installation_id}/access_tokens",
headers={
"Authorization": f"Bearer {jwt_token}",
"Accept": "application/vnd.github+json",
"X-GitHub-Api-Version": "2022-11-28"
}
)
data = response.json()
return data["token"] # This is your installation access tokenThe installation token is used exactly like any other Bearer token for subsequent API calls. Because it expires in 1 hour, build a caching layer that refreshes tokens 5 minutes before expiry.
Step 4: Redirect users to install your GitHub App
https://github.com/apps/{app-name}/installations/newAfter installation, GitHub redirects to your callback URL with an installation_id. Store this per-customer in your database.
If you're building a product that needs to support GitHub alongside other issue trackers — Jira, Linear, Asana — managing GitHub Apps installation tokens per customer, while also handling different auth flows for every other tool, quickly becomes a significant engineering overhead. Knit handles GitHub auth (OAuth and PAT) and normalises the API surface across all your supported ticketing tools, so you write the integration once. See getknit.dev/integration/github.
Use OAuth Apps when your integration needs to act as the user — for example, creating issues on behalf of the authenticated user, or reading private repos the user has access to.
OAuth Flow:
# Step 1: Redirect user to GitHub
auth_url = (
"https://github.com/login/oauth/authorize"
f"?client_id={CLIENT_ID}"
f"&redirect_uri={REDIRECT_URI}"
f"&scope=repo,read:user"
f"&state={generate_csrf_token()}" # Always validate state to prevent CSRF
)
# Step 2: Exchange code for token (after redirect back)
def exchange_code_for_token(code: str) -> str:
response = requests.post(
"https://github.com/login/oauth/access_token",
data={
"client_id": CLIENT_ID,
"client_secret": CLIENT_SECRET,
"code": code
},
headers={"Accept": "application/json"}
)
return response.json()["access_token"]OAuth App tokens do not expire automatically, but users can revoke them at any time. Build webhook listeners for the github_app_authorization event to detect revocations and clean up stored tokens accordingly.
PATs are the simplest option — generate one in Settings → Developer settings → Personal access tokens — but they're fundamentally single-user. All API calls are attributed to the token owner, which creates audit and attribution problems in multi-tenant products. Use PATs for CI/CD pipelines, internal automation, and developer tooling only.
Fine-grained PATs (currently in beta) allow scoping to specific repositories and actions, making them a reasonable choice for tightly controlled automation scenarios.
Issues are the core resource for most GitHub integrations. GitHub's Issues API also returns pull requests — always check for the pull_request field if you want to exclude PRs.
List issues in a repository:
def list_issues(owner: str, repo: str, token: str, state: str = "open") -> list:
"""
Returns up to 100 issues per page.
Iterate Link headers for full pagination.
pull_request field is present on PRs — filter if needed.
"""
issues = []
url = f"https://api.github.com/repos/{owner}/{repo}/issues"
params = {"state": state, "per_page": 100}
headers = {
"Authorization": f"Bearer {token}",
"Accept": "application/vnd.github+json",
"X-GitHub-Api-Version": "2022-11-28"
}
while url:
response = requests.get(url, params=params, headers=headers)
response.raise_for_status()
issues.extend([i for i in response.json() if "pull_request" not in i])
# GitHub returns pagination via Link header
link_header = response.headers.get("Link", "")
url = extract_next_url(link_header) # Parse rel="next" from header
params = {} # Next URL already includes params
return issuesCreate an issue:
def create_issue(owner: str, repo: str, token: str,
title: str, body: str, labels: list = None,
assignees: list = None) -> dict:
response = requests.post(
f"https://api.github.com/repos/{owner}/{repo}/issues",
headers={
"Authorization": f"Bearer {token}",
"Accept": "application/vnd.github+json",
"X-GitHub-Api-Version": "2022-11-28"
},
json={
"title": title,
"body": body,
"labels": labels or [],
"assignees": assignees or []
}
)
response.raise_for_status()
return response.json() # Returns full issue object including issue number and URLUpdate an issue (assign, label, close):
def update_issue(owner: str, repo: str, issue_number: int, token: str, **fields) -> dict:
"""
Supports: title, body, state (open/closed), labels, assignees, milestone.
"""
response = requests.patch(
f"https://api.github.com/repos/{owner}/{repo}/issues/{issue_number}",
headers={
"Authorization": f"Bearer {token}",
"Accept": "application/vnd.github+json",
"X-GitHub-Api-Version": "2022-11-28"
},
json=fields
)
response.raise_for_status()
return response.json()# List repositories for an organization
GET /orgs/{org}/repos?type=all&per_page=100
# Get a specific repository
GET /repos/{owner}/{repo}
# List repository collaborators
GET /repos/{owner}/{repo}/collaborators# Get the authenticated user
GET /user
# Get a user by username
GET /users/{username}
# List organization members
GET /orgs/{org}/members# List all labels in a repository
GET /repos/{owner}/{repo}/labels
# Create a label
POST /repos/{owner}/{repo}/labels
Body: {"name": "bug", "color": "d73a4a", "description": "Something isn't working"}
# List milestones
GET /repos/{owner}/{repo}/milestones?state=openWebhooks let GitHub push events to your server rather than requiring you to poll the API. Configure them in repository or organization settings, or programmatically via the API.
Create a webhook via the API:
def create_webhook(owner: str, repo: str, token: str,
payload_url: str, secret: str, events: list) -> dict:
response = requests.post(
f"https://api.github.com/repos/{owner}/{repo}/hooks",
headers={
"Authorization": f"Bearer {token}",
"Accept": "application/vnd.github+json",
"X-GitHub-Api-Version": "2022-11-28"
},
json={
"name": "web",
"active": True,
"events": events, # e.g. ["issues", "pull_request", "push"]
"config": {
"url": payload_url,
"content_type": "json",
"secret": secret,
"insecure_ssl": "0"
}
}
)
response.raise_for_status()
return response.json()Every GitHub webhook payload includes an X-Hub-Signature-256 header. You must verify this on every incoming request — skip this step and your endpoint can be spoofed by anyone who discovers its URL.
import hmac
import hashlib
from flask import Flask, request, abort
app = Flask(__name__)
WEBHOOK_SECRET = b"your-webhook-secret"
@app.route("/webhook/github", methods=["POST"])
def handle_github_webhook():
# Verify signature before processing anything
signature_header = request.headers.get("X-Hub-Signature-256", "")
if not signature_header.startswith("sha256="):
abort(400, "Missing or malformed signature")
expected_sig = hmac.new(
WEBHOOK_SECRET,
request.data, # Raw bytes — don't use parsed JSON here
hashlib.sha256
).hexdigest()
received_sig = signature_header[7:] # Strip "sha256=" prefix
# Constant-time comparison prevents timing attacks
if not hmac.compare_digest(expected_sig, received_sig):
abort(401, "Invalid signature")
# Safe to process the payload now
payload = request.json
event_type = request.headers.get("X-GitHub-Event")
if event_type == "issues":
handle_issue_event(payload)
elif event_type == "pull_request":
handle_pr_event(payload)
return "", 200
def handle_issue_event(payload: dict):
action = payload["action"] # opened, closed, labeled, assigned, etc.
issue = payload["issue"]
repo = payload["repository"]
if action == "opened":
print(f"New issue #{issue['number']} in {repo['full_name']}: {issue['title']}")Supported webhook events for issue integrations: issues, issue_comment, label, milestone, pull_request, push, repository.
GitHub retries failed webhook deliveries with exponential backoff for up to 72 hours. Return a 200 response immediately on receipt and process the payload asynchronously to avoid delivery timeouts (GitHub expects a response within 10 seconds).
Rate limit status is returned in every response:
X-RateLimit-Limit: 5000
X-RateLimit-Remaining: 4823
X-RateLimit-Reset: 1747353600 # Unix timestamp when the limit resets
X-RateLimit-Used: 177When X-RateLimit-Remaining reaches 0, GitHub returns 403 Forbidden with a Retry-After header. Build rate limit handling into your HTTP client from the start:
def github_request(url: str, token: str, **kwargs) -> requests.Response:
response = requests.get(url, headers={
"Authorization": f"Bearer {token}",
"Accept": "application/vnd.github+json",
"X-GitHub-Api-Version": "2022-11-28"
}, **kwargs)
if response.status_code == 403 and "X-RateLimit-Remaining" in response.headers:
if response.headers["X-RateLimit-Remaining"] == "0":
reset_time = int(response.headers["X-RateLimit-Reset"])
wait = max(0, reset_time - int(time.time())) + 5 # 5s buffer
time.sleep(wait)
return github_request(url, token, **kwargs) # Retry
response.raise_for_status()
return responseFor secondary rate limits (triggered by too many concurrent requests), watch for Retry-After in the response headers and honor it exactly.
The most common integration pattern: pull issues from one or more GitHub repos and display or sync them inside your product.
import requests
import time
def sync_all_issues(installations: list, token_manager) -> list:
"""
Full issue sync across multiple repositories.
Returns a normalised list of issues for storage.
"""
all_issues = []
for installation in installations:
token = token_manager.get_token(installation["id"]) # Cached + auto-refreshed
for repo in installation["repos"]:
owner, name = repo["owner"], repo["name"]
page_url = f"https://api.github.com/repos/{owner}/{name}/issues"
params = {"state": "all", "per_page": 100}
while page_url:
resp = requests.get(page_url, params=params, headers={
"Authorization": f"Bearer {token}",
"Accept": "application/vnd.github+json",
"X-GitHub-Api-Version": "2022-11-28"
})
resp.raise_for_status()
for issue in resp.json():
if "pull_request" in issue:
continue # Skip PRs
all_issues.append({
"id": issue["number"],
"title": issue["title"],
"state": issue["state"],
"assignees": [a["login"] for a in issue["assignees"]],
"labels": [l["name"] for l in issue["labels"]],
"url": issue["html_url"],
"created_at": issue["created_at"],
"updated_at": issue["updated_at"],
"repo": f"{owner}/{name}"
})
# Parse next page from Link header
link = resp.headers.get("Link", "")
next_url = next(
(p.split(";")[0].strip("<>") for p in link.split(",")
if 'rel="next"' in p), None
)
page_url = next_url
params = {}
return all_issuesWhen a user creates a task in your product and wants it to appear in GitHub:
def create_github_issue_from_task(task: dict, repo_config: dict, token: str) -> dict:
"""
Maps your product's task model to a GitHub issue.
Returns the created issue with GitHub's issue number for cross-referencing.
"""
# Map your assignees to GitHub usernames
github_assignees = [
repo_config["user_mapping"].get(uid)
for uid in task.get("assignee_ids", [])
if repo_config["user_mapping"].get(uid)
]
# Map your labels/tags to GitHub label names
github_labels = [
repo_config["label_mapping"].get(tag)
for tag in task.get("tags", [])
if repo_config["label_mapping"].get(tag)
]
response = requests.post(
f"https://api.github.com/repos/{repo_config['owner']}/{repo_config['repo']}/issues",
headers={
"Authorization": f"Bearer {token}",
"Accept": "application/vnd.github+json",
"X-GitHub-Api-Version": "2022-11-28"
},
json={
"title": task["title"],
"body": f"{task['description']}\n\n---\n*Created via {task['source']}*",
"assignees": github_assignees,
"labels": github_labels,
"milestone": repo_config.get("milestone_id")
}
)
response.raise_for_status()
github_issue = response.json()
# Store the GitHub issue number in your database for future updates
return {
"github_issue_number": github_issue["number"],
"github_issue_url": github_issue["html_url"],
"github_issue_id": github_issue["id"]
}Keep issue state in sync in real time — when a GitHub issue is closed, close the linked item in your product; and vice versa.
# Webhook handler (GitHub → your product)
def handle_issue_state_change(payload: dict):
action = payload["action"]
if action not in ("closed", "reopened"):
return # Only care about state changes
github_issue_id = payload["issue"]["id"]
new_state = "closed" if action == "closed" else "open"
# Look up the linked task in your DB
task_id = db.get_task_by_github_id(github_issue_id)
if task_id:
db.update_task_state(task_id, new_state)
print(f"Synced GitHub issue {github_issue_id} → Task {task_id}: {new_state}")
# REST handler (your product → GitHub)
def close_github_issue_for_task(task_id: str, token: str):
github_info = db.get_github_info_for_task(task_id)
if not github_info:
return
update_issue(
owner=github_info["owner"],
repo=github_info["repo"],
issue_number=github_info["issue_number"],
token=token,
state="closed"
)GitHub Apps auth — JWTs, per-installation tokens that expire hourly, managing token refresh across multiple customer installations — is the part of a GitHub integration that adds the most engineering overhead for the least user-visible value.
Knit provides a unified ticketing API that handles GitHub authentication (OAuth and Personal Access Token flows) for your customers. Instead of building and maintaining the OAuth consent flow, token storage, and refresh logic, your customers connect their GitHub account once through Knit's auth layer. You call Knit's normalised endpoints using a single set of headers:
Authorization: Bearer {your-knit-api-token}
X-Knit-Integration-Id: {customer-integration-id}This is particularly valuable if your product supports GitHub alongside other issue trackers — Jira, Linear, Asana, Zendesk, and more are all available through the same Knit interface, so you build the integration pattern once and it works across all of them.
The Knit APIs available for GitHub:
Example: fetch all teams in a GitHub org via Knit
import requests
def get_github_teams_via_knit(knit_token: str, integration_id: str,
account_id: str) -> list:
"""
Returns GitHub teams for the given org (account_id).
No JWT generation, no installation tokens, no token refresh logic.
"""
response = requests.get(
"https://api.getknit.dev/v1.0/ticketing/groups",
headers={
"Authorization": f"Bearer {knit_token}",
"X-Knit-Integration-Id": integration_id
},
params={"accountId": account_id}
)
response.raise_for_status()
data = response.json()
# Cursor-based pagination built in
groups = data["data"]["groups"]
next_cursor = data["data"]["pagination"].get("next")
while next_cursor:
response = requests.get(
"https://api.getknit.dev/v1.0/ticketing/groups",
headers={
"Authorization": f"Bearer {knit_token}",
"X-Knit-Integration-Id": integration_id
},
params={"accountId": account_id, "cursor": next_cursor}
)
page = response.json()
groups.extend(page["data"]["groups"])
next_cursor = page["data"]["pagination"].get("next")
return groups→ See the full GitHub integration on Knit: getknit.dev/integration/github
→ Knit's ticketing API docs: developers.getknit.dev
If you're building a GitHub integration from scratch, this is the order that minimises rework:
installation_id on callback, and store it per customer.
What is the difference between GitHub Apps, OAuth Apps, and Personal Access Tokens?
GitHub Apps are the recommended approach for building integrations — they authenticate as the app itself, support fine-grained permissions, and receive 15,000 API requests/hour per installation. OAuth Apps authenticate as a user and are limited to the user's rate limit of 5,000 requests/hour. Personal Access Tokens are best for scripts and automation where a single user account controls access, but they do not scale across multiple users.
How do I authenticate with the GitHub REST API?
Pass your token in the Authorization header: Authorization: Bearer {token}. For GitHub Apps, generate a JWT signed with your app's private key, then exchange it for an installation access token via POST /app/installations/{installation_id}/access_tokens. For OAuth Apps and PATs, pass the token directly. Unauthenticated requests are limited to 60 requests per hour; authenticated requests get 5,000 per hour.
What are the GitHub REST API rate limits?
Unauthenticated requests: 60 per hour. Authenticated OAuth Apps and PATs: 5,000 requests per hour. GitHub Apps using installation tokens: 15,000 requests per hour per installation. Search API requests: 30 per minute for authenticated users, 10 per minute for unauthenticated. Rate limit status is returned on every response via X-RateLimit-Remaining and X-RateLimit-Reset headers.
How do GitHub webhooks work?
GitHub webhooks send HTTP POST payloads to a URL you configure whenever a subscribed event occurs. Every payload includes an X-Hub-Signature-256 header — an HMAC-SHA256 signature of the raw request body using your webhook secret. You must verify this signature on every incoming request. GitHub delivers at most one webhook per event and retries for up to 72 hours on delivery failure.
How do I list all issues from a GitHub repository via the API?
Use GET /repos/{owner}/{repo}/issues. By default this returns open issues and pull requests. Filter with state=open, state=closed, or state=all. Use labels, assignee, and milestone query params to narrow results. Results are paginated at 30 items per page by default — use per_page (max 100) and the Link response header to navigate pages. Pull requests are included in the issues endpoint; filter them out by checking for the pull_request field.
What is the difference between the GitHub REST API and GraphQL API?
The GitHub REST API has separate endpoints per resource and is the standard choice for most integrations. The GitHub GraphQL API (v4) lets you request exactly the fields you need in a single query, reducing over-fetching. Use REST when building straightforward CRUD integrations. Use GraphQL when you need to fetch deeply nested relationships — issues with their comments, labels, and assignees — in a single request.
How do I verify a GitHub webhook signature?
Compute HMAC-SHA256 of the raw request body using your webhook secret as the key. Compare this digest to the value in the X-Hub-Signature-256 header (prefixed with sha256=). Use a constant-time comparison function (like hmac.compare_digest in Python) to prevent timing attacks. Never process webhook payloads before verifying the signature.
Is there a simpler way to integrate GitHub without managing OAuth or GitHub Apps authentication myself?
Yes. Knit provides a unified ticketing API that handles GitHub authentication (OAuth and PAT) for you. Instead of implementing the OAuth flow, managing token storage, or dealing with per-user credentials, your customers connect their GitHub account once through Knit's auth layer. You then call Knit's normalised endpoints — for organisations, users, teams, and labels — without writing auth infrastructure. This is especially useful if you also need to support Jira, Linear, or Asana alongside GitHub, as Knit's same API surface covers all of them. → getknit.dev/integration/github
Slack has four API surfaces — Web API, Events API, Incoming Webhooks, and Socket Mode — and picking the wrong one is the most common reason Slack integrations need to be rebuilt. This guide explains what each surface does, which one your integration actually needs, and how to work with the key Web API endpoints (chat.postMessage, chat.update, conversations.list, users.lookupByEmail) with real code examples.
Quick answer: For most product integrations — sending notifications, DMs, interactive messages, slash commands — use the Web API with a bot token. Use the Events API when you need Slack to push events to your server in real time. Use Incoming Webhooks only for simple, one-way alerts to a fixed channel.
If you've ever searched "how to integrate with Slack," you've probably landed on a page that explains how to post a message using an Incoming Webhook — and wondered why there are three other APIs that seem to do something similar.
That confusion is real, and it costs engineering teams time. Slack has four distinct API surfaces: the Web API, the Events API, Incoming Webhooks, and Socket Mode. Each one exists for a different reason. Picking the wrong one means either building something that breaks when Slack's terms change, or over-engineering a simple notification system.
This guide cuts through that. By the end, you'll know exactly which Slack API surface your integration needs, how OAuth works, how the key endpoints behave, and how to handle slash commands and interactive messages. There's also a section on building via Knit, if you'd rather skip managing Slack auth and token lifecycle yourself and if you plan to add a ms teams integration later as it solves for both in one go.
The Slack Web API is a standard HTTPS REST API. You make requests to https://slack.com/api/{method}, pass a bot token in the Authorization header, and get JSON back. It is the foundation of most serious Slack integrations — over 100 methods are available covering messaging, user management, channels, files, and more.
Use it when you need to initiate actions from your server: send messages, look up users, list channels, update a message after it's been sent, or respond to interactions.
The Events API flips the direction. Instead of your server calling Slack, Slack calls your server via HTTP POST whenever something happens — a message is posted, a user joins a channel, a reaction is added, and so on. You register a public URL, Slack sends events to it, and you process them.
Use it when your integration needs to react to things happening in Slack: syncing messages to an external system, triggering workflows when users mention a keyword, or logging activity.
Incoming Webhooks are the simplest option. During app installation, Slack gives you a URL. You POST JSON to that URL and a message appears in a pre-configured channel. There's no OAuth flow to manage at runtime, no tokens to refresh — just one URL.
Use them when you want to push simple notifications from an external system into a single channel: CI/CD build alerts, server monitoring notifications, daily digest messages.
The constraint: each webhook is tied to one channel at install time. You can't dynamically choose where to send the message, and you can't read data or respond to events.
Socket Mode lets your app receive events over a persistent WebSocket connection rather than an HTTP endpoint. This means Slack doesn't need to reach a public URL — useful during development, or when your app runs behind a firewall or in an environment where exposing a port isn't possible.
Use it for local development or for apps that live in environments without a public-facing URL. In production, the Events API is generally preferred.
Start at api.slack.com/apps. Create a new app, either from scratch or from an app manifest. An app manifest is a YAML or JSON file that declares your app's permissions, event subscriptions, and slash commands — useful for version-controlling your app configuration.
When your app is installed to a workspace, Slack issues two types of tokens:
xoxb-...): Acts on behalf of your app's bot user. This is what most integrations use. The bot can only access channels it's been added to.xoxp-...): Acts on behalf of the user who installed the app. Has access to that user's data. Generally only needed if your integration requires user-level permissions (e.g., reading someone's private messages on their behalf).For most integration use cases — sending notifications, managing channels, looking up users — a bot token is sufficient and the safer choice.
Scopes define what your app can do. You declare required scopes when creating the app, and users see them listed when installing. Request only what you need — over-permissioned apps create friction at install time.
Common scopes for a messaging integration:
client_id, requested scopes, and a redirect_uri.redirect_uri with a temporary code.code for an access token via https://slack.com/api/oauth.v2.access.access_token (and team_id) securely. This token doesn't expire — but users can revoke it, and you should handle token_revoked events.All Web API calls follow the same pattern:
POST https://slack.com/api/{method}
Authorization: Bearer xoxb-your-bot-token
Content-Type: application/jsonEvery response includes an "ok" boolean. If "ok": false, the "error" field tells you why.
{ "ok": false, "error": "channel_not_found" }Always check ok before using the response body.
chat.postMessageThe workhorse of most Slack integrations. Sends a message to a channel — or a DM when you pass a user ID as the channel.
POST https://slack.com/api/chat.postMessage
Authorization: Bearer xoxb-your-bot-token
Content-Type: application/json{
"channel": "C0123456789",
"blocks": [
{
"type": "section",
"text": {
"type": "mrkdwn",
"text": "*New order received* 🎉\nOrder #1042 from Acme Corp — $4,200"
}
}
]
}Response:
{
"ok": true,
"ts": "1715000000.000100",
"channel": "C0123456789"
}Save the ts (timestamp) and channel from the response. Together, these uniquely identify the message and are required to update it later.
The blocks array uses Slack's Block Kit — a structured layout system that lets you build rich messages with sections, buttons, images, and dropdowns. Plain text is also accepted but blocks give you far more control.
chat.updateWhen a status changes — a build completes, an order ships, an approval is actioned — update the original message rather than posting a new one. This keeps channels clean.
{
"channel": "C0123456789",
"ts": "1715000000.000100",
"blocks": [
{
"type": "section",
"text": {
"type": "mrkdwn",
"text": "*Order #1042 — Shipped* ✅\nTracking: UPS 1Z999AA10123456784"
}
}
]
}Pass "as_user": true if you want the update to appear as coming from the user rather than the bot.
conversations.listRetrieves public and private channels. Useful for letting users select a channel in your app's UI without hardcoding channel IDs.
GET https://slack.com/api/conversations.list?types=public_channel,private_channel&limit=200
Authorization: Bearer xoxb-your-bot-token{
"channels": [
{ "id": "C0123456789", "name": "engineering-alerts", "is_private": false },
{ "id": "C0987654321", "name": "finance-approvals", "is_private": true }
],
"response_metadata": {
"next_cursor": "dGVhbTpDMDYxRkE3OTM="
}
}Paginate using the cursor query parameter: pass the next_cursor value from response_metadata as the cursor in your next request. Continue until next_cursor is empty.
users.list and users.lookupByEmailTwo options depending on what you have:
users.list — returns all workspace members with pagination. Useful for building a local user cache or populating a dropdown.
GET https://slack.com/api/users.list?limit=200{
"members": [
{
"id": "U0123456789",
"is_bot": false,
"deleted": false,
"profile": { "email": "sarah@acme.com" }
}
],
"response_metadata": { "next_cursor": "..." }
}Filter out bots (is_bot: true) and deactivated users (deleted: true) before storing.
users.lookupByEmail — the faster option when you already know the email. One call, one user.
GET https://slack.com/api/users.lookupByEmail?email=sarah@acme.com{
"ok": true,
"user": { "id": "U0123456789" }
}Use the returned id directly as the channel in chat.postMessage to send a direct message to that user.
Slash commands let users trigger actions in your external system by typing /command in any Slack channel. When a user fires one, Slack sends a POST request to your registered endpoint within 3 seconds — if your response takes longer, Slack will show an error.
{
"eventId": "evt_01abc",
"eventType": "slash_command",
"eventData": {
"command": "/report",
"text": "Q1 2026",
"keyCommand": "report",
"argumentCommand": "Q1 2026",
"userId": "U0123456789",
"teamId": "T0123456789",
"channelId": "C0123456789",
"responseUrl": "https://hooks.slack.com/commands/..."
}
}Key fields:
command — the slash command itself (e.g., /report)text — everything the user typed after the commandkeyCommand — the command name without the slashargumentCommand — the arguments portion (everything after the command name)userId — who triggered itresponseUrl — a URL you can POST a delayed response to (valid for 30 minutes)If your command triggers a long-running operation, acknowledge immediately with a simple response, then POST the actual result to responseUrl when ready:
// Immediate acknowledgment (within 3s)
{
"commandResponse": {
"text": "Generating your Q1 report, hang tight..."
}
}// Delayed response via responseUrl (up to 30 min later)
{
"commandResponse": {
"blocks": [
{
"type": "section",
"text": { "type": "mrkdwn", "text": "*Q1 2026 Report*\nRevenue: $2.4M | Growth: +18%" }
}
]
}
}Slack rate-limits the Web API by method, using a tier system:
When you hit a limit, Slack responds with HTTP 429 and a Retry-After header indicating how many seconds to wait. Always implement retry logic with exponential backoff. For high-volume messaging (bulk notifications, digest sends), queue messages and pace them against the per-channel limit.
A common need: your backend event has a user's email and you need to reach them directly in Slack.
import requests
SLACK_TOKEN = "xoxb-your-bot-token"
HEADERS = {"Authorization": f"Bearer {SLACK_TOKEN}", "Content-Type": "application/json"}
def send_dm_by_email(email: str, message: str):
# Step 1: Resolve email → user ID
lookup = requests.get(
"https://slack.com/api/users.lookupByEmail",
params={"email": email},
headers=HEADERS
).json()
if not lookup.get("ok"):
raise Exception(f"User not found: {lookup.get('error')}")
user_id = lookup["user"]["id"]
# Step 2: Send DM (user ID is used as the channel)
response = requests.post(
"https://slack.com/api/chat.postMessage",
headers=HEADERS,
json={
"channel": user_id,
"blocks": [
{"type": "section", "text": {"type": "mrkdwn", "text": message}}
]
}
).json()
if not response.get("ok"):
raise Exception(f"Message failed: {response.get('error')}")
return response["ts"] # Save for later updatesPost a message with Approve/Decline buttons, then update it once the manager acts.
def post_approval_request(channel: str, request_details: str):
response = requests.post(
"https://slack.com/api/chat.postMessage",
headers=HEADERS,
json={
"channel": channel,
"blocks": [
{
"type": "section",
"text": {"type": "mrkdwn", "text": f"*Approval Request*\n{request_details}"}
},
{
"type": "actions",
"elements": [
{"type": "button", "text": {"type": "plain_text", "text": "✅ Approve"},
"action_id": "approve", "style": "primary"},
{"type": "button", "text": {"type": "plain_text", "text": "❌ Decline"},
"action_id": "decline", "style": "danger"}
]
}
]
}
).json()
return {"ts": response["ts"], "channel": response["channel"]}
def resolve_approval(ts: str, channel: str, approved: bool, actioned_by: str):
status = "✅ Approved" if approved else "❌ Declined"
requests.post(
"https://slack.com/api/chat.update",
headers=HEADERS,
json={
"channel": channel,
"ts": ts,
"blocks": [
{
"type": "section",
"text": {"type": "mrkdwn", "text": f"*Approval Request* — {status}\nActioned by: {actioned_by}"}
}
]
}
)Route different /commands to the right handler in your backend.
from flask import Flask, request, jsonify
app = Flask(__name__)
HANDLERS = {
"report": handle_report_command,
"ticket": handle_ticket_command,
"status": handle_status_command,
}
@app.route("/slack/commands", methods=["POST"])
def slack_command():
payload = request.get_json()
key_command = payload["eventData"]["keyCommand"]
args = payload["eventData"]["argumentCommand"]
user_id = payload["eventData"]["userId"]
response_url = payload["eventData"]["responseUrl"]
handler = HANDLERS.get(key_command)
if not handler:
return jsonify({"commandResponse": {"text": f"Unknown command: `/{key_command}`"}})
# Acknowledge immediately, process async
handler(args, user_id, response_url)
return jsonify({"commandResponse": {"text": "On it — give me a moment..."}})Managing OAuth installs, token storage, token refresh, and multi-workspace support adds significant overhead before you've written a line of business logic. Knit handles the Slack integration infrastructure — auth, token lifecycle, and a normalised API layer — so you can focus on what your integration actually does.
Here's what Knit exposes for Slack:
POST to chat.postMessage behind a single Knit endpoint. Pass a channel ID and a blocks array. The response returns ts and channel — both stored by Knit for downstream operations.
Use cases: Order notifications, incident alerts, digest messages, CRM event triggers, approval requests.
Updates an existing message using its ts + channel pair. Pass as_user: true to update as the installing user rather than the bot.
Use cases: Live build status boards, approval resolution, updating order/ticket status without channel noise.
Wraps conversations.list with cursor-based pagination handled automatically. Returns id, name, and is_private for each channel. Supports filtering by types.
Use cases: Channel pickers in your UI, compliance audits, onboarding automation (add new users to default channels).
Retrieves the DM channel IDs for users the bot has existing conversations with. Useful for mapping your internal user records to Slack DM channels without repeatedly calling users.lookupByEmail.
Single call to resolve an email address to a Slack user ID — the equivalent of users.lookupByEmail. Use the returned id as the channel in a Send Message call to DM that user directly.
Use cases: HR onboarding flows, IT support ticket updates, sales/support follow-up DMs.
Register a slash command and a destination URL. When a user fires the command, Knit forwards the full event payload — including command, text, keyCommand, argumentCommand, userId, channelId, and responseUrl — to your endpoint, signed with an X-Knit-Signature header for verification.
Your endpoint returns a commandResponse object with blocks and/or text, and Knit delivers it back to Slack. For async operations, use the responseUrl from the forwarded payload.
Use cases: /report, /ticket, /status, /approve — any command that needs to query or trigger something in your backend.
If you're starting a Slack integration from scratch, here's a sensible sequence:
chat.postMessage — get a working notification flowing before adding complexity.chat.update once you have messages being sent — live-updating messages is one of the highest-value Slack UX patterns.If you're integrating Slack as one of several tools in a larger product and don't want to manage per-workspace OAuth and token storage for each one, Knit's Slack integration gives you all six of the above capabilities behind a single authenticated API — and adds every other integration you support through the same interface.
The most common mistake in Slack integrations is starting with Incoming Webhooks because they're simple, then realising six months later that you need to post to different channels dynamically, update messages, or handle slash commands — and having to rebuild. Start with the Web API unless your use case genuinely only needs fixed-channel notifications.
What is the difference between the Slack Web API and the Events API?
The Web API is request-driven: your server calls Slack to send messages, retrieve data, or update content. The Events API is event-driven: Slack calls your server when something happens in a workspace. Most integrations use both — the Web API to act, the Events API to react.
Which Slack API should I use to send a message?
Use chat.postMessage via the Slack Web API. Authenticate with a bot token (xoxb-), POST to https://slack.com/api/chat.postMessage with a channel ID and a blocks or text body. For direct messages, use the recipient's Slack user ID as the channel value.
How do I send a direct message to a Slack user from my application?
First look up the user's Slack ID by calling users.lookupByEmail with their email address. Then call chat.postMessage using that user ID as the channel parameter. The user will receive the message in their DMs from your app's bot.
What are Slack OAuth scopes and which ones do I need?
Scopes are permissions your app requests when a user installs it. For a basic messaging integration you need: chat:write (post messages), users:read.email (look up users by email), channels:read (list channels), and commands (if you're adding slash commands). Only request scopes you actually use.
What is Slack Socket Mode and when should I use it?
Socket Mode lets your app receive Slack events over a WebSocket connection instead of a public HTTP endpoint. Use it during local development when you don't have a public URL, or in production environments behind a firewall. For public-facing production apps, the Events API over HTTP is the standard approach.
Does the Slack Web API have rate limits?
Yes. Slack uses a tier system: chat.postMessage is Tier 3 (~50 requests per minute per channel), conversations.list is Tier 2 (~20 req/min), and users.lookupByEmail is Tier 4 (~100 req/min). Exceeding limits returns HTTP 429 with a Retry-After header. Always implement exponential backoff retry logic.
How do I handle Slack slash commands in my backend?
Register your slash command in your Slack app settings with an endpoint URL. Slack will POST a payload to that URL whenever the command is used. You must respond within 3 seconds — for longer operations, return an immediate acknowledgment and use the responseUrl from the payload to send the actual response asynchronously.
Deep dives into the Knit product and APIs

Are you in the market for Nango alternatives that can power your API integration solutions? In this article, we’ll explore five top platforms—Knit, Merge.dev, Apideck, Paragon, and Tray Embedded—and dive into their standout features, pros, and cons. Discover why Knit has become the go-to option for B2B SaaS integrations, helping companies simplify and secure their customer-facing data flows.
Nango is an open-source embedded integration platform that helps B2B SaaS companies quickly connect various applications via a single interface. Its streamlined setup and developer-friendly approach can accelerate time-to-market for customer-facing integrations. However, coverage is somewhat limited compared to broader unified API platforms—particularly those offering deeper category focus and event-driven architectures.
Nango also relies heavily on open source communities for adding new connectors which makes connector scaling less predictable fo complex or niche use cases.
Pros (Why Choose Nango):
Cons (Challenges & Limitations):
Now let’s look at a few Nango alternatives you can consider for scaling your B2B SaaS integrations, each with its own unique blend of coverage, security, and customization capabilities.

Overview
Knit is a unified API platform specifically tailored for B2B SaaS integrations. By consolidating multiple applications—ranging from CRM to HRIS, Recruitment, Communication, and Accounting—via a single API, Knit helps businesses reduce the complexity of API integration solutions while improving efficiency. See how Knit compares directly to Nango →
Key Features
Pros

Overview
Merge.dev delivers unified APIs for crucial categories like HR, payroll, accounting, CRM, and ticketing systems—making it a direct contender among top Nango alternatives.
Key Features
Pros
Cons

Overview
Apideck offers a suite of API integration solutions that give developers access to multiple services through a single integration layer. It’s well-suited for categories like HRIS and ATS.
Key Features
Pros
Cons

Overview
Paragon is an embedded integration platform geared toward building and managing customer-facing integrations for SaaS businesses. It stands out with its visual workflow builder, enabling lower-code solutions.
Key Features
Pros
Cons

Overview
Tray Embedded is another formidable competitor in the B2B SaaS integrations space. It leverages a visual workflow builder to enable embedded, native integrations that clients can use directly within their SaaS platforms.
Key Features
Pros
Cons
When searching for Nango alternatives that offer a streamlined, secure, and B2B SaaS-focused integration experience, Knit stands out. Its unified API approach and event-driven architecture protect end-user data while accelerating the development process. For businesses seeking API integration solutions that minimize complexity, boost security, and enhance scalability, Knit is a compelling choice.

Whether you are a SaaS founder/ BD/ CX/ tech person, you know how crucial data safety is to close important deals. If your customer senses even the slightest risk to their internal data, it could be the end of all potential or existing collaboration with you.
But ensuring complete data safety — especially when you need to integrate with multiple 3rd party applications to ensure smooth functionality of your product — can be really challenging.
While a unified API makes it easier to build integrations faster, not all unified APIs work the same way.
In this article, we will explore different data sync strategies adopted by different unified APIs with the examples of Finch API and Knit — their mechanisms, differences and what you should go for if you are looking for a unified API solution.
Let’s dive deeper.
But before that, let us first revisit the primary components of a unified API and how exactly they make building integration easier.
As we have mentioned in our detailed guide on Unified APIs,
“A unified API aggregates several APIs within a specific category of software into a single API and normalizes data exchange. Unified APIs add an additional abstraction layer to ensure that all data models are normalized into a common data model of the unified API which has several direct benefits to your bottom line”.
The mechanism of a unified API can be broken down into 4 primary elements —
Every unified API — whether its Finch API, Merge API or Knit API — follows certain protocols (such as OAuth) to guide your end users authenticate and authorize access to the 3rd party apps they already use to your SaaS application.
Not all apps within a single category of software applications have the same data models. As a result, SaaS developers often spend a great deal of time and effort into understanding and building upon each specific data model.
A unified API standardizes all these different data models into a single common data model (also called a 1:many connector) so SaaS developers only need to understand the nuances of one connector provided by the unified API and integrate with multiple third party applications in half the time.
The primary aim of all integration is to ensure smooth and consistent data flow — from the source (3rd party app) to your app and back — at all moments.
We will discuss different data sync models adopted by Finch API and Knit API in the next section.
Every SaaS company knows that maintaining existing integrations takes more time and engineering bandwidth than the monumental task of building integrations itself. Which is why most SaaS companies today are looking for unified API solutions with an integration management dashboards — a central place with the health of all live integrations, any issues thereon and possible resolution with RCA. This enables the customer success teams to fix any integration issues then and there without the aid of engineering team.
.png)
For any unified API, data sync is a two-fold process —
.png)
First of all, to make any data exchange happen, the unified API needs to read data from the source app (in this case the 3rd party app your customer already uses).
However, this initial data syncing also involves two specific steps — initial data sync and subsequent delta syncs.
Initial data sync is what happens when your customer authenticates and authorizes the unified API platform (let’s say Finch API in this case) to access their data from the third party app while onboarding Finch.
Now, upon getting the initial access, for ease of use, Finch API copies and stores this data in their server. Most unified APIs out there use this process of copying and storing customer data from the source app into their own databases to be able to run the integrations smoothly.
While this is the common practice for even the top unified APIs out there, this practice poses multiple challenges to customer data safety (we’ll discuss this later in this article). Before that, let’s have a look at delta syncs.
Delta syncs, as the name suggests, includes every data sync that happens post initial sync as a result of changes in customer data in the source app.
For example, if a customer of Finch API is using a payroll app, every time a payroll data changes — such as changes in salary, new investment, additional deductions etc — delta syncs inform Finch API of the specific change in the source app.
There are two ways to handle delta syncs — webhooks and polling.
In both the cases, Finch API serves via its stored copy of data (explained below)
In the case of webhooks, the source app sends all delta event information directly to Finch API as and when it happens. As a result of that “change notification” via the webhook, Finch changes its copy of stored data to reflect the new information it received.
Now, if the third party app does not support webhooks, Finch API needs to set regular intervals during which it polls the entire data of the source application to create a fresh copy. Thus, making sure any changes made to the data since the last polling is reflected in its database. Polling frequency can be every 24 hours or less.
This data storage model could pose several challenges for your sales and CS team where customers are worried about how the data is being handled (which in some cases is stored in a server outside of customer geography). Convincing them otherwise is not so easy. Moreover, this friction could result in additional paperwork delaying the time to close a deal.
The next step in data sync strategy is to use the user data sourced from the third party app to run your business logic. The two most popular approaches for syncing data between unified API and SaaS app are — pull vs push.
.png)
Pull model is a request-driven architecture: where the client sends the data request and then the server sends the data. If your unified API is using a pull-based approach, you need to make API calls to the data providers using a polling infrastructure. For a limited number of data, a classic pull approach still works. But maintaining polling infra and/making regular API calls for large amounts of data is almost impossible.

On the contrary, the push model works primarily via webhooks — where you subscribe to certain events by registering a webhook i.e. a destination URL where data is to be sent. If and when the event takes place, it informs you with relevant payload. In the case of push architecture, no polling infrastructure is to be maintained at your end.
There are 3 ways Finch API can interact with your SaaS application.
Knit is the only unified API that does NOT store any customer data at our end.
Yes, you read that right.
In our previous HR tech venture, we faced customer dissatisfaction over data storage model (discussed above) firsthand. So, when we set out to build Knit Unified API, we knew that we must find a way so SaaS businesses will no longer need to convince their customers of security. The unified API architecture will speak for itself. We built a 100% events-driven webhook architecture. We deliver both the initial and delta syncs to your application via webhooks and events only.
The benefits of a completely event-driven webhook architecture for you is threefold —
For a full feature-by-feature comparison, see our Knit vs Finch comparison page →
Let’s look at the other components of the unified API (discussed above) and what Knit API and Finch API offers.
Knit’s auth component offers a Javascript SDK which is highly flexible and has a wider range of use cases than Reach/iFrame used by the Finch API for front-end. This in turn offers you more customization capability on the auth component that your customers interact with while using Knit API.
The Knit API integration dashboard doesn’t only provide RCA and resolution, we go the extra mile and proactively identify and fix any integration issues before your customers raises a request.
Knit provides deep RCA and resolution including ability to identify which records were synced, ability to rerun syncs etc. It also proactively identifies and fixes any integration issues itself.
In comparison, the Finch API customer dashboard doesn’t offer as much deeper analysis, requiring more work at your end.
Wrapping up, Knit API is the only unified API that does not store customer data at our end, and offers a scalable, secure, event-driven push data sync architecture for smaller as well as larger data loads.
By now, if you are convinced that Knit API is worth giving a try, please click here to get your API keys. Or if you want to learn more, see our docs

Finch is a leading unified API player, particularly popular for its connectors in the employment systems space, enabling SaaS companies to build 1: many integrations with applications specific to employment operations. This translates to the ease for customers to easily leverage Finch’s unified connector to integrate with multiple applications in HRIS and payroll categories in one go. Invariably, owing to Finch, companies find connecting with their preferred employment applications (HRIS and payroll) seamless, cost-effective, time-efficient, and overall an optimized process. While Finch has the most exhaustive coverage for employment systems, it's not without its downsides - most prominent being the fact that a majority of the connectors offered are what Finch calls “assisted” integrations. Assisted essentially means a human-in-the-loop integration where a person has admin access to your user's data and is manually downloading and uploading the data as and when needed. Another one being that for most assisted integrations you can only get information once in a week which might not be ideal if you're building for use cases that depend on real time information.
● Ability to scale HRIS and payroll integrations quickly
● In-depth data standardization and write-back capabilities
● Simplified onboarding experience within a few steps
● Most integrations are assisted(human-assisted) instead of being true API integrations
● Integrations only available for employment systems
● Not suitable for realtime data syncs
● Limited flexibility for frontend auth component
● Requires users to take the onus for integration management
Pricing: Starts at $35/connection per month for read only apis; Write APIs for employees, payroll and deductions are available on their scale plan for which you’d have to get in touch with their sales team.
Now let's look at a few alternatives you can consider alongside finch for scaling your integrations

Knit is a leading alternative to Finch, providing unified APIs across many integration categories, allowing companies to use a single connector to integrate with multiple applications. Here’s a list of features that make Knit a credible alternative to Finch to help you ship and scale your integration journey with its 1:many integration connector:
Pricing: Starts at $2400 Annually
● Wide horizontal and deep vertical coverage: Knit not only provides a deep vertical coverage within the application categories it supports, like Finch, however, it also supports a wider horizontal coverage of applications, higher than that of Finch. In addition to applications within the employment systems category, Knit also supports a unified API for ATS, CRM, e-Signature, Accounting, Communication and more. This means that users can leverage Knit to connect with a wider ecosystem of SaaS applications.
● Events-driven webhook architecture for data sync: Knit has built a 100% events-driven webhook architecture, which ensures data sync in real time. This cannot be accomplished using data sync approaches that require a polling infrastructure. Knit ensures that as soon as data updates happen, they are dispatched to the organization’s data servers, without the need to pull data periodically. In addition, Knit ensures guaranteed scalability and delivery, irrespective of the data load, offering a 99.99% SLA. Thus, it ensures security, scale and resilience for event driven stream processing, with near real time data delivery.
● Data security: Knit is the only unified API provider in the market today that doesn’t store any copy of the customer data at its end. This has been accomplished by ensuring that all data requests that come are pass through in nature, and are not stored in Knit’s servers. This extends security and privacy to the next level, since no data is stored in Knit’s servers, the data is not vulnerable to unauthorized access to any third party. This makes convincing customers about the security potential of the application easier and faster.
● Custom data models: While Knit provides a unified and standardized model for building and managing integrations, it comes with various customization capabilities as well. First, it supports custom data models. This ensures that users are able to map custom data fields, which may not be supported by unified data models. Users can access and map all data fields and manage them directly from the dashboard without writing a single line of code. These DIY dashboards for non-standard data fields can easily be managed by frontline CX teams and don’t require engineering expertise.
● Sync when needed: Knit allows users to limit data sync and API calls as per the need. Users can set filters to sync only targeted data which is needed, instead of syncing all updated data, saving network and storage costs. At the same time, they can control the sync frequency to start, pause or stop sync as per the need.
● Ongoing integration management: Knit’s integration dashboard provides comprehensive capabilities. In addition to offering RCA and resolution, Knit plays a proactive role in identifying and fixing integration issues before a customer can report it. Knit ensures complete visibility into the integration activity, including the ability to identify which records were synced, ability to rerun syncs etc.
● No-Human in the loop integrations
● No need for maintaining any additional polling infrastructure
● Real time data sync, irrespective of data load, with guaranteed scalability and delivery
● Complete visibility into integration activity and proactive issue identification and resolution
● No storage of customer data on Knit’s servers
● Custom data models, sync frequency, and auth component for greater flexibility
See the full Knit vs Finch comparison →

Another leading contender in the Finch alternative for API integration is Merge. One of the key reasons customers choose Merge over Finch is the diversity of integration categories it supports.
Pricing: Starts at $7800/ year and goes up to $55K
● Higher number of unified API categories; Merge supports 7 unified API categories, whereas Finch only offers integrations for employment systems
● Supports API-based integrations and doesn’t focus only on assisted integrations (as is the case for Finch), as the latter can compromise customer’s PII data
● Facilitates data sync at a higher frequency as compared to Finch; Merge ensures daily if not hourly syncs, whereas Finch can take as much as 2 weeks for data sync
● Requires a polling infrastructure that the user needs to manage for data syncs
● Limited flexibility in case of auth component to customize customer frontend to make it similar to the overall application experience
● Webhooks based data sync doesn’t guarantee scale and data delivery

Workato is considered another alternative to Finch, albeit in the traditional and embedded iPaaS category.
Pricing: Pricing is available on request based on workspace requirement; Demo and free trial available
● Supports 1200+ pre-built connectors, across CRM, HRIS, ticketing and machine learning models, facilitating companies to scale integrations extremely fast and in a resource efficient manner
● Helps build internal integrations, API endpoints and workflow applications, in addition to customer-facing integrations; co-pilot can help build workflow automation better
● Facilitates building interactive workflow automations with Slack, Microsoft Teams, with its customizable platform bot, Workbot
However, there are some points you should consider before going with Workato:
● Lacks an intuitive or robust tool to help identify, diagnose and resolve issues with customer-facing integrations themselves i.e., error tracing and remediation is difficult
● Doesn’t offer sandboxing for building and testing integrations
● Limited ability to handle large, complex enterprise integrations
Paragon is another embedded iPaaS that companies have been using to power their integrations as an alternative to Finch.

Pricing: Pricing is available on request based on workspace requirement;
● Significant reduction in production time and resources required for building integrations, leading to faster time to market
● Fully managed authentication, set under full sets of penetration and testing to secure customers’ data and credentials; managed on-premise deployment to support strictest security requirements
● Provides a fully white-labeled and native-modal UI, in-app integration catalog and headless SDK to support custom UI
However, a few points need to be paid attention to, before making a final choice for Paragon:
● Requires technical knowledge and engineering involvement to custom-code solutions or custom logic to catch and debug errors
● Requires building one integration at a time, and requires engineering to build each integration, reducing the pace of integration, hindering scalability
● Limited UI/UI customization capabilities
Tray.io provides integration and automation capabilities, in addition to being an embedded iPaaS to support API integration.

Pricing: Supports unlimited workflows and usage-based pricing across different tiers starting from 3 workspaces; pricing is based on the plan, usage and add-ons
● Supports multiple pre-built integrations and automation templates for different use cases
● Helps build and manage API endpoints and support internal integration use cases in addition to product integrations
● Provides Merlin AI which is an autonomous agent to build automations via chat interface, without the need to write code
However, Tray.io has a few limitations that users need to be aware of:
● Difficult to scale at speed as it requires building one integration at a time and even requires technical expertise
● Data normalization capabilities are rather limited, with additional resources needed for data mapping and transformation
● Limited backend visibility with no access to third-party sandboxes
We have talked about the different providers through which companies can build and ship API integrations, including, unified API, embedded iPaaS, etc. These are all credible alternatives to Finch with diverse strengths, suitable for different use cases. Undoubtedly, the number of integrations supported within employment systems by Finch is quite large, there are other gaps which these alternatives seek to bridge:
● Knit: Providing unified apis for different categories, supporting both read and write use cases. A great alternative which doesn’t require a polling infrastructure for data sync (as it has a 100% webhooks based architecture), and also supports in-depth integration management with the ability to rerun syncs and track when records were synced.
● Merge: Provides a greater coverage for different integration categories and supports data sync at a higher frequency than Finch, but still requires maintaining a polling infrastructure and limited auth customization.
● Workato: Supports a rich catalog of pre-built connectors and can also be used for building and maintaining internal integrations. However, it lacks intuitive error tracing and remediation.
● Paragon: Fully managed authentication and fully white labeled UI, but requires technical knowledge and engineering involvement to write custom codes.
● Tray.io: Supports multiple pre-built integrations and automation templates and even helps in building and managing API endpoints. But, requires building one integration at a time with limited data normalization capabilities.
Thus, consider the following while choosing a Finch alternative for your SaaS integrations:
● Support for both read and write use-cases
● Security both in terms of data storage and access to data to team members
● Pricing framework, i.e., if it supports usage-based, API call-based, user based, etc.
● Features needed and the speed and scope to scale (1:many and number of integrations supported)
Depending on your requirements, you can choose an alternative which offers a greater number of API categories, higher security measurements, data sync (almost in real time) and normalization, but with customization capabilities.
Our detailed guides on the integrations space
.png)
The average company now runs more than 130 SaaS applications — and that number keepsclimbing. Each new tool promises efficiency, but also adds another data silo your teams have towork around manually.
SaaS integration is how you connect those tools: letting them share data automatically, trigger each other's workflows, and cut out the manual handoffs that slow teams down and introduce errors. But "SaaS integration" covers a wide range of use cases — from internal automation betweenyour own tools, to building customer-facing integration products that your own users canconfigure. The right approach depends on what you're trying to solve.
This guide breaks down what SaaS integration actually means, the different architecturesavailable, how to choose the right approach for your situation, and what to watch out for alongthe way
SaaS integration is the process of connecting separate SaaS applications so they can share data, trigger each other’s workflows, and automate repetitive tasks. This connectivity can be:
At its core, SaaS integration often involves using APIs (Application Programming Interfaces) to ensure data can move between apps in real time. As companies add more and more SaaS tools, integration is no longer a luxury—it's a necessity for efficiency and scalability.
Most SaaS integration content lumps all use cases together,but the two categories operate differently and require different tooling.
These connect the tools your own team uses. Examples: syncingyour CRM with your marketing automation platform, pushing invoices from yourbilling tool into your ERP, or triggering onboarding workflows when a new hireis added to your HRIS.
The goal is operational efficiency — reducing manual dataentry, eliminating duplicate records, and keeping systems in sync without humanintervention.
The right tools here are typically iPaaS platforms (Zapier, Workato, Make) or custom scripts maintained by your engineering team.
These are integrations you build into your own product so yourcustomers can connect it with the tools they use. If you're building a SaaSproduct and your customers ask things like "does this connect withSalesforce?" or "can we sync this with our HRMS?" — you're incustomer-facing integration territory.
The stakes are different here. You're not automating aninternal workflow — you're building a feature that sits inside your product andneeds to work reliably for many different customers across many different toolconfigurations.
The right tools for this are embedded iPaaS solutions orunified API platforms (more on these in Section 6).
How you connect SaaS tools matters as much as which tools youconnect. There are three dominant architecture patterns, each with differentscalability and maintenance tradeoffs.
Each application is directly connected to every otherapplication it needs to talk to. Simple to set up for two or three tools. Turnsinto a maintenance nightmare as the number of integrations grows — adding onenew tool requires N new connections to every other tool already in the network.
Best for: small teams with very few tools to connect, orone-off data migrations.
All data flows through a central platform — the"hub" — that manages routing, transformation, and error handling.Adding a new tool means connecting it once to the hub, not to every otherapplication.
This is how most enterprise iPaaS solutions work. It scaleswell for internal workflows but requires the hub to understand every dataformat and transformation rule.
Best for: medium-to-large businesses managing complex internalworkflows across many departments.
Rather than connecting directly to each third-party API, youintegrate once with a unified API layer that normalises data across manyproviders. One integration to Knit's unified API, for example, gives you accessto dozens of HRMS, ATS, or CRM tools through a single consistent data model.
This is particularly powerful for customer-facingintegrations, where you need to support many different customer toolconfigurations without writing one connector per tool.
Best for: SaaS companies building customer-facing integrationsat scale.
With the explosive growth of SaaS, SaaS integrations are now more important than ever. Below are some of the top reasons companies invest heavily in SaaS integrations:
Here are a few real-world ways SaaS integrations can transform businesses:
Automatically sync employee data — new hires, promotions,salary changes, departures — from your HRIS to your payroll system. Eliminatesmanual re-entry of compensation, leave balances, and benefits, reducing payrollerrors and compliance risk.
When a candidate is marked as hired in your ATS, automaticallycreate their employee profile in your HRIS and trigger onboarding workflows.The new hire arrives on Day 1 with access, documentation, and a structuredonboarding plan already in place.
Sync lead activity between your marketing automation platform(HubSpot, Marketo) and your CRM (Salesforce, HubSpot CRM). Sales reps seereal-time engagement data — email opens, form fills, page views — withouttoggling between tools.
Automatically generate a contract in DocuSign or Ironclad whena deal is marked "Closed Won" in your CRM. Contract metadata flowsback once signed, keeping your CRM records accurate without manual updates.
When a new hire is added to your HRIS, automatically provisiontheir accounts in Google Workspace, Slack, and any other tools they need.Reverses on offboarding: deprovision access across all systems the momentthey're marked as departed.
Sync orders, inventory, and revenue data between yourstorefront (Shopify, WooCommerce) and your accounting or ERP system (NetSuite,QuickBooks). Eliminates end-of-month reconciliation work and keeps yourfinancial reporting current.
Connect your support platform (Zendesk, Intercom) with your CRM so support agents see full customer history and deal status without leavingtheir helpdesk. Customer success teams can trigger support tickets directlyfrom CRM deal records.
Push product usage events from your SaaS application into your CDP or CRM (Segment, Amplitude). Sales and success teams see which features customers are actually using, enabling better expansion conversations andearlier churn detection.
Reflect salary changes, life events, or new hires from yourHRIS to your benefits platform automatically. Employees' benefit selections,coverage, and premiums stay accurate without HR having to manually update twosystems.
Despite the clear advantages, integrating SaaS apps can be complicated. Here are some challenges to watch out for:
Depending on your goals, your team size, and the complexity of the integrations, you’ll have to decide whether to develop integrations in-house or outsource to third-party solutions.
The answer often depends on whether you're building internalor customer-facing integrations. For internal workflows, building in-house isoften viable for the first few connections. But if you're buildingcustomer-facing integrations into your product, the "buy" case isalmost always stronger — the long-tail maintenance of hundreds of customerconfigurations at different API versions is a full-time engineering commitmentthat rarely makes sense to own.
Multiple categories of third-party SaaS integration platforms exist to help you avoid building everything from scratch. While iPaaS tools are best suited for internal enterprise workflow automations, embedded iPaaS tools which encompass embedded workflow tools and Unified API platforms are best suited for customer facing integrations offerings of SaaS tools or AI agents:
If you’re ready to implement SaaS integrations, here’s a simplified roadmap:
To ensure your integrations are robust and future-proof, follow these guiding principles:
1. AI-Powered Integrations
Generative AI will reshape how integrations are built, potentially automating much of the dev work to accelerate go-live times.
2. Verticalized Solutions
Industry-specific integration packs will make it even easier for specialized SaaS providers (e.g., healthcare, finance) to connect relevant tools in their niche.
3. Heightened Security and Privacy
As data regulations tighten worldwide, expect solutions that offer near-zero data storage (to reduce breach risk) and continuous compliance checks.
4. Integrations as a core product feature, not an afterthought
The SaaS companies gaining the most ground on retention arethe ones where integrations feel native — not bolted on. Customers increasinglyevaluate tools partly on how well they fit into their existing stack. Productsthat offer wide, reliable, maintained integration coverage reduce switchingcosts and become harder to replace. Expect "integration quality" tobecome a standard feature category in SaaS buying decisions, not just acheckbox.
API integration refers specifically to connecting systems viatheir APIs — the technical mechanism. SaaS integration is broader: it describesthe process of connecting SaaS applications so they share data and triggerworkflows, which usually happens through APIs but can also involve webhooks,file-based syncs, or middleware platforms. All SaaS integrations typically useAPIs, but not all API integrations involve SaaS tools.
Internal integrations connect the tools your own team uses —syncing your CRM with your marketing platform, for example. Customer-facingintegrations are built into your SaaS product so your customers can connect itwith the tools they already use. The two require different approaches: internalintegrations are usually handled by iPaaS tools, while customer-facingintegrations need embedded iPaaS solutions or unified API platforms that canscale across many customer configurations.
A unified API is a single API layer that normalises dataacross multiple SaaS providers in the same category. Instead of building oneconnector to Workday, another to BambooHR, another to Rippling — all withdifferent data models and auth flows — you integrate once with a unified APIand get access to all of them through a consistent schema. Unified APIs aremost valuable for SaaS companies building customer-facing integrations, whereyou need to support many different customer tool configurations without proportionallyincreasing engineering effort.
The three main patterns are: (1) Point-to-point, where eachapplication connects directly to every other application it needs to reach —simple for two tools, but complexity grows as N² as you add more. (2)Hub-and-spoke, where all data routes through a central platform that handlesrouting, transformation, and error handling — scalable for internal workflows.(3) Unified API, where a single integration unlocks access to many providers ina category through a normalised data model — best for customer-facingintegrations at scale.
If your goal is internal automation with minimal coding, aniPaaS solution like Zapier (for simple automations), Make (for more complexlogic), or Workato (for enterprise-grade workflows) covers most use cases. Formore complex data pipelines or custom business logic, you may need a customintegration layer. The key factors: number of tools you need to connect, howcomplex the data transformations are, and how much engineering bandwidth youcan dedicate to maintenance.
You have three main options: build native integrationsin-house (write custom code for each third-party API your customers use), usean embedded iPaaS platform (embed a pre-built integration layer into yourproduct), or use a unified API provider like Knit. For most SaaS teams, thebuild-in-house approach makes sense for the first one or two high-demandintegrations, but quickly becomes a maintenance burden as your customer baseand their tool diversity grows. Unified API and embedded iPaaS solutions let youscale customer-facing integrations without a proportional increase inengineering effort.
The biggest challenges are: (1) API inconsistency —third-party APIs have different authentication methods, data models, and ratelimits. (2) Ongoing maintenance — APIs change, get versioned, or getdeprecated, breaking integrations unexpectedly. (3) Data mapping complexity —getting data to flow correctly when field names and schemas differ betweensystems. (4) Security and compliance — sensitive data moving between systemsneeds encryption, access controls, and compliance with regulations like GDPR orSOC 2. (5) Engineering bandwidth — building and maintaining many integrationsin-house competes with your core product roadmap.
Key practices: use OAuth 2.0 for authentication whereversupported (avoid storing credentials directly), enforce HTTPS/TLS for all datain transit, minimise data storage — only retain what is necessary, and purge itwhen it's no longer needed. Choose integration vendors with SOC 2 Type II Certification and clear data processing agreements. Build in monitoring and alerting so you detect integration failures and unexpected data patterns quickly.
SaaS integration is how you make the tools in your stackactually work together — eliminating manual handoffs, reducing errors, andunlocking automation at scale.
The right approach depends on what you're integrating:
• For internal workflows: iPaaS platforms (Zapier,Workato, Make) cover most use cases without heavy engineering.
• For customer-facing integrations in your product:unified APIs or embedded iPaaS solutions scale significantly better thanbuilding connectors in-house.
• For architecture: unified API is the most maintainablepattern for SaaS companies that need to support many customer environments.
The companies that get this right — reliable, wide,well-maintained integrations — retain customers better and attract buyers whoare evaluating tools on how well they fit into an existing stack.
Knit is a unified API platform purpose-built for SaaS teamsthat need to offer deep integrations across HRMS, ATS, CRM, accounting, andticketing tools — without building and maintaining individual connectors foreach.
• One API integration → access to 50+ tools in eachcategory
• Normalised data models so you're not mapping eachprovider's schema yourself
• Pass-through architecture — data flows directly to your system, Knit doesn't store it
• Real-time sync with webhook support and a 99.9% uptime SLA
Used by product and engineering teams at companies who havemoved past the "build it ourselves" phase and want to scaleintegrations without scaling the engineering headcount to match.
See how Knit works → www.developers.getknit.dev or Schedule a 30-min demo

Modern software stacks run on API integrations. The average enterprise now operateshundreds of SaaS applications — HR, payroll, CRM, support, finance, recruiting — and makingthose applications share data reliably is one of the most persistent engineering challengesproduct teams face.When an integration breaks, sales teams lose pipeline visibility, payroll runs on stale headcountdata, and support tickets go unrouted. When integrations work well, they're invisible — andthat's exactly the point.This guide covers what API integration is, how it works, the different types, real-world examples,tools, costs, and how the unified API model is replacing point-to-point custom builds at scale.
API integration is the process of connecting two or more software applications through theirAPIs (Application Programming Interfaces) so they can exchange data automatically. Ratherthan requiring users to manually copy data between systems, API integration creates apersistent connection that keeps both systems in sync according to defined rules — withouthuman intervention.
Since the applications you use cannot achieve their full potential in silos, API integration ensures that they can establish a secure, reliable and scalable connection which prevents an unauthorized exchange of data, but enables them to talk to each other.
An API is the interface a software product exposes — it defines what data is available, how torequest it, and what format it returns. API integration is the practical implementation: the codeand architecture that uses that interface to connect two systems and keep them in sync.An API can exist without integration (a company publishes an API that nobody calls). Integrationcan exist without APIs (legacy EDI or file-based transfers). When you build a Workday-to-ADP payroll sync, you're building an API integration using both products' APIs.
Before we delve deeper into the benefits of API integration, how it works, etc. let’s quickly look at how APIs play an important role in the integration ecosystem for businesses. APIs enable businesses to reorganize and establish such a relationship which allows them to interact as per business needs. This allows companies to achieve a high level of integration at lower development costs. They essentially act as a connecting thread, which is critical for integration.
If you follow this API integration process, you can create API integrations in-house to support application connectivity and data exchange.
An API integration works by sending HTTP requests from onesystem to another's API endpoint, receiving a response, transforming the dataif needed, and writing it to the destination. In practice, most integrationsrun in one of two modes: polling (regularly checking the source for changes) orevent-driven (the source system sends a notification — a webhook — the momentsomething changes).
Here's a concrete example:
Salesforce (CRM) ↔ HubSpot (marketing automation)
A sales team uses Salesforce to manage leads and HubSpot torun email campaigns. Without integration, a rep who advances a lead to"Qualified" in Salesforce can't reach them with the right campaignuntil someone manually exports a CSV — typically once a week.
With API integration:
• A webhook in Salesforce fires when a lead's stagechanges to "Qualified"
• The integration layer receives the event and callsHubSpot's Contacts API to update the contact's lifecycle stage
• HubSpot's campaign automation picks up the change andenrols the lead in the correct nurture sequence within minutes
• Campaign engagement data (email opens, link clicks)flows back to Salesforce automatically, so the sales rep sees it before calling
The integration runs continuously, requires no manual stepsafter setup, and eliminates the lag and errors that come with weekly manualsyncs.
There are two dimensions to API integration types: theprotocol the APIs use, and the synchronisation pattern the integration follows.
REST accounts for the large majority of new SaaS APIintegrations. SOAP still appears in older enterprise systems — SAP, Oracle, andsome banking APIs. GraphQL is used by platforms like GitHub and Shopify whereclients need to specify exactly which fields to return. gRPC is primarily usedfor internal microservice communication rather than third-party productintegrations.
• Real-time (event-driven / webhooks): Data movesimmediately when something changes. A new hire added to Workday fires awebhook; the downstream system creates the employee record within seconds.Lowest latency, most reliable for critical workflows.
• Batch / scheduled sync: Data is pulled at regular intervals — hourly, nightly. Simpler to implement, acceptable for reporting and non-time-sensitive workflows.
• Bidirectional: Changes in either system propagate tothe other. Required for CRM ↔ support ticketing, where both teams update sharedrecords.
• Unidirectional: Data flows one way only. Typical forHRIS → payroll, where HR is the source of truth and payroll only reads from it.
The core process is consistent regardless of tools:
1. Define the data flow: What data moves, in whichdirection, and how often? Which system is the source of truth for each field?
2. Review API documentation: Understandauthentication (OAuth 2.0, API key, JWT), rate limits, pagination, and webhookavailability before writing code.
3. Map data fields: Field names rarely match acrosssystems. "employee_id" in one HRIS is "staff_code" inanother. Document mappings before coding.
4. Build and test authentication: OAuth flowsrequire careful handling — token expiry, refresh logic, and scope managementare the most common sources of silent integration failures.
5. Handle errors explicitly: Rate limit errors(429), auth failures (401), and temporary unavailability (503) each needspecific retry logic. Don't let failures fail silently.
6. Test with realistic volumes: An integration thatworks for 100 records may break at 100,000. Test pagination, batch limits, andtimeout behaviour before production.
7. Monitor continuously: API schemas change withoutnotice. Set alerts on error rate spikes, latency changes, and data volumedrops.
Pre-launch checklist:
• Auth flow tested including token refresh
• Rate limit handling implemented (429 responses +exponential backoff)
• Field mappings documented and validated with sampledata
• Error logging live before go-live
• Pagination tested with full dataset
• Webhook signature verification implemented
• Rollback plan documented
API integration is not simply about building and deployment, but involves constant maintenance and management. API integrations require comprehensive support at different levels.
First, you need to decide on a synchronisation model. Event-drivenwebhook integrations respond immediately to changes. Polling introduces latencyand wastes API quota on unchanged data. Where the source system supportswebhooks, use themd
Second, in terms of API integration management, you need to align on the data storage needs and how you seek to address them to store the volumes of data that are exchanged across applications.
Third, API integration management needs to ensure that any updates or upgrades to individual APIs are reflected in their integrations without disrupting the flow of work. Maintenance involves finding and updating changes in API schemas before anyone notices.
Finally, APIs can and do fail, which requires immediate error handling support and communication. Thus, API integration management is as important and engineering bandwidth as building and deployment and can impact the success of the overall integration experience and effectiveness.
The cost of an API integration essentially depends on the compensation for your engineering team that will be involved in building the API integration, the time they will take and whether or not the full access to the API for the application in question is available freely or comes at a price.
In case the API is freely available, the estimated cost of an API integration can be considered as the following. Generally, three resources from the engineering team are involved in building an API integration. A Developer at a compensation of 125K USD, a Product Manager at 100K USD and a QA Engineer at a salary of 80K USD. Each one of these apportions a segment of their time towards building an API integration.
Secondly, an API integration can take anywhere between 2 weeks to 3 months to build, averaging out at about four weeks for any API integration. In such a scenario, an API integration cost stands at 10K USD on an average, which can go higher if the time taken is more or if you need to hire an engineering team just for building integrations with higher compensation. Similarly, this will increase if the APIs come at a premium cost. You can multiply the average cost of one integration with the number of integrations your company uses to get the overall API integration cost for your business.
The hidden cost is maintenance. Integration maintenancetypically runs 15–20% of the original build cost annually — and that's assumingthe underlying APIs don't change significantly. A portfolio of 30 integrations,each built at $10K, carries a $45,000–$60,000 annual maintenance overhead evenbefore new build work is considered.
If you are just getting started in your API integration journey, there are specific lessons that you must learn to ensure that you are able to achieve the quality of integration you seek. Follow these practices to start your API integration learning:
While there are several ways businesses today are leading integrations between different applications they use, API integration has become one of the most popular ways, owing to the several benefits it brings for developers and business impact alike. Some of the top benefits of API integration include:
To begin with, API integrations significantly reduce the human effort and time your team might spend in connecting data between different applications. In the absence of API integration, your team members would have to manually update information across applications, leading to unnecessary efforts and wastage of time. Fortunately, with API integration, information between two applications, for instance, CRM and marketing software, can be directly updated, allowing your team members to focus on their functional competencies and expertise, instead of updating data and information. The interoperability brought along with API integration ensures that data is automatically exchanged, in real- time, leading to added efficiency.
A related benefit from the first one is the concern with manual errors. If one team member is expected to update several applications, there are chances of human error. Especially as and when the data becomes voluminous and has to be shared between multiple applications, it can lead to inaccuracies and inadequacies. However, with API integration, data exchange becomes accurate and free from human error, ensuring that all data exchanged is in usable condition and compatible to all applications involved.
API integrations help businesses leverage capabilities from other applications, while allowing them to focus on their core expertise. Conventionally, businesses focused on building everything in their application from scratch. However, with API integrations, they can rely on the complementary functions of other applications, while focusing on only building strengths. It relieves considerable engineering bandwidth and effort which can be used to develop core application features and functionalities.
When data is exchanged between applications, the usability of different features and benefits from different applications increase. As they have additional data from other applications, their potential to drive business benefits increase significantly. For instance, if you are using a marketing automation platform to run campaigns for your product. Now, if you get user data on how they are interacting with the product, how engaged they are and what their other expectations are, you can create a customized upselling pitch for them.
Thus, with API integration, data exchange not only makes business more smooth and efficient, but also helps you explore new business cases for the different applications that you have adopted, and at times, even identify new ways of creating revenue.
APIs have a strong security posture which protects them from threats, flaws and vulnerabilities. API integrations add a security layer with access controls which ensures that only specific employees have access to specific or sensitive data from other applications. API integration security is built upon measures of HTTP and supports Transport Layer Security (TLS) encryption or built-in protocols, Web Services Security. API integration can also help prevent security fraud that might occur during data exchange between two applications or if one application malfunctions.
With the help of token, encryption signatures, throttling and API gateways, API integration can help businesses securely exchange information and data between applications.
The right tooling depends on what you're building:integrations for your own team's workflows, or integrations you're deliveringto your customers as part of your product. The distinction matters because theplatforms designed for each are fundamentally different.
When to use iPaaS: Your goal is internal automation —connecting the tools your team uses. Zapier, Workato, and MuleSoft are fast toconfigure, cover thousands of connectors, and can be managed by non-engineeringteams.
When to use Unified API: You're a SaaS product and need tointegrate with all the HRIS, ATS, CRM, or payroll tools your customers use.Instead of building 30 separate integrations, you build once against theunified API and get coverage across the whole category. Knit provides this forHRIS, ATS, CRM, payroll, and ticketing — with an event-driven architecture anda pass-through model that doesn't store customer data.
In addition to the above mentioned benefits of API integrations, it is interesting to note that API integration has a positive impact on customer experience as well. There are multiple ways in which API integration can help businesses serve customers better, leading to greater stickiness, retention and positive branding. Here are a few ways in which API integration impacts customer experience:
By integrating data about customers from different sources, companies can customize the experience they provide. For instance, conversations with the sales team can be captured and shared for marketing campaigns which can exclusively focus on customer pain points rather than simply sharing all product USPs. At the same time, marketing campaigns can be directed towards customer purchase patterns to ensure customers see what they are interested in.
API integration ensures that customer data once collected can be shared between different departments of a company and the customer doesn’t have to interact with the business multiple times. This also ensures that there is no error in multiple data exchanges with the customers, leading to an accurate and streamlined manner of interaction. Thus, with API integration, customer interactions become more efficient and with reduced errors.
API integrations can help businesses penetrate into new markets and address customer demands better. Since they ensure that businesses don’t have to build new functionalities from scratch, they can enhance customer experience by focusing on their core capabilities and providing additional functionalities with API integration. Thus, API integration helps businesses meet the growing demands of customers to prevent churn or dissatisfaction with lack of functionalities.
API integration ensures that customers can access or exchange information between different applications easily without switching between applications. This significantly reduces the friction for customers and the time spent in toggling between different applications. Thus, a smooth customer experience that most expect ensues.
Now that you understand why API integrations are important, it is vital to see some of the top use cases for examples of API integration. Here, we have covered some areas in which API integrations are most commonly used:
Workday ↔ ADP: When a new employee is created in Workday,their compensation, department, and start date push to ADP automatically. Paychanges, terminations, and leave adjustments flow in real time — eliminatingthe weekly CSV uploads and the payroll errors they produce.
Greenhouse ↔ BambooHR: When a candidate is marked"Hired" in Greenhouse, an employee record is automatically created inBambooHR. The recruiter doesn't re-enter data. The new hire's Day 1 systemaccess can trigger immediately off the same event.
Salesforce ↔ HubSpot: Lead status changes in Salesforce updatethe HubSpot contact lifecycle, triggering the right nurture sequenceautomatically. Campaign engagement data — emails opened, links clicked — flowsback to Salesforce so sales reps have context before calling.
QuickBooks ↔ Stripe: Every payment processed in Stripe creates corresponding invoice in QuickBooks. Refunds and failed charges sync automatically. Month-end reconciliation that previously took hours now takesminutes.
Zendesk ↔ Salesforce: Support tickets in Zendesk are linked to CRM account records in Salesforce. When a ticket opens, the support agent seesthe account's full history — open deals, renewal date, previous tickets —without leaving their ticketing tool.
Shopify ↔ Warehouse Management System: Order data flows from Shopify to the WMS in real time. Inventory updates flow back to Shopify toprevent overselling. Returns trigger inventory adjustments automatically onboth sides.
AI agent ↔ HRIS via MCP: A growing pattern in 2026 is AIagents that call HRIS and CRM APIs — often through MCP (Model Context Protocol)servers — to retrieve context before executing tasks. An HR assistant agentmight pull an employee's leave balance, compensation history, and departmentfrom Workday before drafting a response to a benefits query. No human in theloop; the integration provides the live data the agent needs.
While API integrations have several benefits that can significantly help businesses and engineering teams, there are a few challenges along the way, which organizations need to address in the very beginning.
To begin with, not all applications provide all functionalities in their application for free to all users. While some might have an additional charge for API access, others might only provide APIs to customers above a certain pricing tier. Thus, managing 1:1 partnerships with different applications to access their APIs can be difficult and unsustainable as the number of applications you use increases.
When you are using API integrations, each component of your business is dependent on multiple applications. It is normal for APIs to fail or stop working once in a while. Factors such as uptime/ downtime, errors, latency, etc. can all lead to API failure. While individually, API failure may not have a big impact. However, when you have multiple applications connected, it can break the flow of work and disrupt business continuity. Especially, if you are offering API integrations along with your product to the client, API failure can lead to business disruption for them, resulting in a poor customer experience.
While most API integrations focus on facilitating data connectivity and exchange between applications, there might be a requirement from integrations to analyze the data from one application and filter it out for different fields/ understanding for the next application. However, simple or conventional API integration cannot achieve this, and this will require some external developer bandwidth to achieve the deep tech functionalities.
Each application or integration has its own data models, nuances and protocols, which are unique and mostly different from one another. Even within the same segment or category, like CRM, applications can have different syntax or schemas for the same data field. For instance, the lead name in one application can be Customer_id while for another it can be cust_id. This might require developers to learn data logic for each application, requiring unnecessary bandwidth.
Every custom integration is a maintenance obligation. APIs areupdated, endpoints deprecated, and authentication schemes changed — oftenwithout advance notice. A team running 10 custom integrations might absorb oneAPI change per month. A team running 50 is managing a full-time maintenancefunction. This is the primary reason product teams at scale move to integrationplatforms rather than maintaining in-house connections.
Developing API integrations in house can be quite expensive and resource intensive. First of all, finding the right developers to build API integrations for your use can be very difficult. Second, even if you are able to find someone, the process can take anywhere between a few weeks to a few months. That’s when the developer understands the logic of the application and API integration can take place. This high time consumption also comes at a cost for the time the developer spends on API integration. Since the salary of a developer can be anywhere between $80K to $125K, API integration development can cost 1000s of dollars for companies.
The story doesn’t end once an API integration is in place. APIs need to be maintained and continuously upgraded whenever an application updates itself. At the same time, as mentioned, APIs can fail. In such a situation, your non-technical teams will find it difficult to maintain the APIs, putting the reliance again on your developers, who might be required to fix any bugs. Thus, someone with technical knowledge of integration maintenance has to look over updates and other issues.
As the number of applications a business uses increases, as well as the APIs become more complex, with each one having its own set of peculiarities, there has been a rise of what we today call unified APIs. A unified API primarily normalizes data nuances and protocols from different APIs into one normalized data model from a similar category of applications, which organizations can use to integrate with applications that fall therein. It adds an additional abstraction layer on top of other APIs and data models.
One of the best use cases for unified API is when you are offering different integrations to your customers from a single segment. For instance, if you are providing your customers with the option to choose the CRM of their choice and integrate with your system, a unified API will help ensure that different CRM platforms like Salesforce, Zoho, Airtable, can all be connected via a single API and your developers don’t have to spend hours in finding and configuring APIs for each CRM. Some of the top unified API examples include:
Let’s quickly look at some of the key benefits that a unified API will bring along to manage API integrations for businesses:
Therefore, unified API is essentially a revolution in API integration, helping developers take out all the pain for integrating applications with API, where they only focus on reaping the benefits and developing core product functionalities.
Before we move on to the last section, it is important to check whether or not you are now able to answer the key API integration questions that might come in your mind. Some of the frequently asked API integration questions include:
API integration is the process of connecting two or moresoftware applications through their APIs so they can exchange dataautomatically. When a customer updates their status in your CRM, APIintegration can propagate that change to your support system and billingplatform without any manual intervention. The connection runs continuously,handles authentication, data transformation, and error recovery, and operatesaccording to defined rules.
API integrations vary by protocol and synchronisation pattern.By protocol: REST (most common in modern SaaS), SOAP (enterprise and legacysystems), GraphQL (flexible query APIs), and gRPC (high-performance internalservices). By sync pattern: real-time event-driven (webhooks), batch/scheduledpolling, bidirectional sync, and unidirectional sync. Most product integrationsuse REST over webhooks for real-time, bidirectional data exchange.
An API is the interface a software product exposes — itdefines what data is available, how to request it, and what format it returns.API integration is the practical implementation: the code and architecture thatuses that interface to connect two systems and keep them in sync. An API canexist without integration; integration requires a connection method (usuallyAPIs in modern SaaS).
The right tool depends on what you're building. For internalworkflow automation, iPaaS platforms like Zapier, Workato, or MuleSoft arefastest. For product teams building customer-facing integrations across acategory of tools (HRIS, ATS, CRM), unified API platforms like Knit, Merge, orFinch cover the whole category from a single integration point. Custom buildsmake sense for one-off integrations with highly specific requirements.
A simple integration typically costs $8,000–$15,000 inengineering time. A complex enterprise integration (bidirectional sync, legacysystems, custom data models) can reach $40,000–$80,000 or more. Ongoingmaintenance adds 15–20% annually. Teams building more than 10–15 integrationsusually find integration platforms more cost-effective than custom builds atscale.
Standard API integration is a point-to-point connectionbetween two specific systems — you build one integration for Workday, aseparate one for BambooHR, another for Personio. A unified API sits abovethose: it normalises the data models across all tools in a category and exposesa single API your code talks to. Build once, get coverage across the wholecategory. The unified API vendor maintains each underlying connector, so you'renot affected when Workday updates its API.
AI agents increasingly use API integrations — often throughMCP (Model Context Protocol) servers — to retrieve live context beforeexecuting tasks. An HR assistant agent answering a question about an employee'sleave balance needs a live call to the HRIS; a sales agent drafting a follow-upemail needs current CRM data. The integration layer handles authentication anddata retrieval; the agent handles reasoning and output. The event-driven,real-time nature of webhook-based integrations is particularly well-suited toagent workflows where stale data produces wrong answers.
As we draw this discussion to a close, it is important to note that the SaaS market and use of applications will see an exponential growth in the coming years. The SaaS market is expected to hit $716.52 billion by 2028. Furthermore, the overall spend per company on SaaS products is up by 50%. As companies will use more applications, the need for API integrations will continue to increase. Thus, it is important to keep in mind:
Thus, companies must focus on exploring the potential of APIs, especially for the top segment of products they routinely use, to make connectivity and exchange of data smooth and seamless between applications, leading to better productivity, data driven decision making and business success.
.png)
In our previous post, we introduced the Model Context Protocol (MCP) as a universal standard designed to bridge AI agents and external tools or data sources. MCP promises interoperability, modularity, and scalability. This helps solve the long-standing issue of integrating AI systems with complex infrastructures in a standardized way. But how does MCP actually work?
Now, let's peek under the hood to understand its technical foundations. This article will focus on the layers and examine the architecture, communication mechanisms, discovery model, and tool execution flow that make MCP a powerful enabler for modern AI systems. Whether you're building agent-based systems or integrating AI into enterprise tools, understanding MCP's internals will help you leverage it more effectively.
MCP follows a client-server model that enables AI systems to use external tools and data. Here's a step-by-step overview of how it works:
1. Initialization
When the Host application starts (for example, a developer assistant or data analysis tool), it launches one or more MCP Clients. Each Client connects to its Server, and they exchange information about supported features and protocol versions through a handshake.
2. Discovery
The Clients ask the Servers what they can do. Servers respond with a list of available capabilities, which may include tools (like fetch_calendar_events), resources (like user profiles), or prompts (like report templates).
3. Context Provision
The Host application processes the discovered tools and resources. It can present prompts directly to the user or convert tools into a format the language model can understand, such as JSON function calls.
4. Invocation
When the language model decides a tool is needed—based on a user query like “What meetings do I have tomorrow?”; the Host directs the relevant Client to send a request to the Server.
5. Execution
The Server receives the request (for example, get_upcoming_meetings), performs the necessary operations (such as calling a calendar API), and gathers the results.
6. Response
The Server sends the results back to the Client.
7. Completion
The Client passes the result to the Host. The Host integrates the new information into the language model’s context, allowing it to respond to the user with accurate, real-time data.
At the heart of MCP is a client-server architecture. It is a design choice that offers clear separation of concerns, scalability, and flexibility. MCP provides a structured, bi-directional protocol that facilitates communication between AI agents (clients) and capability providers (servers). This architecture enables users to integrate AI capabilities across applications while maintaining clear security boundaries and isolating concerns.
These are applications (like Claude Desktop or AI-driven IDEs) needing access to external data or tools. The host application:
For example, In Claude Desktop, the host might manage several clients simultaneously, each connecting to a different MCP server such as a document retriever, a local database, or a project management tool.
MCP Clients are AI agents or applications seeking to use external tools or retrieve contextually relevant data. Each client:
An MCP client is built using the protocol’s standardized interfaces, making it plug-and-play across a variety of servers. Once compatible, it can invoke tools, access shared resources, and use contextual prompts, without custom code or hardwired integrations.
MCP Servers expose functionality to clients via standardized interfaces. They act as intermediaries to local or remote systems, offering structured access to tools, resources, and prompts. Each MCP server:
Servers can wrap local file systems, cloud APIs, databases, or enterprise apps like Salesforce or Git. Once developed, an MCP server is reusable across clients, dramatically reducing the need for custom integrations (solving the “N × M” problem).
Local Data Sources: Files, databases, or services securely accessed by MCP servers
Remote Services: External internet-based APIs or services accessed by MCP servers
MCP uses JSON-RPC 2.0, a stateless, lightweight remote procedure call protocol over JSON. Inspired by its use in the Language Server Protocol (LSP), JSON-RPC provides:
Message Types
The MCP protocol acts as the communication layer between these two components, standardising how requests and responses are structured and exchanged. This separation offers several benefits, as it allows:
Request Format
When an AI agent decides to use an external capability, it constructs a structured request:
{
"jsonrpc": "2.0",
"method": "call_tool",
"params": {
"tool_name": "search_knowledge_base",
"inputs": {
"query": "latest sales figures"
}
},
"id": 1
}
Server Response
The server validates the request, executes the tool, and sends back a structured result, which may include output data or an error message if something goes wrong.
This communication model is inspired by the Language Server Protocol (LSP) used in IDEs, which also connects clients to analysis tools.
A key innovation in MCP is dynamic discovery. When a client connects to a server, it doesn't rely on hardcoded tool definitions. It allows clients to understand the capabilities of any server they connect to. It enables:
Initial Handshake: When a client connects to an MCP server, it initiates an initial handshake to query the server’s exposed capabilities. It goes beyond relying on pre-defined knowledge of what a server can do. The client dynamically discovers tools, resources, and prompts made available by the server. For instance, it asks the server: “What tools, resources, or prompts do you offer?”
{
"jsonrpc": "2.0",
"method": "discover_capabilities",
"id": 2
}
Server Response: Capability Catalog
The server replies with a structured list of available primitives:
This discovery process allows AI agents to learn what they can do on the fly, enabling plug-and-play style integration
This approach to capability discovery provides several significant advantages:
Once the AI client has discovered the server’s available capabilities, the next step is execution. This involves using those tools securely, reliably, and interpretably. The lifecycle of tool execution in MCP follows a well-defined, structured flow:
This flow ensures execution is secure, auditable, and interpretable, unlike ad-hoc integrations where tools are invoked via custom scripts or middleware. MCP’s structured approach provides:
MCP Servers are the bridge/API between the MCP world and the specific functionality of an external system (an API, a database, local files, etc.). Servers communicate with clients primarily via two methods:
Local (stdio) Mode
Remote (http) Mode
Regardless of the mode, the client’s logic remains unchanged. This abstraction allows developers to build and deploy tools with ease, choosing the right mode for their operational needs.
One of the most elegant design principles behind MCP is decoupling AI intent from implementation. In traditional architectures, an AI agent needed custom logic or prompts to interact with every external tool. MCP breaks this paradigm:
This separation unlocks huge benefits:
The Model Context Protocol is more than a technical standard, it's a new way of thinking about how AI interacts with the world. By defining a structured, extensible, and secure protocol for connecting AI agents to external tools and data, MCP lays the foundation for building modular, interoperable, and scalable AI systems.
Key takeaways:
As the ecosystem around AI agents continues to grow, protocols like MCP will be essential to manage complexity, ensure security, and unlock new capabilities. Whether you're building AI-enhanced developer tools, enterprise assistants, or creative AI applications, understanding how MCP works under the hood is your first step toward building robust, future-ready systems.
Yes, a single MCP client can connect to multiple servers, each offering different tools or services. This allows AI agents to function more effectively across domains. For example, a project manager agent could simultaneously use one server to access project management tools (like Jira or Trello) and another server to query internal documentation or databases.
JSON-RPC was chosen because it supports lightweight, bi-directional communication with minimal overhead. Unlike REST or GraphQL, which are designed around request-response paradigms, JSON-RPC allows both sides (client and server) to send notifications or make calls, which fits better with the way LLMs invoke tools dynamically and asynchronously. It also makes serialization of function calls cleaner, especially when handling structured input/output.
With MCP’s dynamic discovery model, clients don’t need pre-coded knowledge of tools or prompts. At runtime, clients query servers to fetch a list of available capabilities along with their metadata. This removes boilerplate setup and enables developers to plug in new tools or update functionality without changing client-side logic. It also encourages a more modular and composable system architecture.
Tool invocations in MCP are gated by multiple layers of control:
Versioning is built into the handshake process. When a client connects to a server, both sides exchange metadata that includes supported protocol versions, capability versions, and other compatibility information. This ensures that even as tools evolve, clients can gracefully degrade or adapt, allowing continuous deployment without breaking compatibility.
Yes. MCP is designed to be model-agnostic. Any AI model—whether it’s a proprietary LLM, open-source foundation model, or a fine-tuned transformer, can act as a client if it can construct and interpret JSON-RPC messages. This makes MCP a flexible framework for building hybrid agents or systems that integrate multiple AI backends.
Errors are communicated through structured JSON-RPC error responses. These include a standard error code, a message, and optional data for debugging. The Host or client can log, retry, or escalate errors depending on the severity and the use case, helping maintain robustness in production systems.
Curated API guides and documentations for all the popular tools
.webp)
NetSuite is a leading cloud-based Enterprise Resource Planning (ERP) platform that helps businesses manage finance, operations, customer relationships, and more from a unified system. Its robust suite of applications streamlines workflows automates processes and provides real-time data insights.
To extend its functionality, NetSuite offers a comprehensive set of APIs that enable seamless integration with third-party applications, custom automation, and data synchronization.
Learn all about the NetSuite API in our in-depth Nestuite API Guide
This article explores the NetSuite APIs, outlining the key APIs available, their use cases, and how they can enhance business operations.
Key Highlights of NetSuite APIs
The key highlights of NetSuite APIs are as follows:
These APIs empower developers to build custom solutions, automate workflows, and integrate NetSuite with external platforms, enhancing operational efficiency and business intelligence.
This article gives an overview of the most commonly used NetSuite API endpoints.
NetSuite API Endpoints
Here are the most commonly used NetSuite API endpoints:
Accounts
Accounting Book
Here’s a detailed reference to all the NetSuite API Endpoints.
NetSuite API FAQs
Here are the frequently asked questions about NetSuite APIs to help you get started:
NetSuite enforces concurrency limits rather than per-minute rate limits. Standard licences allow 10 concurrent web service requests; larger enterprise accounts may have higher limits. Exceeding the concurrency limit returns an EXCEEDED_CONCURRENCY_LIMIT_BY_INTEGRATION fault. SuiteQL REST API calls paginate at 1,000 rows per response — use the nextPageId parameter for larger datasets. Best practice is exponential backoff and request queuing rather than parallel firing.
NetSuite supports two authentication methods: Token-Based Authentication (TBA) for server-to-server integrations, and OAuth 2.0 (available from NetSuite 2022.2+) for user-facing flows. TBA requires a manually constructed HMAC-SHA256 signed Authorization header on every request — including realm, oauth_consumer_key, oauth_token, oauth_signature_method, oauth_timestamp, oauth_nonce, and oauth_signature. Basic authentication was fully deprecated. Knit handles TBA signature construction and token lifecycle management automatically.
The NetSuite REST API (SuiteQL) uses JSON payloads and is the recommended interface for new integrations — it supports SQL-like queries via POST to /services/rest/query/v1/suiteql. The SOAP API (SuiteTalk) uses XML and is the legacy interface, offering broader record coverage for complex transactions but slower to work with. New integrations should use the REST API unless the required record type is only available via SOAP.
NetSuite does not support native outbound webhooks. Real-time event notifications require either SuiteScript User Event scripts (server-side JavaScript that fires HTTP calls when records change) or Workflow Event Actions triggered by business process events. Most integrations use scheduled polling via SuiteQL with a lastmodifieddate filter. Knit provides virtual webhooks for NetSuite — subscribe to normalised change events and Knit handles polling, deduplication, and delivery.
SuiteScript is NetSuite's JavaScript-based API for custom business logic that runs server-side inside NetSuite. It supports User Event scripts (triggered by record creates/edits), Scheduled scripts (run on a timer), Client scripts (run in the browser UI), and RESTlets (custom REST endpoints hosted in NetSuite). SuiteScript is used for automation and write operations; SuiteQL is used for read operations from outside NetSuite.
Find more FAQs here.
Get started with NetSuite API
To access NetSuite APIs, enable API access in NetSuite, create an integration record to obtain consumer credentials, configure token-based authentication (TBA) or OAuth 2.0, generate access tokens, and use them to authenticate requests to NetSuite API endpoints.
However, if you want to integrate with multiple CRM, Accounting or ERP APIs quickly, you can get started with Knit, one API for all top integrations.
To sign up for free, click here. To check the pricing, see our pricing page.
.png)
Zoho Books is a robust cloud-based accounting software designed to streamline financial management for small and medium-sized businesses. As part of the comprehensive Zoho suite of business applications, Zoho Books offers a wide array of features that cater to diverse accounting needs. It empowers businesses to efficiently manage their financial operations, from invoicing and expense tracking to inventory management and tax compliance. With its user-friendly interface and powerful tools, Zoho Books simplifies complex accounting tasks, enabling businesses to focus on growth and profitability.
One of the standout features of Zoho Books is its ability to seamlessly integrate with various third-party applications through the Zoho Books API. This integration capability allows businesses to customize their accounting processes and connect Zoho Books with other essential business tools, enhancing productivity and operational efficiency. The Zoho Books API provides developers with the flexibility to automate workflows, synchronize data, and build custom solutions tailored to specific business requirements, making it an invaluable asset for businesses looking to optimize their financial management systems.
Answer: To retrieve a list of invoices, make a GET request to the /invoices endpoint:
bash
GET https://www.zohoapis.com/books/v3/invoices?organization_id=YOUR_ORG_ID
Zoho Books API access uses OAuth 2.0 — there is no separate "enable API" toggle. To get started: (1) Go to the Zoho Developer Console (api-console.zoho.com) and register a new client. (2) Select "Server-based Applications" for server-to-server integrations. (3) Note your Client ID and Client Secret. (4) Generate a grant token by directing users to Zoho's authorization URL with the required scopes (e.g., ZohoBooks.fullaccess.all). (5) Exchange the grant token for an access token and refresh token via POST to https://accounts.zoho.com/oauth/v2/token. Access tokens expire after 1 hour — use the refresh token to renew. The organization_id parameter is required on all API requests and can be retrieved from your Zoho Books settings.
The Zoho Books API v3 covers the full accounting data model. Key objects include: Invoices (create, update, approve, void, email, bulk export), Contacts (customers and vendors, with contact persons and addresses), Bills (accounts payable, with approval workflows), Bank Accounts and Bank Transactions (including categorization), Chart of Accounts, Customer Payments and Vendor Payments, Credit Notes and Vendor Credits, Estimates, Sales Orders, Purchase Orders, Expenses (including recurring), Journals, Items, Projects and Time Entries, and Settings (taxes, currencies, exchange rates). All objects support standard CRUD operations. Knit normalises Zoho Books objects into a unified accounting schema consistent with QuickBooks, Xero, NetSuite, and Sage Intacct.
For quick and seamless integration with Zohobooks API, Knit API offers a convenient solution. It’s AI powered integration platform allows you to build any Zohobooks API Integration use case. By integrating with Knit just once, you can integrate with multiple other CRMs, HRIS, Accounting, and other systems in one go with a unified approach. Knit takes care of all the authentication, authorization, and ongoing integration maintenance. This approach not only saves time but also ensures a smooth and reliable connection to Zohobooks API.
To sign up for free, click here. To check the pricing, see our pricing page.
.png)
Integrating AI agents into your enterprise applications unlocks immense potential for automation, efficiency, and intelligence. As we've discussed, connecting agents to knowledge sources (via RAG) and enabling them to perform actions (via Tool Calling) are key. However, the path to seamless integration is often paved with significant technical and operational challenges.
Ignoring these hurdles can lead to underperforming agents, unreliable workflows, security risks, and wasted development effort. Proactively understanding and addressing these common challenges is critical for successful AI agent deployment.
This post dives into the most frequent obstacles encountered during AI agent integration and explores potential strategies and solutions to overcome them.
Return to our main guide: The Ultimate Guide to Integrating AI Agents in Your Enterprise
AI agents thrive on data, but accessing clean, consistent, and relevant data is often a major roadblock.
Related: Unlocking AI Knowledge: A Deep Dive into Retrieval-Augmented Generation (RAG)]
Connecting diverse systems, each with its own architecture, protocols, and quirks, is inherently complex.
AI agents, especially those interacting with real-time data or serving many users, must be able to scale effectively.
Enabling agents to reliably perform actions via Tool Calling requires careful design and ongoing maintenance.
Related: Empowering AI Agents to Act: Mastering Tool Calling & Function Execution
Understanding what an AI agent is doing, why it's doing it, and whether it's succeeding can be difficult without proper monitoring.
Both the AI models and the external APIs they interact with are constantly evolving.
Integrating AI agents offers tremendous advantages, but it's crucial to approach it with a clear understanding of the potential challenges. Data issues, integration complexity, scalability demands, the effort of building actions, observability gaps, and compatibility drift are common hurdles. By anticipating these obstacles and incorporating solutions like strong data governance, leveraging unified API platforms or integration frameworks, implementing robust monitoring, and maintaining rigorous testing and version control practices, you can significantly increase your chances of building reliable, scalable, and truly effective AI agent solutions. Forewarned is forearmed in the journey towards successful AI agent integration.
Consider solutions that simplify integration: Explore Knit's AI Toolkit
The six most common challenges in AI agent integration are: data compatibility and schema mismatches, integration complexity across heterogeneous systems, scalability under concurrent agent workloads, building AI actions that call external APIs reliably, observability and monitoring gaps in multi-step agent pipelines, and versioning/compatibility drift as APIs and models update. Security and governance — ensuring agents access only scoped data and leave audit trails — is increasingly cited as a seventh challenge in enterprise deployments.
Traditional API integration connects a human-facing application to a data source on demand. AI agent integration requires the agent to autonomously decide which APIs to call, in what sequence, with what parameters — often across multiple systems in a single task. This introduces failure modes that don't exist in direct integrations: hallucinated API calls, cascading errors across tool chains, and unpredictable retry behaviour under rate limits. The agent's non-determinism is what makes integration significantly harder to test and debug than conventional software.
Data compatibility issues arise when agents pull structured data from multiple sources — CRMs, ERPs, HRIS — with different schemas for the same entity (e.g., "customer ID" vs. "contact_id"). The solution is a normalisation layer that maps each source's schema to a unified model before the agent sees the data. Without this, agents must handle schema variations in the prompt, which degrades reliability. Knit's unified API normalises data from 100+ tools into a consistent schema so agents always work with predictable field names and types.
The biggest security risk is over-permissioned tool access — agents granted broad API credentials that allow them to read or write far more data than any given task requires. If an agent is compromised or misbehaves, over-permissioned access can lead to data exfiltration or unintended writes across systems. The mitigation is scoped, task-level permissions: each agent should be granted only the minimum access needed for its specific workflow, with full audit logging of every API call made.
AI agent pipelines are harder to observe than traditional software because failures are often non-deterministic — the same input can produce different tool call sequences on different runs. Effective monitoring requires structured logging at the tool call level (not just the final output), distributed tracing across multi-step workflows, and alerting on anomalies like unexpected tool invocations or repeated retries. OpenTelemetry-compatible instrumentation is the current standard for agent observability in production.
AI agent integrations break when upstream APIs change field names, deprecate endpoints, or alter authentication flows without warning. The mitigation strategy has three layers: pin integrations to a specific API version rather than the latest, monitor vendor changelogs and deprecation notices, and abstract external API calls behind an internal interface so changes only require updating one place. Knit manages API versioning for all connected tools, so agent integrations don't break when a source system updates its API.